The Client Credentials Flow (defined in OAuth 2.0 RFC 6749, section 4.4) involves an application exchanging its application credentials, such as and , for an . This flow is best suited for Machine-to-Machine (M2M) applications, such as CLIs, daemons, or backend services, because the system must authenticate and authorize the application instead of a user.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
How it works
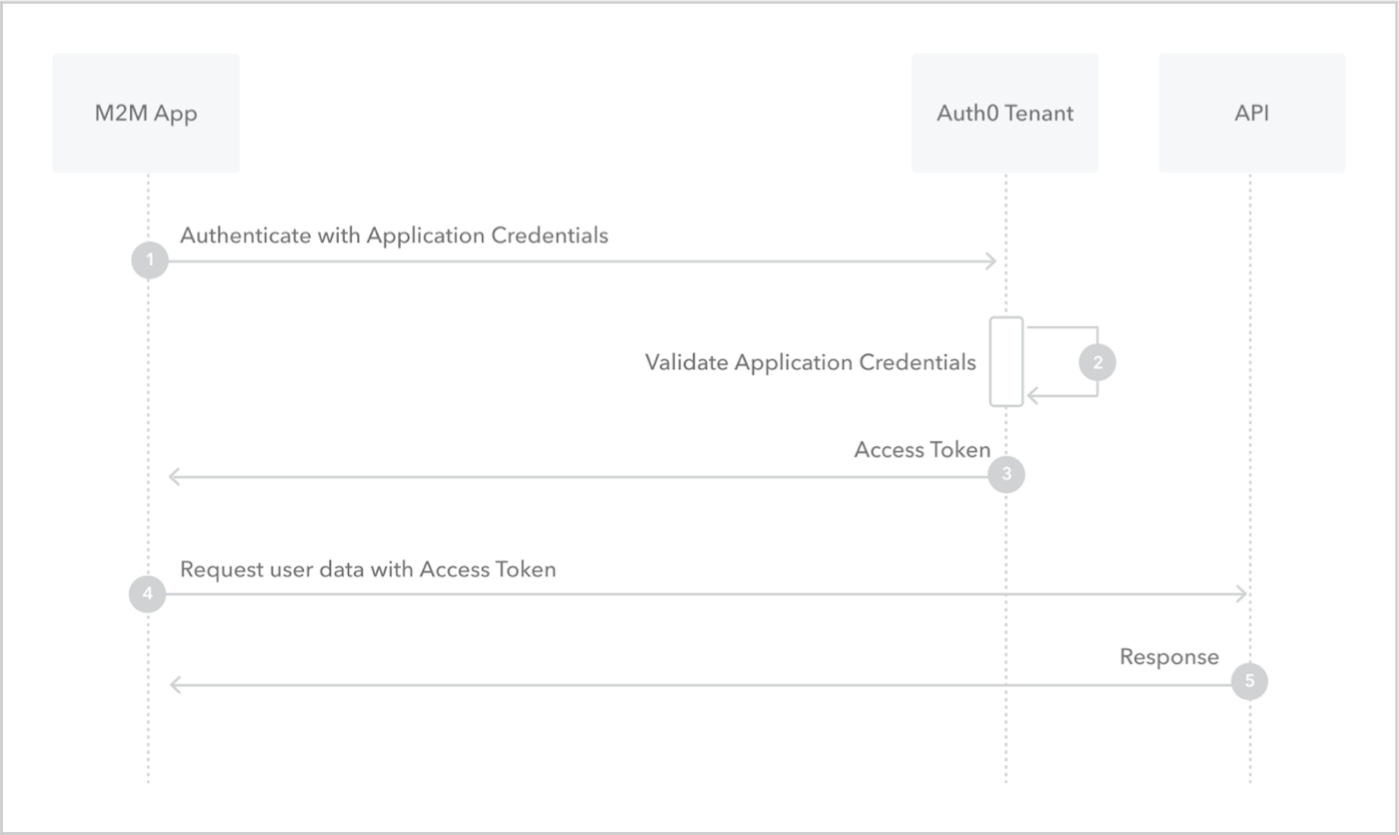
- Application sends application’s credentials to the Auth0 Authorization Server. To learn more about client authentication methods, read Application Credentials.
- Auth0 Authorization Server validates application’s credentials.
- Auth0 Authorization Server responds with an access token.
- Application can use the access token to call an API on behalf of itself. For more information on this process, see Validate JSON Web Tokens.
- API responds with requested data.

