You can manually rotate a signing key periodically to change the JSON web key (JWK) key used by applications and APIs to validate tokens. If your application or API does not allow for this key change, and it attempts to use an expired signing key to verify a token, the authentication request will fail. Although Auth0 signs with only one signing key at a time, your tenant’s Connect (OIDC) discovery document always contains multiple keys. The OIDC discovery document will always include both the current key and the next key, and it may also include the previous key if the previous key has not yet been revoked. To provide a seamless experience in case of an emergency, your application should be able to use any of the keys specified in the document. To learn more about OpenID Connect discovery documents, read Locate JSON Web Key Sets. You can rotate your tenant’s application signing key using the or the Auth0 .Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Use the Dashboard
-
Go to Dashboard > Settings > Signing Keys.
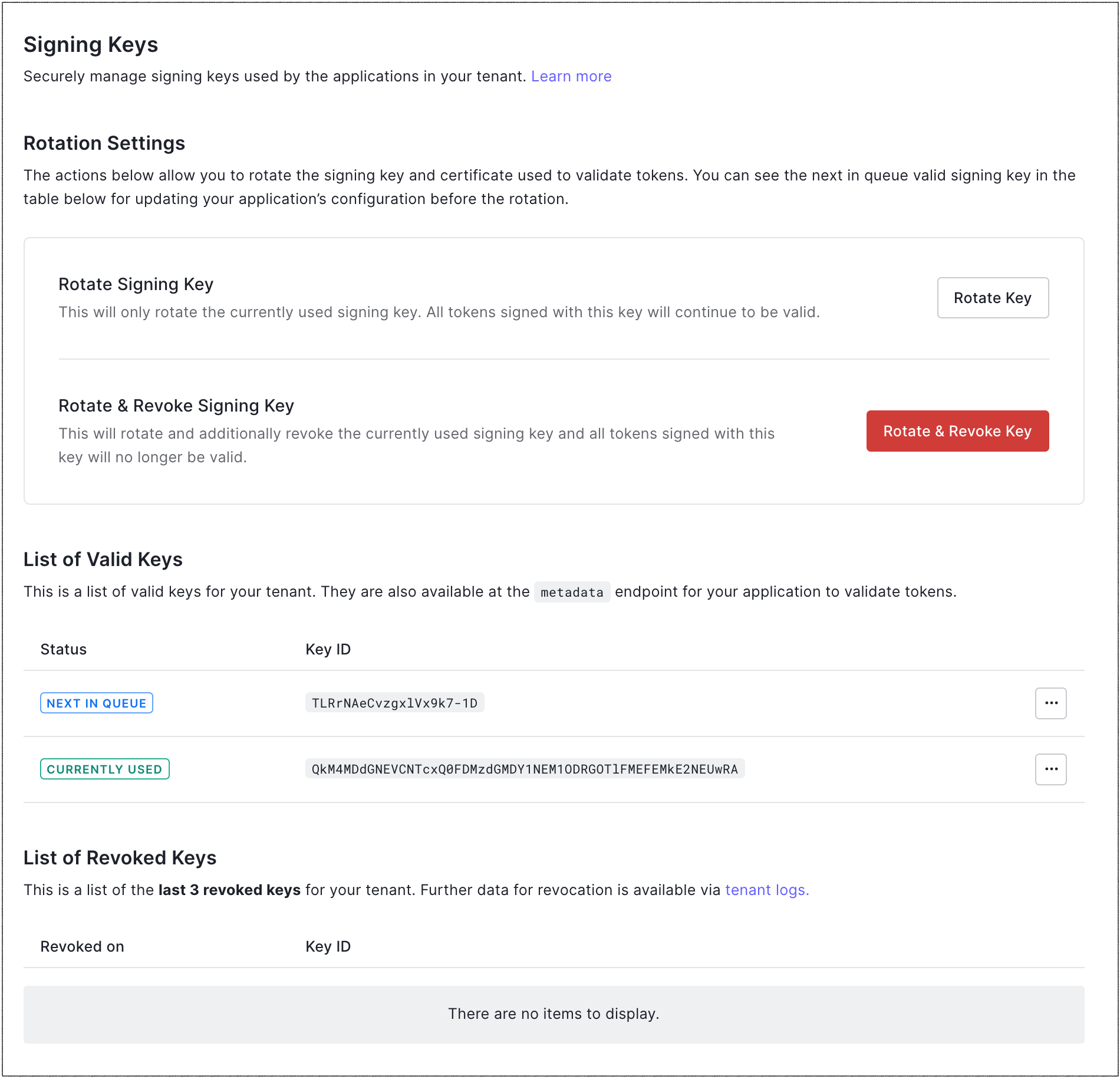
- Under Rotation Settings, locate Rotate Signing Key, and select Rotate Key.
-
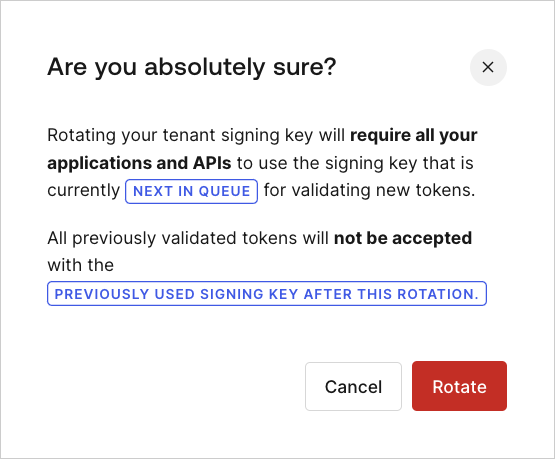
Click Rotate to confirm.
Use the Management API
- To get a list of the signing keys, make a
GETcall to the Get all Application Signing Keys endpoint. - To rotate the signing key, make a
POSTcall to the Rotate the Application Signing Key endpoint. Be sure to replace theMGMT_API_ACCESS_TOKENplaceholder value with your Management API access token.
| Value | Description |
|---|---|
MGMT_API_ACCESS_TOKEN | Access Token for the Management API with the scopes create:signing_keys and update:signing_keys. |
Key rotation impact
APIs and API gateways accepting access tokens
Most middleware and API gateways leverage the JSON web key set (JWKS) endpoint to retrieve the current and future signing keys at a certain interval. If your middleware and/or API gateways do not support this endpoint and require you to manually configure a*.cer file, you will need to coordinate the signing key rotation in Auth0 with the reconfiguration of your middleware and gateways.

