Auth0 provides two ways to implement role-based access control (RBAC), which you can use in place of or in combination with your API’s own internal access control system:The Authorization Core feature set matches the functionality of the Authorization Extension, improves performance and scalability, and provides a more flexible RBAC system than the Authorization Extension.Currently, both implement the key features of RBAC and allow you to restrict the custom scopes defined for an API to those that have been assigned to the user as permissions.
Prerequisites
Install the Authorization ExtensionConfigure extension
- Go to Auth0 Dashboard > Extensions, and select Auth0 Authorization.
-
Choose Configuration at the top right of the Authorization Dashboard.
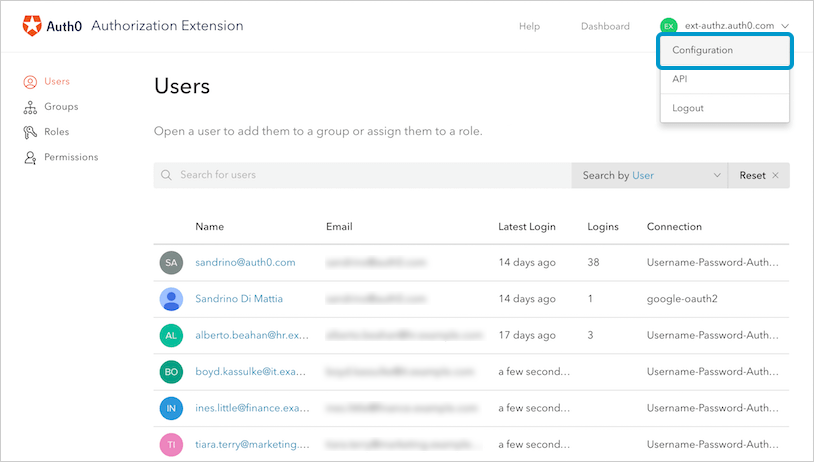
-
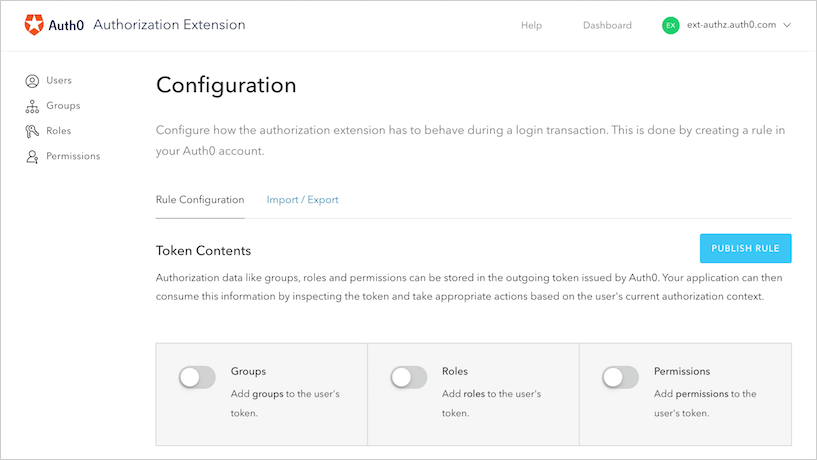
This brings you to the Rule Configuration section of the Configuration page. All of the changes you make in the sections under Token Contents, such as those related to groups, roles, and permissions, will be reflected in the rule you export at the completion of this step.
ApiKey
The rule uses the ApiKey to communicate with the Authorization Extension API and get the policy. The ApiKey is stored as a rule config and will be created automatically when the rule is published. To rotate the ApiKey, click the Rotate button; when the ApiKey is rotated, the rule config will be updated automatically.Add authorization information to the token issued
You can store authorization data like groups, roles, or permissions in the outgoing token issued by Auth0. Your application can then consume this information by inspecting the token and take appropriate actions based on the user’s current authorization context. To add groups, roles, and/or permissions information to the outgoing token, enable the slider next to the option you want to be included.Merge authorization data from IdP
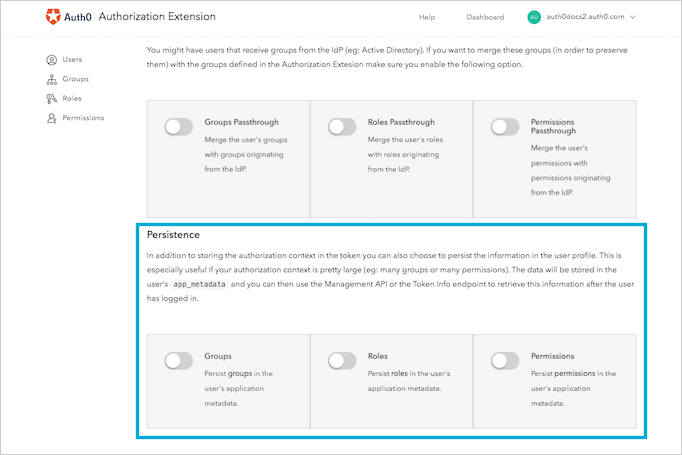
You might have users that receive groups, roles, or permissions from the (IdP) you’re using, such as Active Directory. If you want to merge these items (to preserve them) with the ones defined in the Authorization Extension, make sure you enable the appropriate Passthrough options. Enable the slider next to the appropriate merges you want enabled.Store authorization information in user profiles
If your authorization context is large (for example, the user might belong to many groups or have been granted many permissions), you might find it useful to store some of the authorization content in the users’ profiles. This allows you to store less information in the token, which means you’re less likely to see performance-related issues or even problems with token issuance. Persistence is the process by which you store groups, roles, and permissions information in the users’ profiles. The data will be stored in the user’sapp_metadata field, and you can then use the or the Dashboard to retrieve this information after the user has logged in.