A session is a group of interactions between a user and an application during a given timeframe. A single session may consist of multiple activities (such as page views, events, social interactions, and e-commerce transactions) and can store this information temporarily while the user is connected. With a standard Set-Cookie header implementation, a session ends when a user leaves a website or closes their browser. To prevent users from having to log in every time, applications can extend sessions by setting a maximum lifetime for the . Sessions end when a user logs out or a session lifetime limit is reached. To learn more, review Auth0 Privacy and Cookie Policy.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Session use cases
Auth0 maintains a login session for any user who authenticates through an application. When a user performs a new standard login, Auth0 resets the login session. Updating a password, email, phone number, or username also causes a user’s Auth0 session to expire. When you build an application requiring authentication, you can use sessions to determine whether a user is authenticated each time a request occurs. Depending on how your app has been built, different are recommended to support a more secure experience for users. For example, consider an OIDC-compliant ( Connect) website called storezero.io.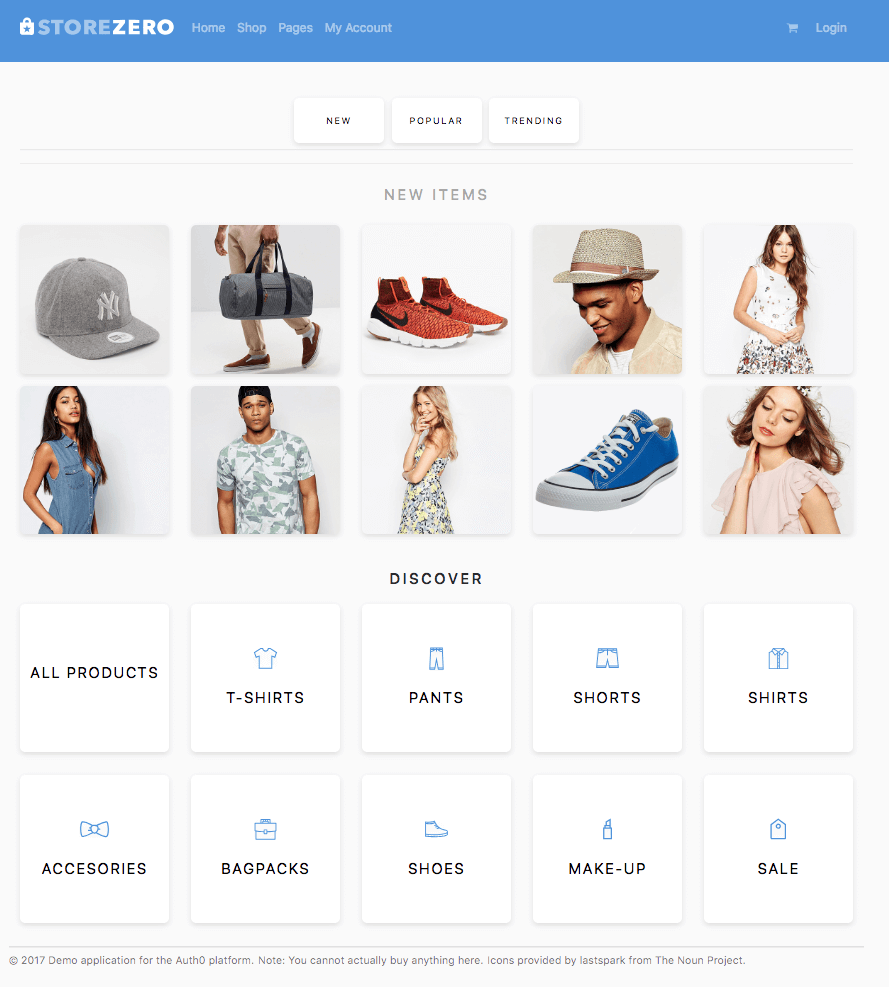
Login flows
Most types of applications (such as web apps, single-page apps, and native apps) should use the Authorization Code Flow with PKCE to facilitate login authentication. This flow involves exchanging an authorization code for tokens.The Authorization Code Flow with PKCE replaces the prior use of implicit flow for single-page apps without a backend. New developments must use this flow to ensure optimal security. Migrating existing apps using implicit flow to the PKCE-enhanced authorization code flow is also highly recommended.
User logs in with username and password
In this example, a user manually logs in using their username and password:- Auth0’s SDK creates a local session and redirects the user to the Auth0 authorization server (
/authorizeendpoint). - The authorization server creates a session, then redirects the user to the login and authorization prompt.
- The user authenticates using their username and password.
- The Auth0 authorization server updates the user’s previously-created session to indicate they are logged in.
- Depending on the flow used, the authorization server returns the user to your application, along with either an ID token or an authorization code.
- Your application exchanges the token or authorization code for an access token and completes the flow.
- The local session (storezero.io), which indicates to the application whether a user is authenticated.
-
The session (storezero.auth0.com), which indicates to the server whether a user is authenticated. The server session can also optionally track details about the authentication.
- For example, the authorization server can track if a user leveraged multi-factor authentication (MFA). This information can then be used to determine whether a user should be prompted to log in or use MFA the next time they arrive at the authorization server.
User logs in with identity provider
In this example, the user opts to log in with Facebook instead of their username and password:- Auth0’s SDK creates a local session and redirects the user to the Auth0 authorization server (
/authorizeendpoint). - The authorization server creates a session, then redirects the user to the login and authorization prompt.
- Upon choosing to log in with Facebook, the authorization server redirects the user to Facebook.
- Facebook creates a session and authenticates the user. Facebook then updates its session to indicate the user is logged in.
- Facebook returns the user to the Auth0 authorization server. The authorization server then updates its session to indicate the user is logged in.
- Depending on the flow used, the authorization server returns the user to your application, along with either an ID token or an authorization code.
- Your application exchanges the token or authorization code for an access token and completes the flow.
Session management for SPAs
In the previous examples, a local session is created when the user initiates either login flow. This local session can keep users logged in and determine when they need to reauthenticate. However, local sessions are not available for applications without backends, such as single-page apps (SPAs). Instead, these applications use a different approach known as silent authentication to keep users logged in. Silent authentication uses the session on the authorization server to determine when a user must reauthenticate. A hidden iframe redirects authentication requests to the authorization server along with theprompt=none parameter. This parameter prevents the server from prompting the user for input.
- If the session on the authorization server has not expired, the transaction continues seamlessly. The server sends an through WMRM (Web Message Response Mode), which leverages
postMessage. - If the session on the authorization has expired or the user logs out, the redirect in the iframe returns an error. The application must then direct the user to the authorization server for reauthentication.

