(SSO) occurs when a user logs in to one application and is then signed in to other applications automatically, regardless of the platform, technology, or domain the user is using. The user signs in only one time, hence the name of the feature (Single Sign-on). For example, if you log in to a Google service such as Gmail, you are automatically authenticated to YouTube, AdSense, Google Analytics, and other Google apps. Likewise, if you log out of your Gmail or other Google apps, you are automatically logged out of all the apps; this is known as Single Logout. SSO provides a seamless experience for users when using your applications and services. Instead of having to remember separate sets of credentials for each application or service, users can simply log in once and access your full suite of applications. Whenever users go to a domain that requires authentication, they are redirected to the authentication domain where they may be asked to log in. If the user is already logged in at the authentication domain, they can be immediately redirected to the original domain without signing in again.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
How it works
Single Sign-on and Single Logout are possible through the use of sessions. There may be up to three different sessions for a user with SSO:- Local session maintained by the application
- session, if SSO is enabled
- session, if the user chose to log in through an (such as Google, Facebook, or an enterprise Identity Provider)
SSO with Universal Login
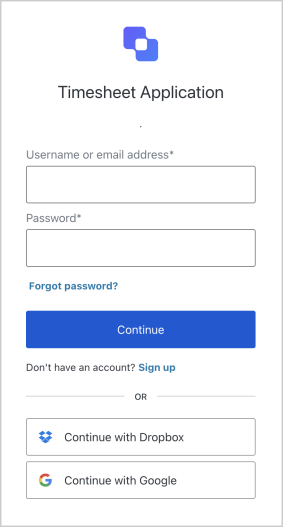
The easiest and most secure way to implement Single Sign-on (SSO) with Auth0 is by using Universal Login for authentication. In fact, currently SSO is only possible with native platforms (like iOS or Android) if the application uses . The Swift and Android quick starts provide some examples of using Universal Login. If you cannot use Universal Login with your application, review the following for additional info on embedded authentication:If you are using Passwordless with Single Sign-On, connection parameters
sms and email do not utilize the existing Auth0 session, and the user will be prompted to log in.SSO on first login
For SSO with Auth0, the Central Service is the Auth0 . Let’s look at an example of the SSO flow when a user logs in for the first time:- Your application redirects the user to the login page.
- Auth0 checks to see whether there is an existing SSO cookie.
-
Because this is the first time the user is visiting the login page and no SSO cookie is present, the user will be asked to log in using one of the connections you have configured.
- Once the user has logged in, Auth0 will set an SSO cookie and redirect the user to your application, returning an ID Token that contains identity information for the user.
SSO on subsequent logins
Let’s look at an example of the SSO flow when a user returns to your website for a subsequent visit:- Your application redirects the user to the login page.
- Auth0 checks to see whether there is an existing SSO cookie.
- Auth0 finds the SSO cookie, and if necessary, updates it. No login screen is shown.
- Auth0 redirects the user to your application, returning an ID Token that contains identity information for the user.
Check user’s SSO status
You can check a user’s SSO status from an application by calling thecheckSession method of the auth0.js SDK, which will attempt to silently authenticate the user within an iframe. Whether the authentication is successful or not indicates whether the user has an active SSO cookie.
Protocols
SAML and WS-Federation
Security Assertion Markup Language (SAML) and Web Services Federation () are both protocols that are widely used in SSO implementations. Both SAML and WS-Fed exchange authorization and authentication data in XML format; the main parts of this exchange are the user, the identity provider, and the service provider. With SAML or WS-Fed:- A user requests a resource from the service provider.
- The service provider checks with the identity provider to see if the user should have access to the resource.
- The identity provider verifies the user’s identity, and if valid, asserts back to the service provider that the user should have access.
OpenID Connect
Connect (OIDC) is an authentication protocol commonly used in consumer-facing SSO implementations. The OIDC protocol handles authentication through and a central identity provider. With OIDC:- A user requests access to an application.
- The application redirects the user to the identity provider for authentication.
- The identity provider verifies the user, and if successful, prompts the user to grant data access to the application.
- If access is granted, the identity provider generates an ID Token, which contains user identity information that the application can consume.
- The identity provider returns the user to the application.
AD/LDAP
Lightweight Directory Access Protocol (LDAP) is an application protocol used to access a directory of credentials that can be shared by multiple applications; it is commonly used by intranets. When paired with Active Directory (AD), LDAP provides a centralized location for user identity, so the application makes an authentication request to the LDAP/AD server. The LDAP protocol exchanges information in LDAP Data Interchange Format (LDIF).Service-provider-initiated SSO
For Service-Provider-initiated SSO, Auth0 is the SSO Service Provider (SP). When a user logs in to an application:- The application presents the user with one or more external identity providers.
- The user selects an identity provider to authenticate with and logs in.
- Upon successful authentication, the user is returned to the application.
Identity-provider-initiated SSO
For Identity-Provider-initiated SSO, a third-party Identity Provider (IdP) is the SSO provider. When a user logs in to an application:- The application redirects the user to an identity provider.
- The third-party identity provider performs authentication and authorization.
- Upon successful authentication, the user is returned to the application.

