Secure access for
But not



Implement Auth0 in any application in just five minutes
With a few lines of code you can have Auth0 integrated in any app written in any language, and any framework. We provide 30+ SDKs & Quickstarts to help you succeed on your implementation
It all starts with Customer Identity
From improving customer experience through seamless sign-on to making MFA as easy as a click of a button – your login box must find the right balance between user convenience, privacy and security.That’s why Okta and Auth0 have joined forces. Because we know together we can help you build a better solution for Customer Identity (CIAM) that will reduce security and compliance risks, improve your UX, and help your developers maximize their time.
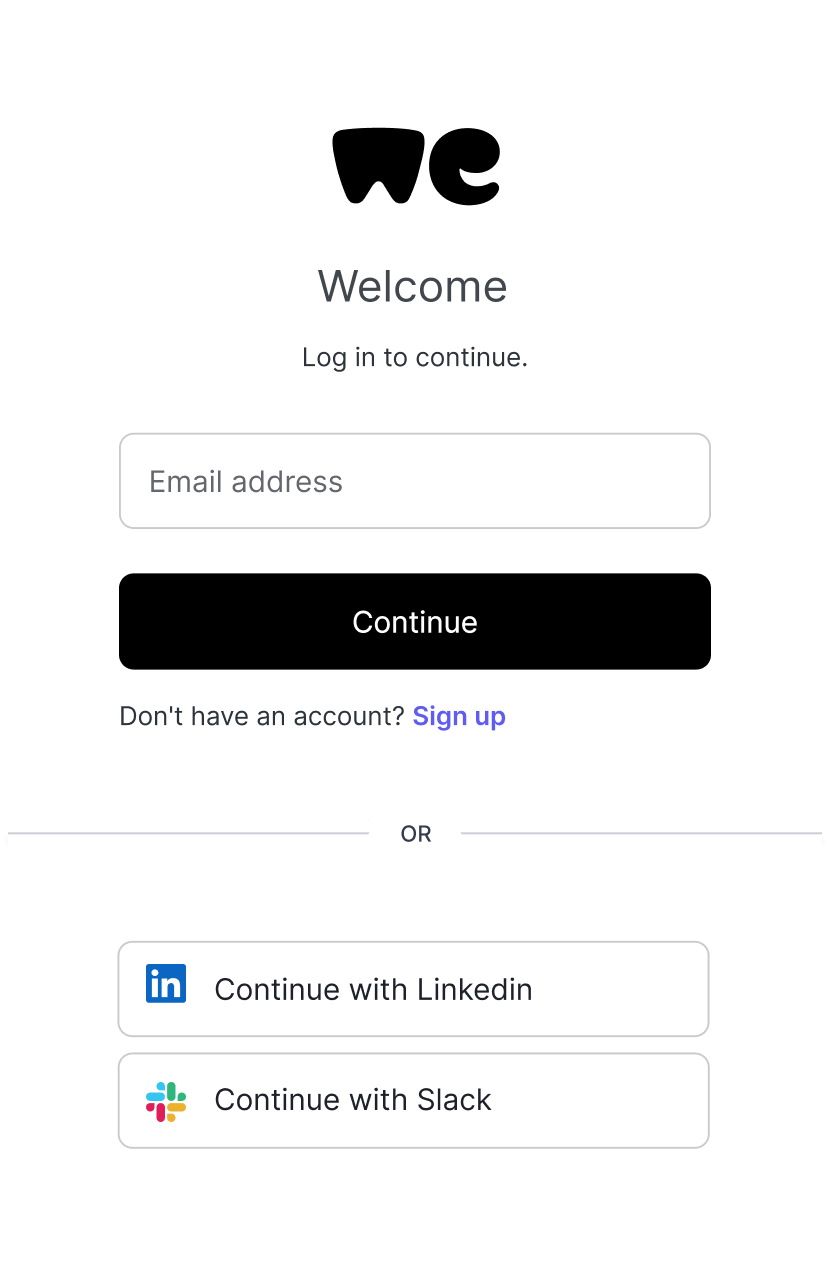
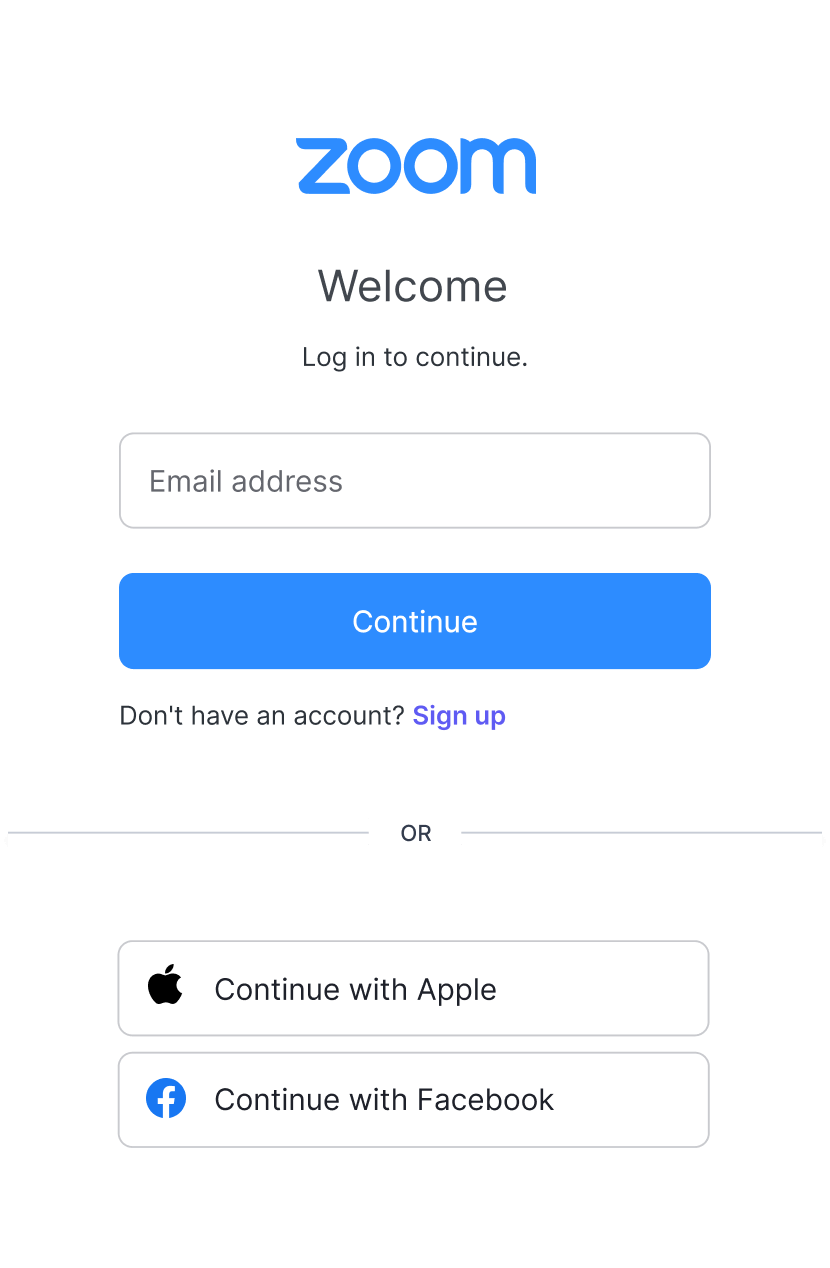
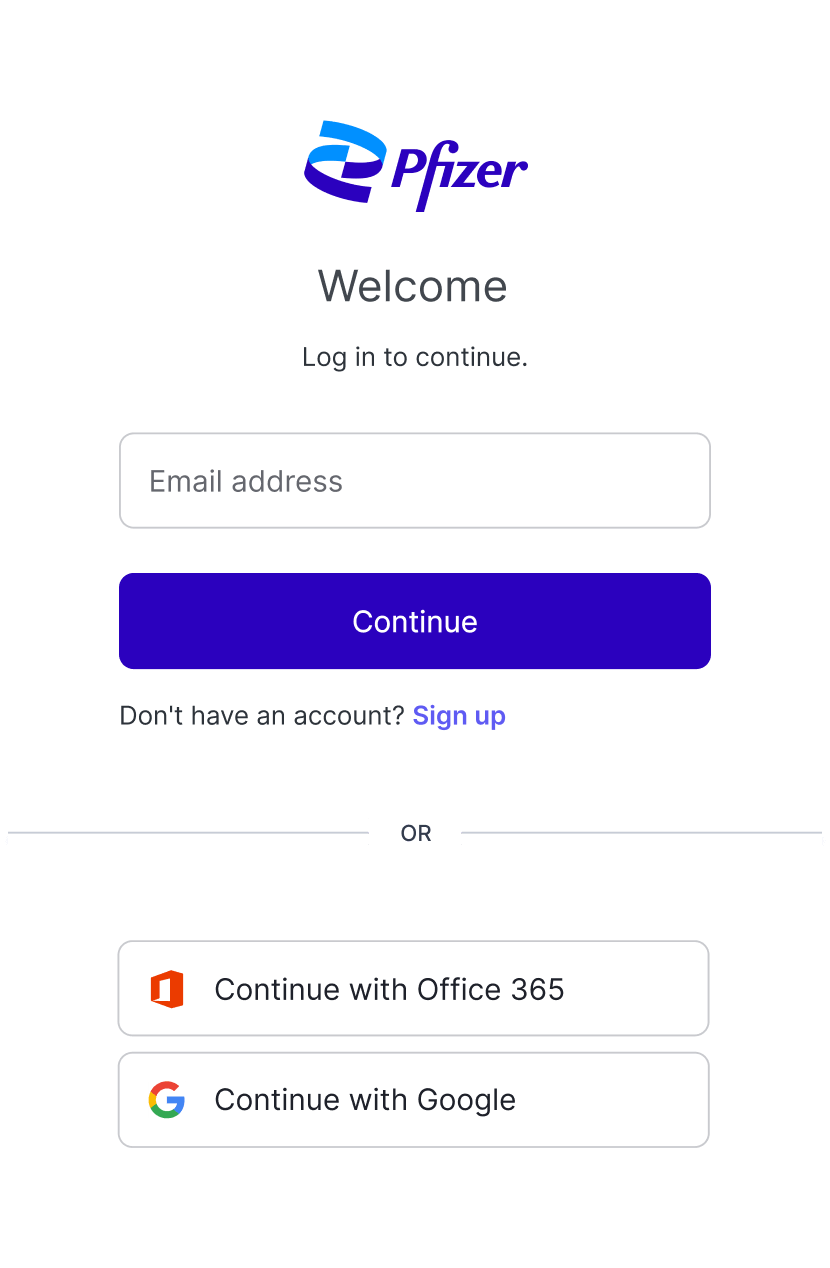
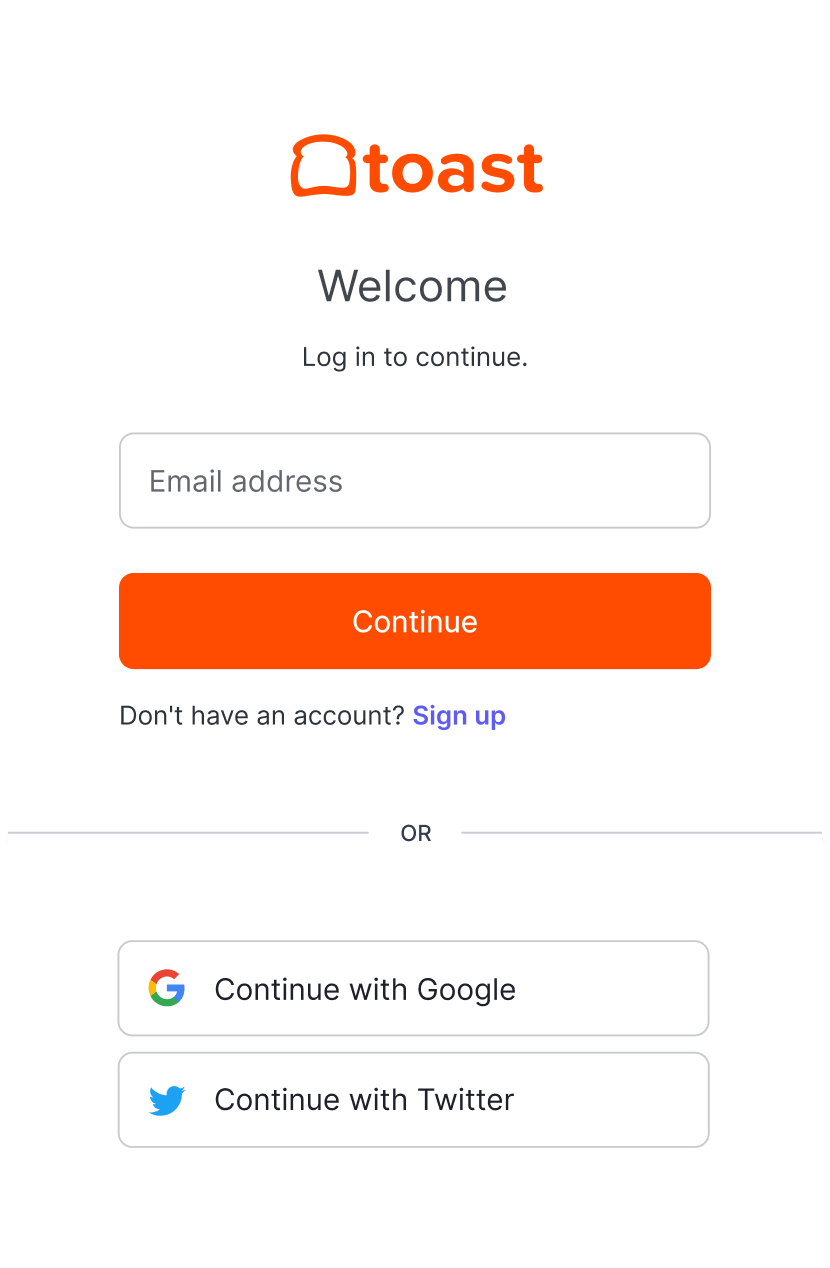



Auth0 is an easy to implement, adaptable authentication and authorization platform
Basically, we make your login box awesome.
Identity is so much more than just the login box
Let’s take a look at everything you can do.
Optimize for user experience and privacy. Use social login integrations, lower user friction, incorporate rich user profiling, and facilitate more transactions.

Anonymous User
Bot Detection
Registration


Progressive Profiling

Step-up Auth
Auth Factors
convenience
privacy
security
Resources
report
The Total Economic Impact of Auth0
11.7 ᴹ
Total benefit
548%
ROI
<6mo
Payback Time
powered by Forrester® ↗
whitepaper
Build vs Buy: Guide to Identity Management
6 Signs You Need to Move From DIY to an Identity Management Solution
video
The Auth0 Product Tour
A short tour through Auth0’s extensibility and uses for B2B, B2C, and B2E.
























