The world is obsessed with data. Companies, governments, academics — everyone is racing to collect and compile the largest data sets, believing the hype about their enormous value. While it's true that data can provide shrewd insights and help in directing an organization's strategy, research is beginning to show that more data isn't always better. In fact, there can be serious diminishing returns if your organization isn't set up to handle the volume of information, ranging from botched business analytics to irreversible damages from a data breach.
Master data management is a set of tailored processes and techniques that allow teams to consolidate their critical streams of information into a single file. This helps ensure that each IT system, platform, and architecture across your entire company can view and work with data in a coherent way. Moreover, a centralized management system allows for broader and tighter security measures to mitigate the risk of hackers acquiring user information in certain formats.
“Master data management is a set of tailored processes and techniques that allow teams to consolidate their critical streams of information into a single file.”
Tweet This
What Is Master Data Management?
Consider an example: You’re a fast growing e-commerce company. Every time a customer makes a purchase you collect their basic personal information, credit card information, a log of what they purchased, when, and occasionally from what device (e.g., mobile or desktop). This is all in addition to data you’ve already amassed on how often this user has visited your site, clicked through items, and placed items in their online cart.
Since you're continuing to expand, you’ve also cataloged all of your products—how many you’ve sold, how many are back-ordered, what your top sellers are, and during what time(s) of year you have the highest turnover. As you continue to scale, you’ve brought on new employees and store their credentials to determine their access to the company's sensitive information. You keep records of other physical assets, such as equipment and inventory. These inputs keep multiplying as you grow.
In an organized format, this information should underpin a deep understanding of your customer base and support the development of targeted marketing campaigns. It should provide the foundation for calculating your inventory turnover rate and return on assets (ROA) and display a host of growth metrics to stakeholders, such as customer acquisition cost (CAC) and monthly recurring revenue (MRR). However, at the moment, it's decentralized and in a variety of formats, including separate databases, spreadsheets, and even physical reports.
Well-orchestrated master data management sets clear protocol for how data is amassed, in what formats, and sets firm policies for who can access sensitive information.
Consolidating User Data With Auth0's Social Login
Auth0's social login feature provides an initial access point for master data management. Auth0 integrates with 30+ social providers to streamline the collection of user data, incorporating specific security measures throughout the process.
Social Login requires three simple steps:
- A user enters your application and selects their desired social network provider (e.g., Facebook).
- A login request is sent to the social network provider.
- The social network provider confirms the user’s identity, allowing new registration and access to your application.
Integrating with social network providers allows your organization access to additional up-to-date information, such as the new user's interests and recent events attended, location and check-ins, birthday, and even shopping history. This rich stream of information is located in a single place and format.
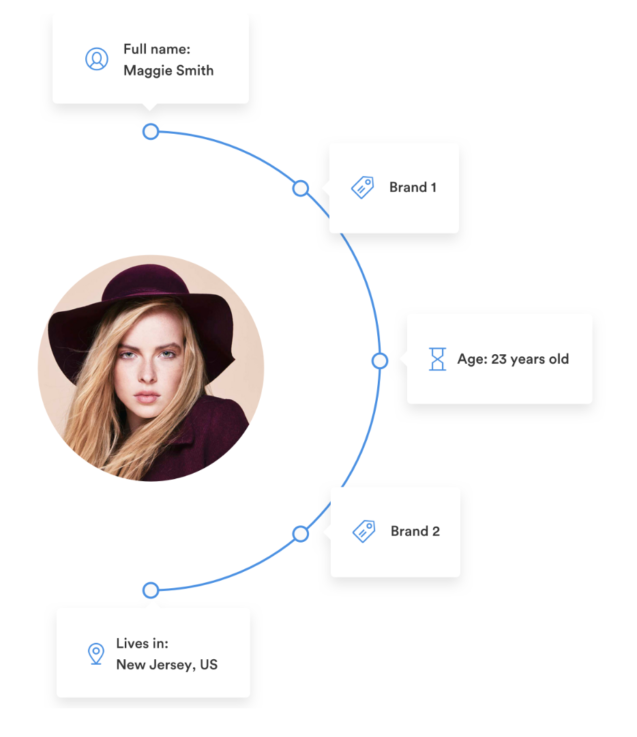
With streamlined information, you can create a comprehensive view of each of your customers:
A detailed understanding of your users will form the basis for showing them more personalized content.
Social Login also includes email verification. This means that the onus is on the social network provider to deliver you real email addresses, mitigating your risk of allowing dishonest users into your application. In 2016, Deloitte fell victim to a fake account. This made-up persona lured a Deloitte team member to open malicious documents, introducing malware designed to steal credentials into its system.
Employing a vetted identity access tool like Social Login will automatically streamline and secure an enormous volume of customer data. It will store the information in a standard format and create a cohesive view for your administrators to manage and for other team members to use for company insights.
Master Data Management and Complying with GDPR
Master data management is even more important now that GDPR finally entered into force. These new rules apply to all those in the EU who control data and/or undertake data processing. Consumers have greater rights under GDPR including:
- A new Right To Data Portability (i.e., the ability to copy and transfer personal data easily from one IT environment to another)
- An expanded Right To Be Forgotten (also called the Right to Erasure)
- A more comprehensive Subject Access Right (i.e., a clear means of requesting and obtaining all personal data from an organization)
Even if you're located outside of the EU, several related policies are taking shape worldwide to dovetail with these stringent guidelines. In particular, Argentina, Australia, Canada, Japan, California, and New York have all forged ahead with rules of similar intensity.
In order to be in compliance with fast-approaching regulatory changes and avoid fines in the event that your team is audited and not up to code, it's important to adopt a strategy for master data management. Regulators will want proof that you are organized, that you can quickly locate personal data when a customer requests it, and that you have efficient procedures in place to remove portions or entire personas.
“In order to be in compliance with fast-approaching regulatory changes and avoid fines in the event that your team is audited and not up to code, it's important to adopt a strategy for master data management.”
Tweet This
You will also have an enormous advantage over your competitors if you can explain how you manage their personal data. As users increasingly understand that they have the ability to determine what companies see and how they use sensitive information, they will likely have more questions about the process and how it relates to their security. Few companies are positioned to describe their techniques in detail. If you are one of the few who has implemented a tight and well- functioning master data management strategy, you can distinguish yourself and build user trust.
Conclusion
Master data management will be unique to each company, based on its structure, supply chain, the categories of data it collects, and the ways in which team members use it. However, starting with a strong and secure access point into your system will go a long way towards streamlining highly sensitive points, complying with stringent regulations, and consolidating layers of rich information into a practical view for more targeted strategies.
About the author

Martin Gontovnikas
Former SVP of Marketing and Growth at Auth0 (Auth0 Alumni)
Gonto’s analytical thinking is a huge driver of his data-driven approach to marketing strategy and experimental design. He is based in the Bay area, and in his spare time, can be found eating gourmet food at the best new restaurants, visiting every local brewery he can find, or traveling the globe in search of new experiences.View profile