Built-in security. At every step.
Auth0 helps you create trusted experiences with layered identity defences that power growth, not friction.
How Auth0 does security
We handle identity security, so you don’t have to.
Build trust at every step
Built-in identity security helps deliver reliable experiences your customers expect. Turn unknown users into trusted, repeat ones.
Secure smarter
Simplify access for trusted users. Get tougher on threats. Go passwordless, configure adaptive MFA policy for risk, strengthen API security, and much more.
Save time and resources
Automate and orchestrate identity security flows with no-code and pro-code Actions, and deploy faster.
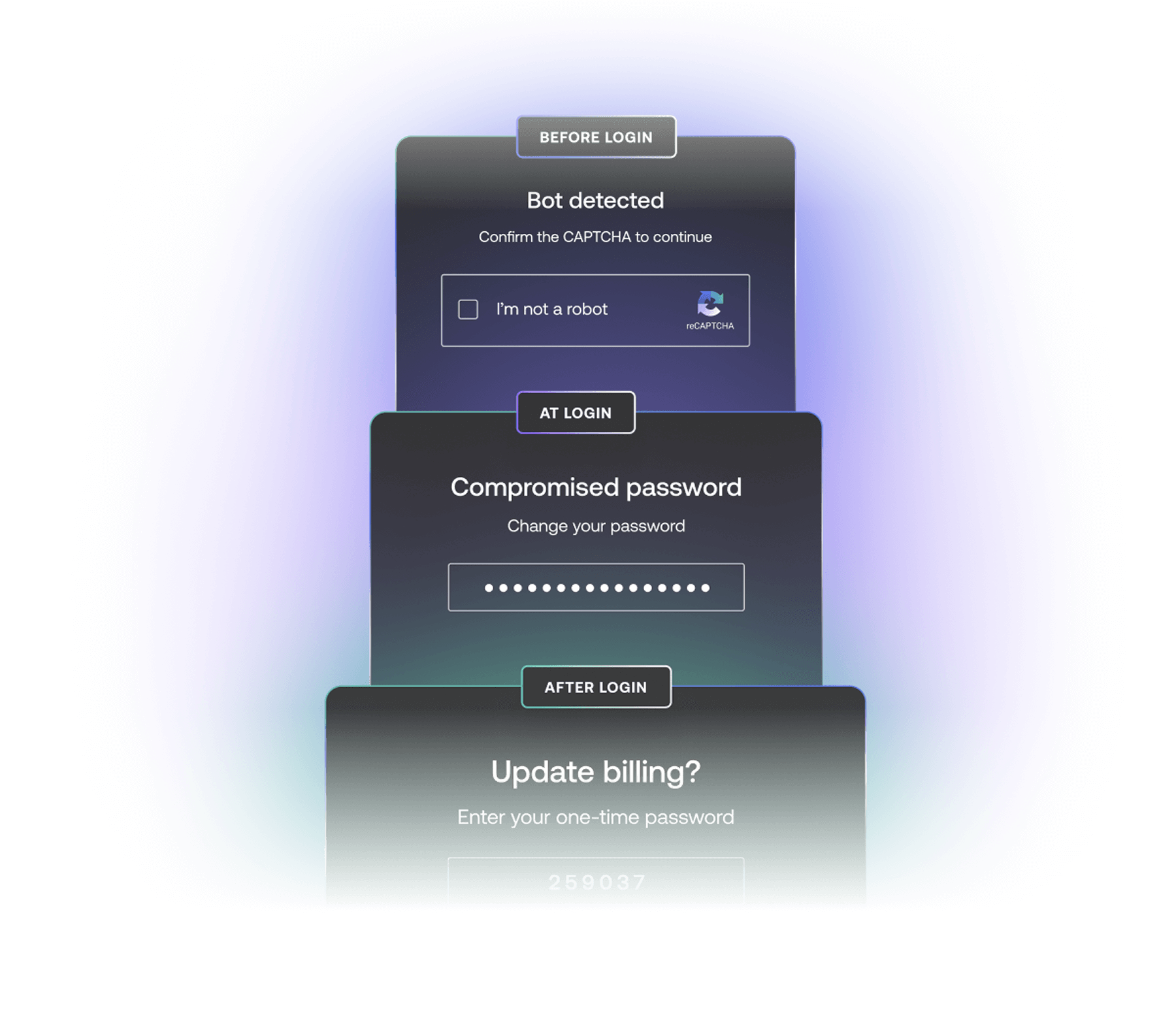
Protection at every touchpoint
Identity is security, and it is more than SSO or an MFA checkbox. We take a multi-layer approach to securing every stage of the customer journey.
Bot Detection
Detect automated attacks like fake signups and credential stuffing using 60+ risk signals, ML-powered detection models, and respond with user-friendly challenges like Auth Challenge.
Learn more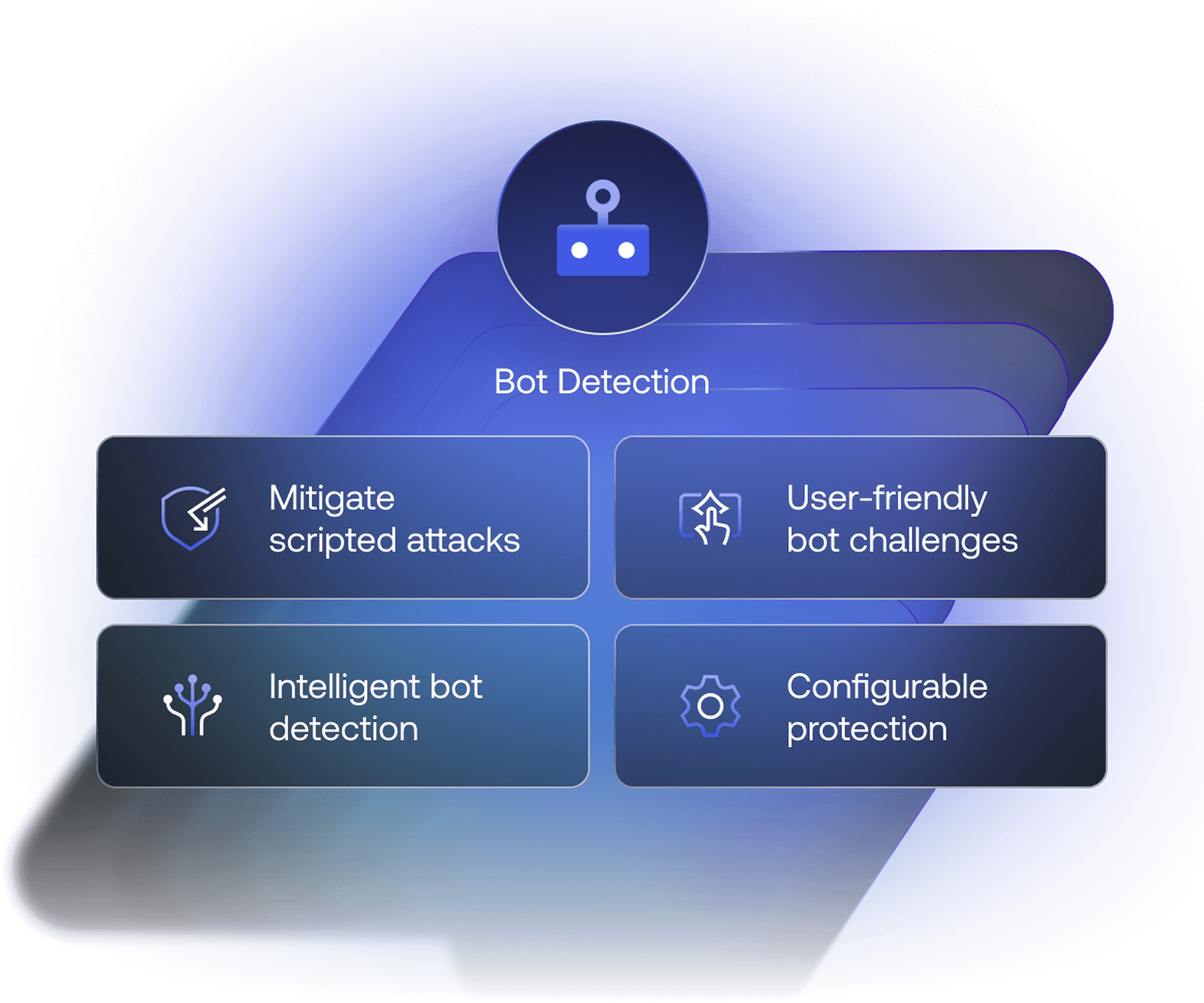
Tenant Access Control List
Prevent known threats before they even hit your login flow. Prevent malicious traffic by IP, ASN, fingerprint, geography, and more, so you can respond faster and protect your apps.
Learn more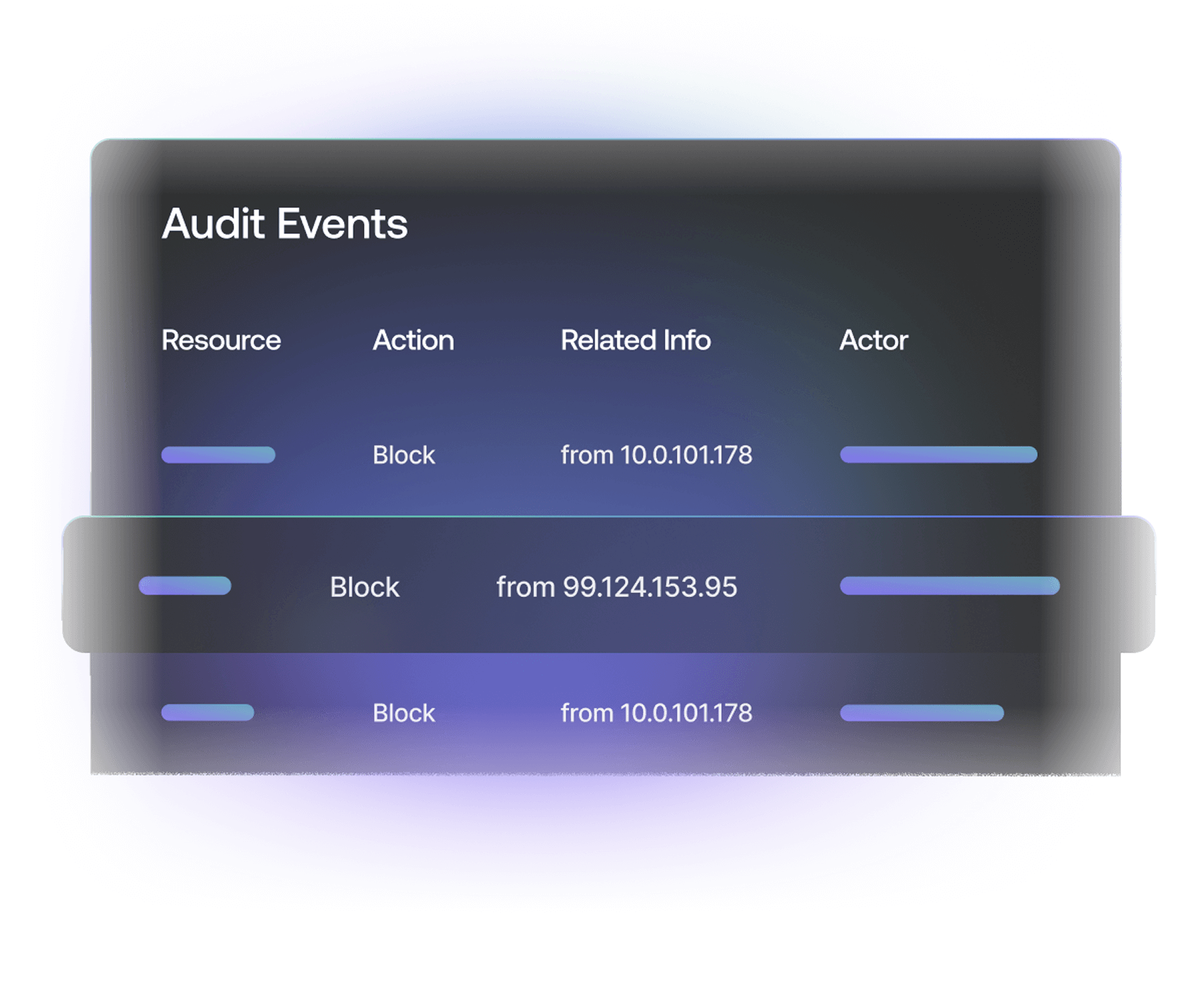
Brute-Force Protection
Prevent high-velocity attacks on a single user account by detecting repeated failed login attempts, blocking the IP, and alerting the affected user.
Learn more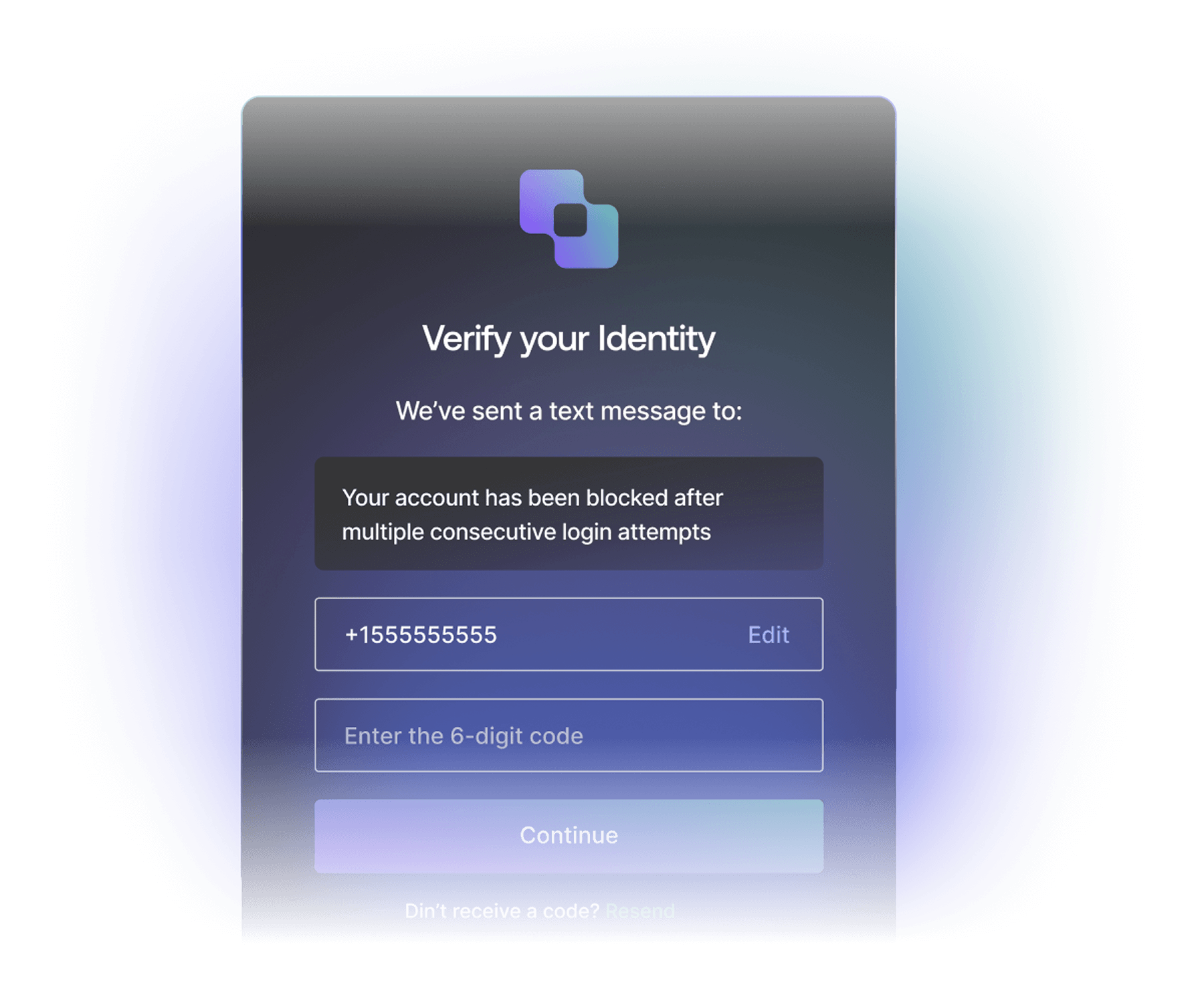
Suspicious IP Throttling
Prevent high-velocity attacks on multiple user accounts. Detect and block traffic from any IP address that rapidly attempts too many logins or signups.
Learn more
Passwordless
Offer more secure and easy alternatives to passwords like phishing-resistant passkeys. Allow users to log in quickly and securely the same way they unlock their mobile devices.
Learn more
Breached Password Detection
Prevent known breached credentials at sign-up, login, or password reset. Detect use of compromised credentials, block, and notify the user in real-time.
Learn more
Credential Guard
This is our advanced version of Breached Password Detection. Detect compromised credentials faster with a dedicated security team and support for 35+ languages and 200+ regions.
Learn more
Adaptive MFA
Set up a contextual and step-up MFA policy to assess risk signals like new devices, networks, locations, and untrusted IPs. Use out-of-the-box risk scoring or configure step-up policies to prompt for MFA only when the risk is elevated.
Learn more
Continuous Session Protection
Monitor and manage user sessions with custom logic in Actions. Prevent session hijacking and revoke suspicious sessions. Set custom timeouts for session or refresh tokens.
Learn more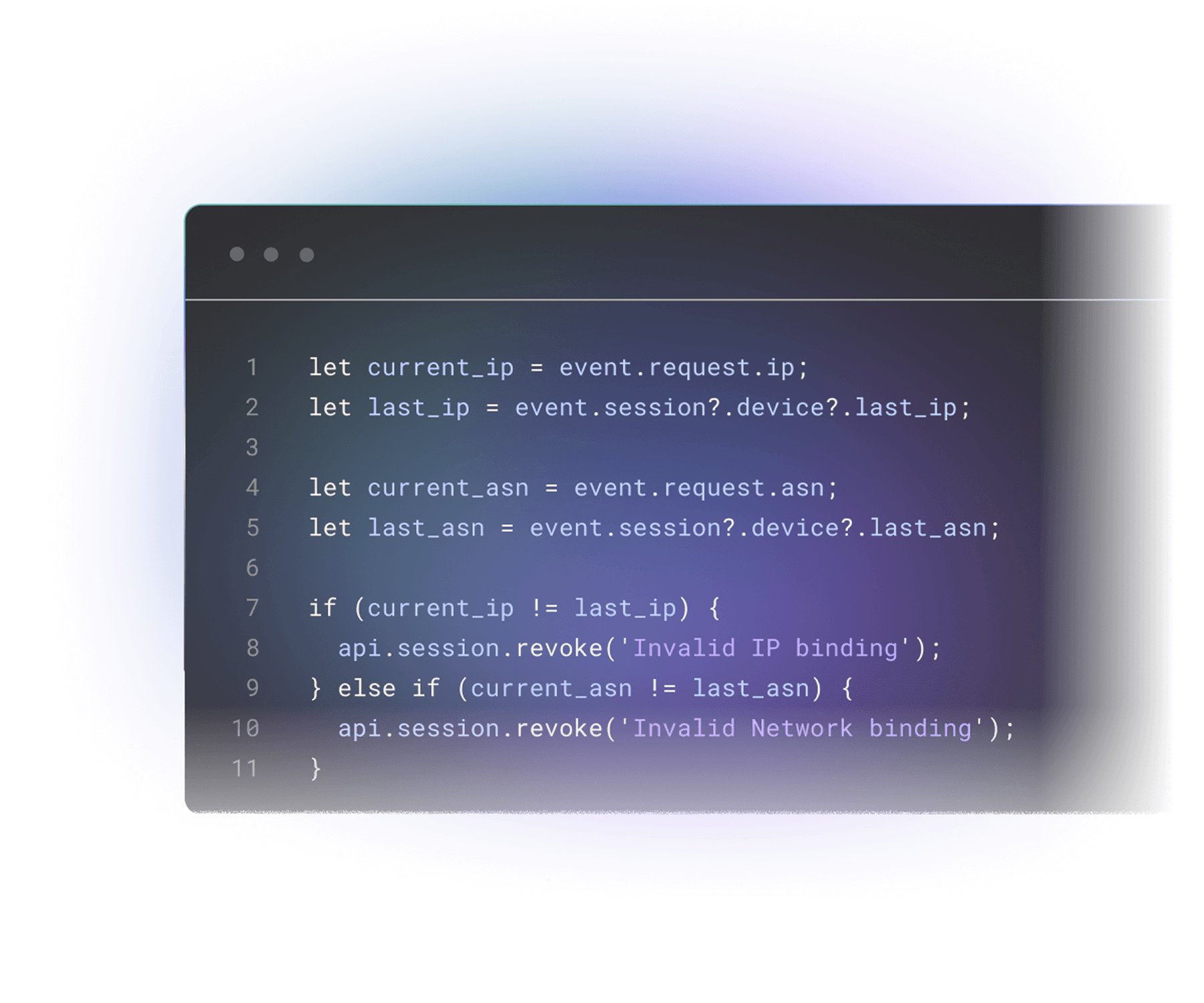
Highly Regulated Identity
Step up security and privacy for sensitive customer interactions with Strong Customer Authentication (SCA) and Financial Grade APIs (FAPI). Gain more control over your encryption keys for your compliance requirements with Customer Managed Keys.
Learn more
Universal Logout
Elevate security for your business customers using Okta Workforce Identity by automatically logging users out of SaaS apps when a logout or deprovisioning event occurs.
Learn more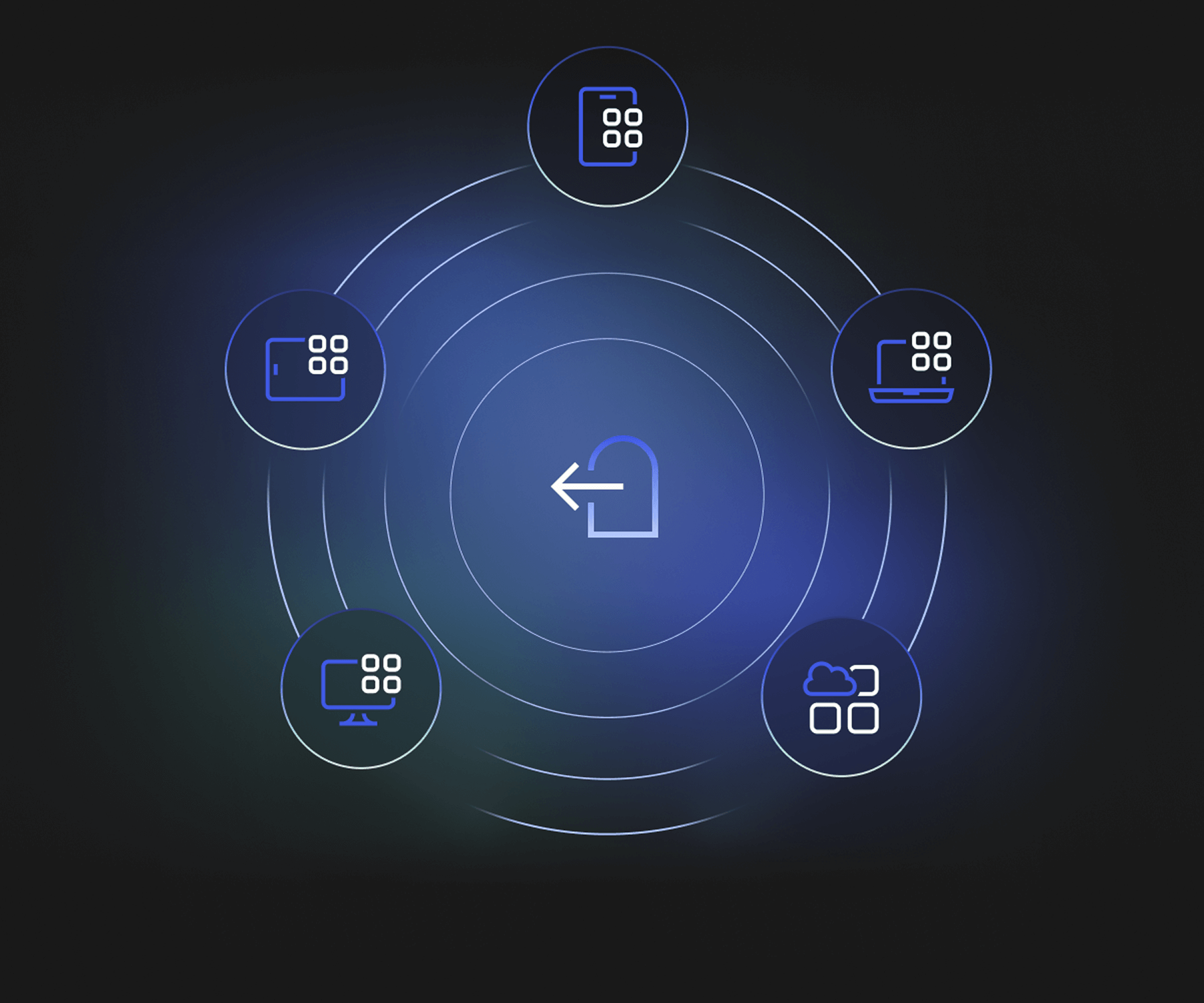
Level up your security posture
How resilient is your org? These Auth0 observability tools help you get proactive with protection, and reduce detection and remediation response times for threats.
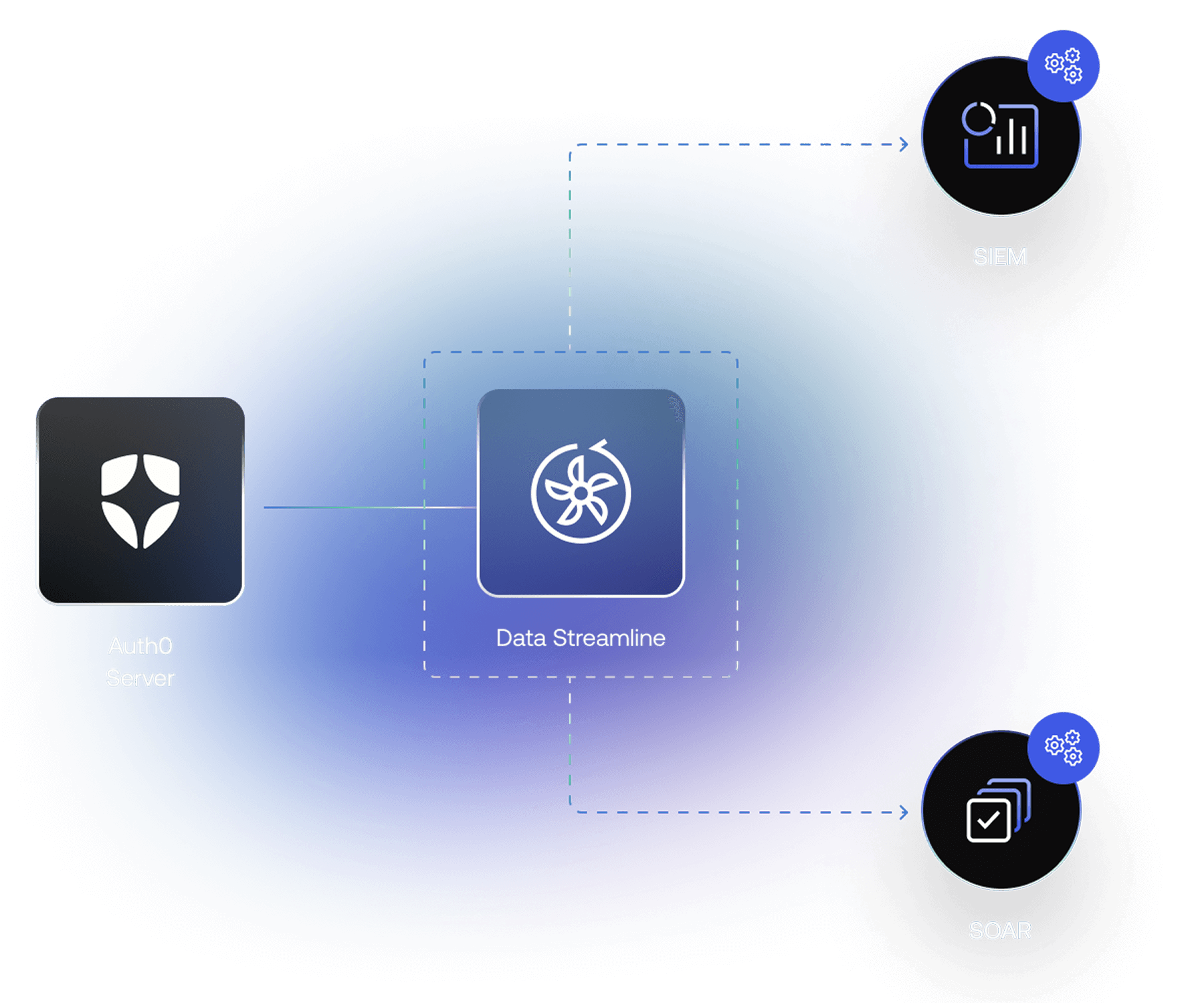
Stream relevant Auth0 log activity to third-party SIEM and SOAR tooling for faster detection and response. With custom business logic, automate response to security threats, outages, new sign-ups, and more.
Learn moreDetect and respond to attacks faster with a dashboard of real-time observation tools. Get intelligent insights into identity events, anomalies, and efficacy. Set custom threshold alerts and receive notifications that easily integrate with SIEM tools.
Learn more

"If we had to build MFA on our own, or brute-force protection, I think we would have needed five, six, seven developers for running and building the project."
Alessandro Orru
Senior Engineering Manager, Moneyfarm

“[Our engineers] don't have to build all the security around it, they don't have to deal with managing it from our database people's perspective, they don't have to deal with managing any usernames or passwords. It's all taken out of our hands.”
Scott Scherer
CIO, Jersey Mike's
“Security is a really good commodity we can get from Auth0 rather than building it ourselves. By offsetting that to a product like Auth0, we can accelerate faster and just focus on the core business functionality.”
Antony Sohal
Head of Data Platforms, Dunelm
Auth0 Marketplace
Security is a team sport. Discover and enable the integrations you need for your security stack.

























Frequently asked questions
Can I block malicious traffic by IP or geography?
Yes. Auth0 lets you block or allow traffic using Tenant Access Control List (ACL) based on IP address, ASN, device fingerprint, or geographic location. This helps stop malicious requests, like high-velocity attacks or traffic from risky regions, before they reach your login flow.
How does Auth0 protect against brute-force and credential stuffing attacks?
Auth0 uses a layered defense approach to improve security before, during, and after login. Identity threats such as brute-force attacks and credential stuffing are addressed across the full authentication flow, not just at the point of login, to reduce risk at every stage of the customer journey.
It combines multiple coordinated security controls, including brute-force protection, suspicious IP throttling, and breached password detection. Together, these protections help detect and block automated login attempts, limit repeated failures, and prevent the use of known compromised credentials.
Learn more here
Does Auth0 detect bots and prevent fake signups?
Yes. Auth0 includes Bot Detection that identifies and mitigates automated attacks such as credential stuffing and fake account creation. It uses statistical models, IP reputation, and traffic pattern analysis to detect when login or signup activity is likely coming from a bot. When risk is detected, Auth0 can trigger additional verification to reduce bot-driven abuse while minimizing friction for legitimate users.
Learn more here
How does Adaptive MFA improve login security?
Adaptive MFA evaluates each login attempt using contextual signals such as device, location, and IP reputation. If the login is considered high risk ( low confidence score), Auth0 triggers a step-up MFA challenge. It only prompts users for additional verification when risk is high, balancing strong security with a frictionless user experience.
Learn more here
Can I configure specific MFA challenges based on risk assessments in Auth0’s Adaptive MFA?
Yes, you can customize when to challenge based on the information from the risk assessors. You can define what constitutes a 'high-risk' login, such as a login from a specific geographic region or a device that hasn't been seen in 30 days, allowing you to tune your security posture to balance protection with a frictionless user experience.
Learn more here
What is Breached Password Detection and why does it matter?
Breached Password Detection helps protect your application from account takeover by identifying when users attempt to sign up or log in with credentials that have been exposed in known data breaches. Auth0 monitors publicly disclosed breaches and checks whether a user’s credentials appear in those datasets. If compromised credentials are detected, Auth0 can automatically block the login or signup attempt, prevent the use of the breached password, and require the user to reset their password before regaining access. It can also notify users and administrators so they can take immediate action.
Learn more here
What is Credential Guard in Auth0?
Credential Guard is Auth0's advanced version of Breached Password Detection that helps identify compromised credentials significantly faster with broader coverage. While standard Breached Password Detection relies on publicly disclosed breach data which can take months to surface, Credential Guard identifies exposed credentials within hours. When compromised credentials are detected, Auth0 can immediately block their use, require password resets, and notify users or administrators, helping prevent account takeover and credential stuffing attacks before they escalate.
Learn more here
Does Auth0 support hardware security keys for MFA?
Yes. Auth0 supports FIDO2-certified hardware security keys (e.g., YubiKey). These phishing-resistant factors provide strong authentication by requiring physical possession of the device.
Start your journey with Auth0
Get best-in-class customer identity, with security built in️.