Simplify APIs and trusted services communication
Bridge the gap between devices and services through secure, automated exchanges. Whether it's IoT or background processes, ensure the integrity of data.
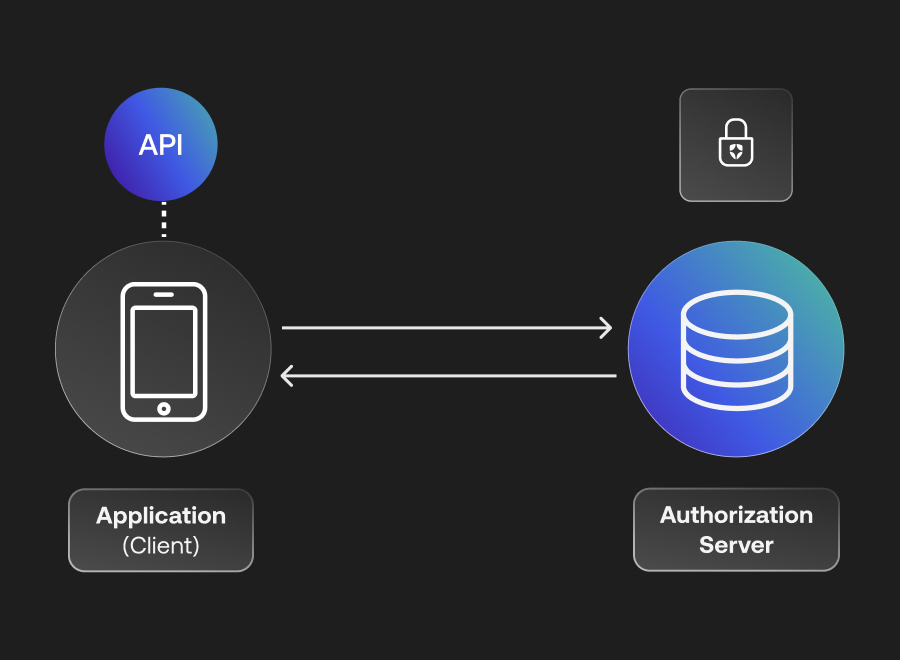
Forge trustworthy bridges for both internal and external APIs
Empower your APIs to communicate securely with non-interactive third-party applications. Keep it simple:
• Applications authenticate themselves to Auth0 via their Client Id and Client Secret.
• Auth0 verifies the information and responds with an Access Token.
• Armed with the Access Token, applications can confidently call the API.
Go beyond human identities with IoT
When machines talk, make sure it's secure. Leverage the unique Identity of each IoT device for a streamlined, impenetrable communication setup.
Using M2M Authorization
Seamless API onboarding for non-interactive apps
Integrate non-interactive applications like servers, CLIs, daemons, and more into your ecosystem. They might operate in the background, but their security takes the front seat.
Scopes and granular permissions
Chart the course for every client's journey in your API landscape. Grant or restrict access based on granular permissions:
• Application Backends
• Command line interfaces
• Miscellaneous processes
Onboarding Self-Service M2M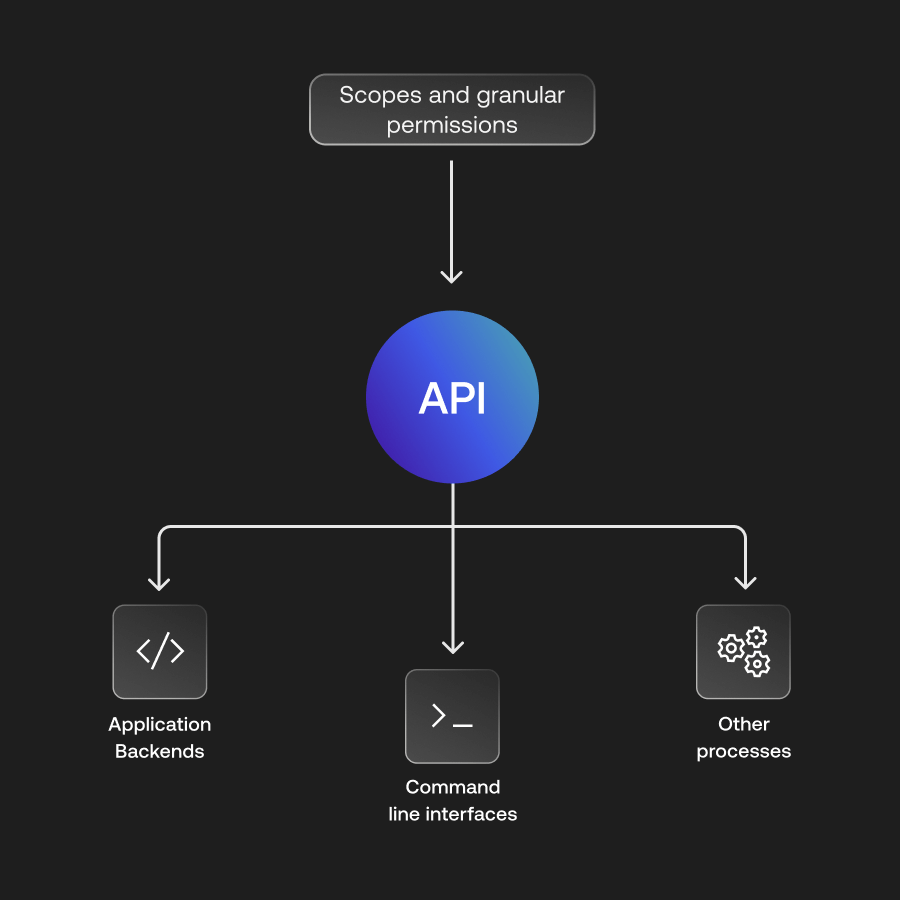
Application Backends
Let application backends, APIs, and services join the conversation without any human nudging.
Command Line Interfaces
Craft robust CLI tools that seamlessly plug into and communicate with your APIs.
Continuous Processes
Empower job schedulers, daemons, and consistent system processes to guard and engage with your API.
Security backed by standards
Sleep better knowing every byte of data exchanged adheres to globally accepted standards. Dive into the OAuth2 Client Credentials Grant flow, and witness security in motion.
Learn about OAuth2
Frequently asked questions
Can I limit the scope of M2M tokens in Auth0?
Yes, Auth0 allows you to define coarse-grained scopes for every M2M client. Following the principle of least privilege, you can ensure a service only has access to the specific API endpoints it needs (e.g., 'read:reports'). This minimizes the potential impact of a compromised machine identity by limiting what it can do within your ecosystem.
Does Auth0 support M2M for IoT devices?
Yes, Auth0 M2M authentication is ideal for securing IoT devices and sensors that need to communicate with back-end APIs. By treating each device as a secure client, Auth0 ensures that data transmitted from the field is authenticated at the source, preventing unauthorized data injection and protecting the integrity of your IoT network and data analytics.
How does Auth0 manage M2M client secrets?
Auth0 manages M2M security by allowing developers to easily rotate client secrets and support asymmetric keys for authentication. This allows security teams to maintain a high security posture without disrupting automated workflows. Auth0 also provides detailed audit logs for every M2M token request, ensuring full visibility into machine-level access and activity.
What is Auth0 Machine-to-Machine (M2M) authentication?
Auth0 Machine-to-Machine (M2M) authentication enables secure communication between non-human identities, such as back-end services, APIs, and CLI tools. By using the OAuth 2.0 Client Credentials flow, Auth0 issues secure, time-bound JWT tokens that allow automated systems to authorize with each other securely, eliminating the need for hard-coded passwords or long-lived secrets.
Why is M2M security critical for microservices?
In a microservices architecture, M2M security ensures that service-to-service communication is verified and follows least-privilege principles. Auth0 prevents unauthorized lateral movement within your cloud infrastructure by requiring every internal request to present a valid, scoped token, ensuring that even if one service is compromised, the rest of your system remains protected.
How else can a confidential M2M client authenticate?
Client Secrets are the default way, supported as a symmetrical authentication method. Two additional asymmetric authentication methods include: Private Key JWT, use of a pair of public and private keys as credentials, and mTLS for OAuth, leveraging a standard X.509 client certificate that is registered with Auth0 that is also paired with a corresponding private key.
Ready to dive in?
Unlock the potential of seamless machine-to-machine communications.