---
title: "Using Next.js and Auth0 with Supabase"
description: "Learn how to integrate Auth0 authentication with database storage and row-level security authorization in Supabase."
authors:
- name: "Jon Meyers"
url: "https://auth0.com/blog/authors/jon-meyers/"
date: "May 19, 2023"
category: "Developers,Tutorial,Next.js"
tags: ["supabase", "nextjs", "auth0"]
url: "https://auth0.com/blog/using-nextjs-and-auth0-with-supabase/"
---
# Using Next.js and Auth0 with Supabase
## Overview
In this article, we are going to explore using [Next.js](https://nextjs.org/), [Auth0](https://auth0.com/), and [Supabase](https://supabase.com/) to build a classic Todo app. Each user will only be able to see their own todos, so we will need to implement authentication, authorization, and a database.
This article will cover the following:
- configuring Auth0, Next.js, and Supabase to work together seamlessly
- using the `nextjs-auth0` library for authentication
- implementing Row Level Security (RLS) policies for authorization
- what a JWT is and how to sign our own
- using PostgreSQL Functions to extract values from a JWT
The final version of the Todo app code can be found [here](https://github.com/dijonmusters/auth0-supabase-2023).
## Prerequisites
This article does not assume prior experience with any of these technologies; however, you will need [Node.js](https://nodejs.org/en/download/) installed to follow along. In addition, plan to have accounts for the managed services in the section below (Auth0 and Supabase). Both are free as of this writing and don't require a credit card.
## Stack
**Next.js** is a React framework that makes building efficient web apps super easy. It also gives us the ability to write server-side logic — which we will need to ensure our application is secure — without needing to maintain our own server.
**Auth0** is an authentication and authorization solution that makes managing users and securing applications a breeze. It is an extremely battle-tested and mature solution for auth.
**Supabase** is an open-source backend-as-a-service, which makes it possible to build an application in a weekend and scale to millions. It is a convenient wrapper around a collection of open-source tools that enable database storage, file storage, authentication, authorization, and real-time subscriptions. While these are all great features, this article will only use database storage and authorization.
"Wait, if Supabase handles auth, why are we using Auth0?"
One of the real strengths of Supabase is the lack of vendor lock-in. Maybe you already have users in Auth0, your company has a lot of experience with it, or you're interacting with other applications that use it. Any of the Supabase components can be swapped out for a similar service and hosted anywhere.
So let's do just that!
## Auth0
The first thing we need to do is sign up for a free account with [Auth0](https://auth0.com/). Once at the dashboard, we need to create a new `Tenant` for our project.
> A tenant is a way of isolating our users and settings from other applications we have with Auth0.
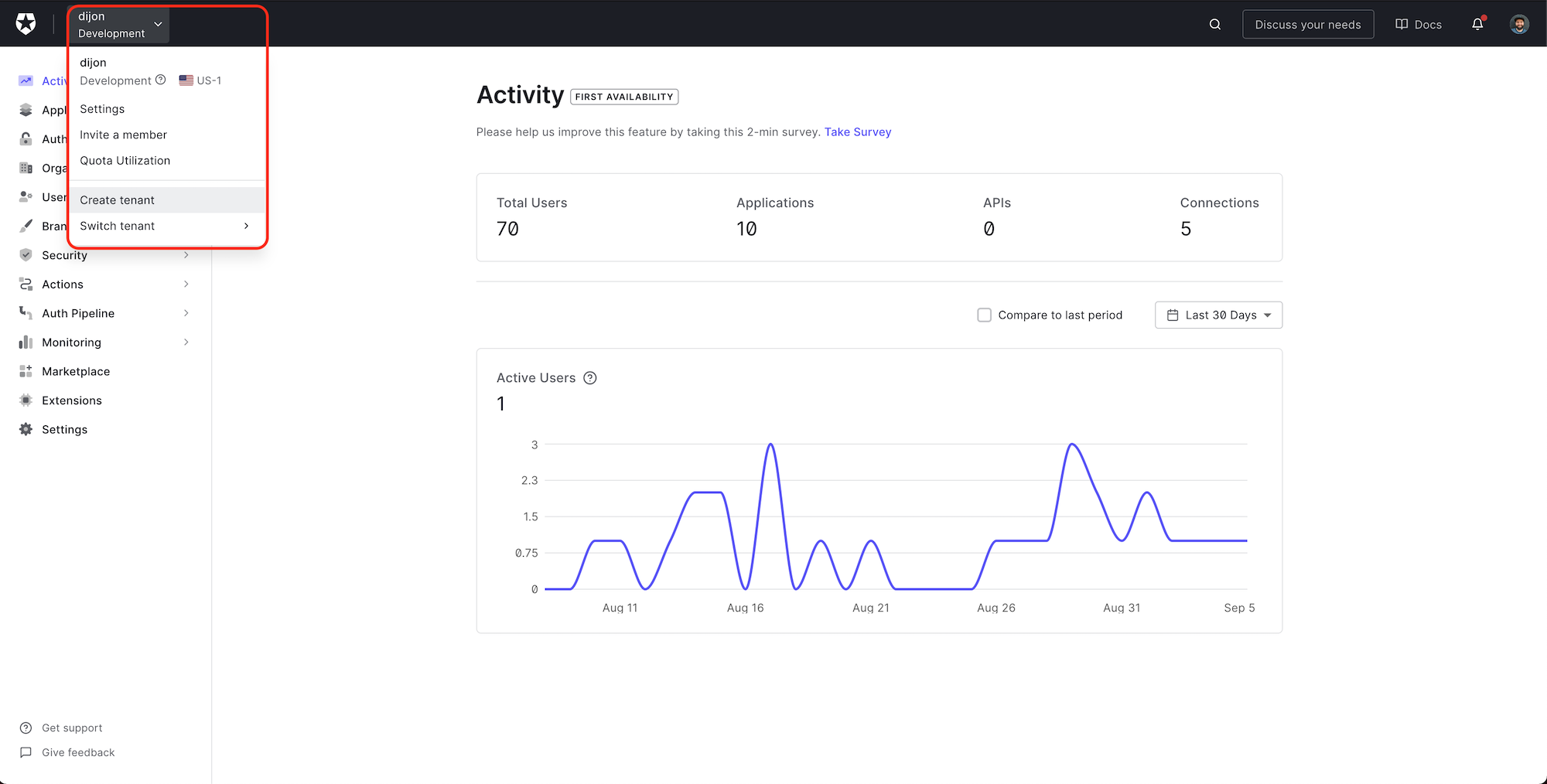
Click the name of your account in the top left, and then select `Create tenant` from the dropdown.
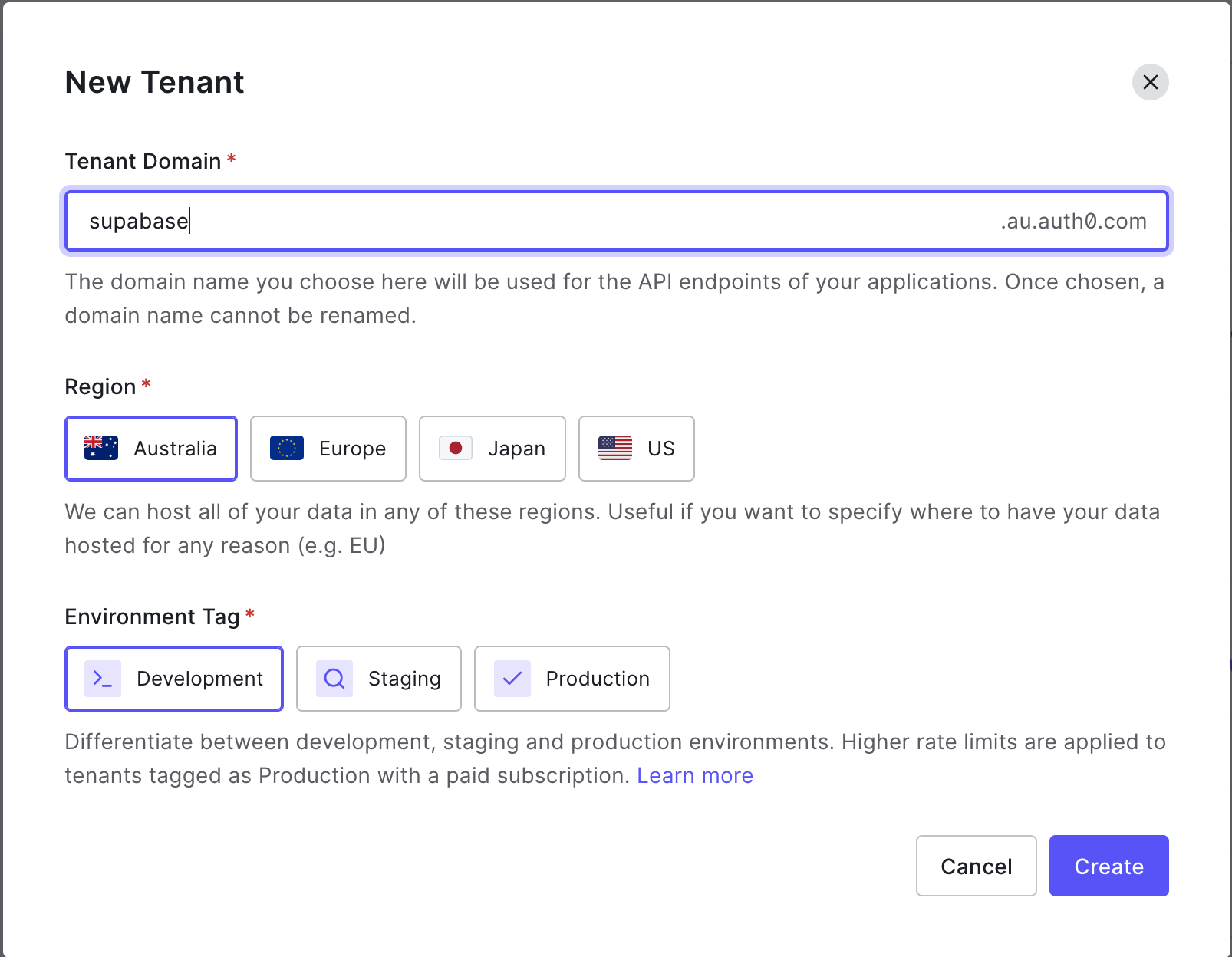
Give your tenant a unique `Domain`, set the `Region` closest to you, and leave the `Environment Tag` set to `Development`.
> In a production application, you want your region to be as close as possible to the majority of your users.
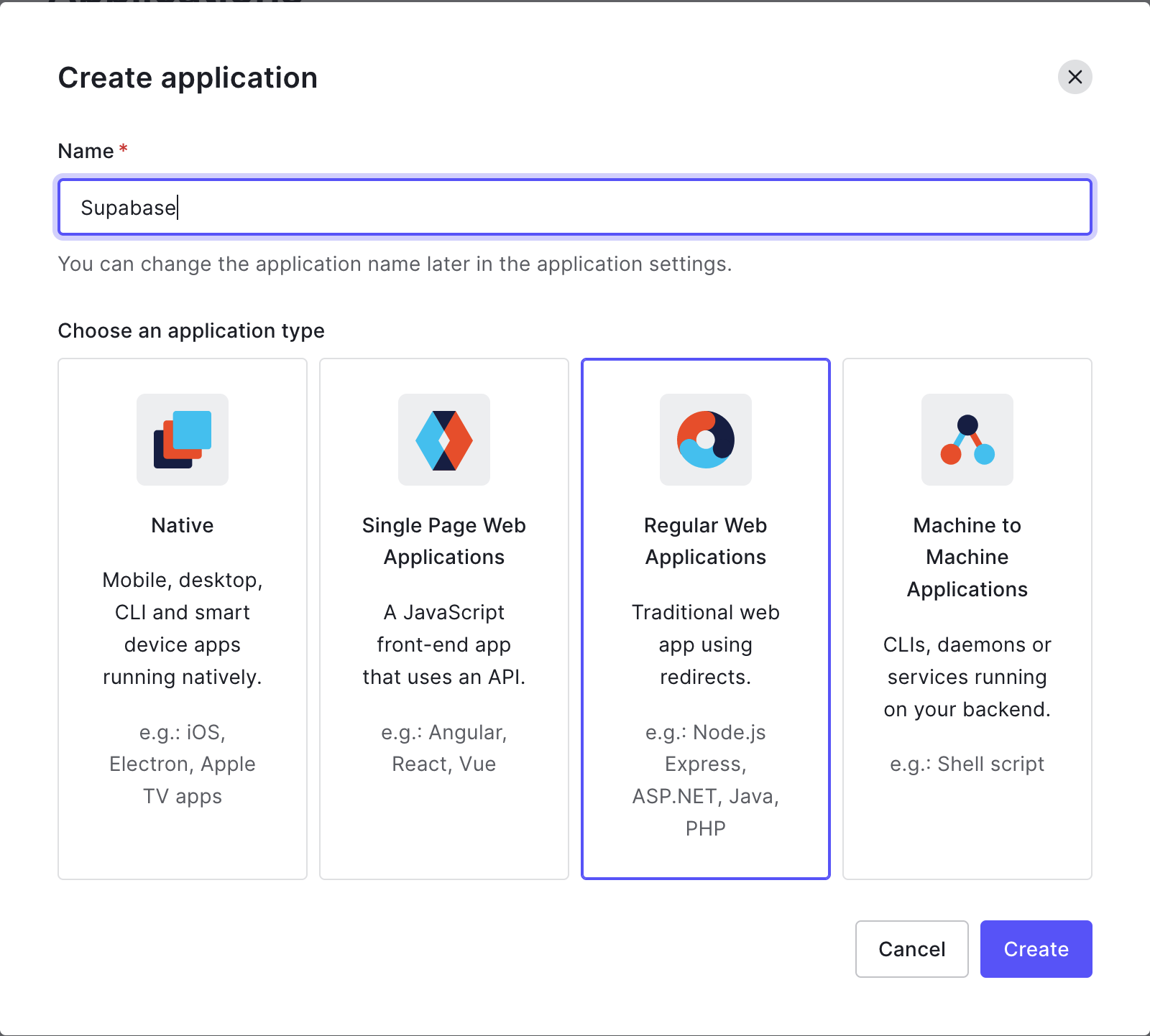
Next, we want to create an Application. Select `Applications` > `Applications` from the sidebar menu, and click `+ Create Application`. We want to give it a name (this can be the same as the Tenant) and select `Regular Web Applications`. Click `Create`.
From the application's page you are redirected to, select the `Settings` tab and scroll down to the `Application URIs` section.
Add the following:
`Allowed Callback URLs`: `http://localhost:3000/api/auth/callback`
`Allowed Logout URLs`: `http://localhost:3000`
Go to `Advanced Settings` > `OAuth` and confirm the `JSON Web Token (JWT) Signature Algorithm` is set to `RS256` and that `OIDC Conformant` is `enabled`. Be sure to save your changes.
Awesome. We now have an Auth0 instance configured to handle authentication for our application. So let's build an app!
While we could use any web application framework for this example, I am going to use Next.js. It gives us a super-efficient React application and includes file-based routing out of the box. In addition, it allows us to run server-side logic while building our app with `getStaticProps` and (when the user requests a page) with the `getServerSideProps` function. We will need to do things like authentication server-side, but we don't want the hassle of setting up, maintaining, and paying for another server.
## Next.js
The fastest way to create a Next.js application is by using the `create-next-app` package:
```bash
npx create-next-app supabase-auth0
```
Replace the contents of `pages/index.js` with:
```jsx
// pages/index.js
import styles from "../styles/Home.module.css";
const Index = () => {
return
Working!
;
};
export default Index;
```
Run the project in Development mode:
```bash
npm run dev
```
And confirm it is working at `http://localhost:3000`.
## Authentication
Let's integrate the `nextjs-auth0` package. This is a convenient wrapper around the Auth0 JS SDK but specifically built for Next.js:
```bash
npm i @auth0/nextjs-auth0
```
Create a new folder at `pages/api/auth/` and add a file called `[...auth0].js` with the following content:
```jsx
// pages/api/auth/[...auth0].js
import { handleAuth } from "@auth0/nextjs-auth0";
export default handleAuth();
```
> The `[...auth0].js` is a catch all route. This means that any url that starts with `/api/auth0` will load this component — `/api/auth0`, `/api/auth0/login`, `/api/auth0/some/deeply/nested/url` etc.
This is one of those awesome things `nextjs-auth0` gives us for free! Calling `handleAuth()` automatically creates a collection of convenient routes — such as `/login` and `/logout` — and all the necessary logic for handling tokens and sessions. There're no extra steps required besides calling this method.
Replace the contents of `pages/_app.js` with:
```jsx
// pages/_app.js
import "@/styles/globals.css";
import { UserProvider } from "@auth0/nextjs-auth0/client";
export default function App({ Component, pageProps }) {
return (
);
}
```
Create a `.env.local` file in your root project folder and add the following:
```
AUTH0_SECRET=generate-this-below
AUTH0_BASE_URL=http://localhost:3000
AUTH0_ISSUER_BASE_URL=https://..auth0.com
AUTH0_CLIENT_ID=get-from-auth0-dashboard
AUTH0_CLIENT_SECRET=get-from-auth0-dashboard
```
> See [the Next.js documentation for Environment variables](https://nextjs.org/docs/basic-features/environment-variables) to learn more.
Generate a secure `AUTH0_SECRET` by running:
```bash
node -e "console.log(crypto.randomBytes(32).toString('hex'))"
```
> `AUTH0_CLIENT_ID` and `AUTH0_CLIENT_SECRET` can be found at `Applications > Settings > Basic Information` in the Auth0 Dashboard.
> You will need to quit the Next.js server and re-run the `npm run dev` command anytime new environment variables are added to the `.env.local` file
Let's update our `pages/index.js` file to add the ability to sign in and out:
```jsx
// pages/index.js
import styles from "../styles/Home.module.css";
import { useUser } from "@auth0/nextjs-auth0/client";
import Link from "next/link";
const Index = () => {
const { user } = useUser();
return (