Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Log streams are designed for monitoring and analytics purposes. We don’t recommend using log streams in your application’s critical path or for real-time decision-making.By default, logs may not display in the exact order in which they occurred. If you are streaming tenant logs and require chronological sorting, we recommend implementing log sorting through your stream processing.
By enabling Log Streams, Customer becomes the Controller of such information and is responsible for the data exported from the Auth0 Platform, including what information is streamed and how it is used by Customer.
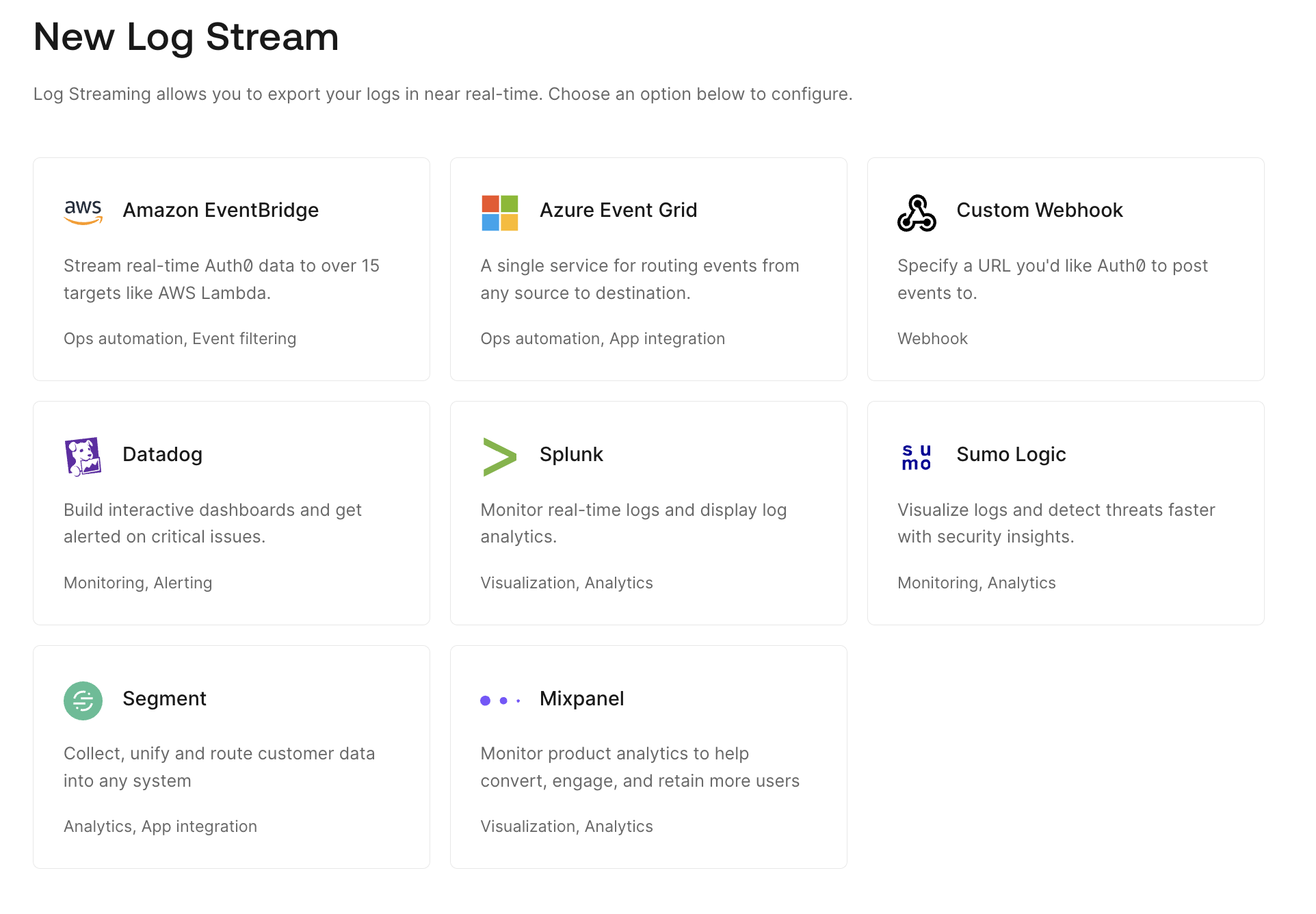
Supported log streaming services
We support a variety of log streaming services through the Auth0 Marketplace, including:- Amazon EventBridge
- Azure Event Grid
- Elastic
- Logz.io
- MDR ONE
- Mixpanel
- Oodle AI
- Oort
- Pangea
- Panther
- Perch Security
- Segment
- Slack
-
Datadog
- Auth0 provides Datadog dashboard templates. To learn more, read Use Auth0 Dashboard Templates with Datadog.
-
Splunk
- Auth0 also provides a dashboard to visualize the data from your Auth0 tenant. You can use the app to view recommended aggregations from Auth0 or to use them as a starting point to create your own custom visualizations. To learn more, read Use Auth0 App for Splunk.
-
Sumo Logic
- Auth0 provides a Sumo Logic app and dashboard to visualize and monitor the health of login traffic from your Auth0 tenant. You can also use to view recommended aggregations from Auth0 or to use them as a starting point to create your own custom visualizations. To learn more, read Use Auth0 App for Sumo Logic.
Delivery attempts
Auth0 delivers each log to your server as it is triggered in our system. We guarantee logs are delivered at least once. When a log is triggered:- We attempt to deliver the log to your server up to three times.
- If we fail to reach your server by the third attempt, we log an error visible in the Health view for the log stream.
- We restart this process for any errored log until the problem is resolved.
Log retention
Your Auth0 log retention period depends on your subscription level. If there is an issue where your server does not receive logs sent from Auth0, you can delete the stream and then recreate it with the Starting Cursor field set to a specific day and time within the retention period.Filtering and PII obfuscation
Customers can choose which filter categories of their logs to stream and which to exclude to ensure the external destination receives only the relevant data. Customers can also choose to mask or hash Personal Identifiable Information (PII) in the streamed logs.PII obfuscation
Auth0 provides two ways to obfuscate PII tenant log fields when streaming to third-party destinations:- Masking: the field values are replaced with asterisks
- xxHash: a fast, non-cryptographic hash algorithm
| Data | Field name |
|---|---|
first_name | first_namegiven_namename |
last_name | last_namefamily_namename |
email | email |
phone | phonephone_numberold_phone_numbernew_phone_number |
address | address |
username | usernameuser_name |

