Digital identity is at the core of any application - invisible yet crucial. We often take identity for granted as most of its magic happens behind the scenes. But identity plays a much larger role beyond the login screen for your applications. At a high level, we can break up identity into four distinct components: authentication, authorization, user profile, and security.
Authentication
Authentication dictates the way a user logs into your application. While in the past, a simple username and password form did the trick, today it is much more complicated. In addition to providing the traditional means of authentication, social connections through providers like Facebook and Twitter, enterprise federation and single sign on (SSO), and even passwordless authentication are becoming the norm. Implementing all of these various types of authentication methods in your application is a tiresome, repetitive, and expensive task.
Authorization
Authorization is tasked with ensuring the right users have the right access at the right time. Admins of your application should easily be able to make system wide changes, while regular users can only make changes to their accounts for example. From small businesses to large enterprises, access has to be fine tuned to ensure that the right users have access. Multiple departments, complex hierarchies and groups, and users moving throughout the system need up to date access to work effectively. Access is very important to making sure your application operates as intended and getting this aspect of identity right can be quite challenging.
User Profile
The user profile is concerned with the data that your application has collected on each individual user. The better you know your users the better experience and personalization you can provide. With disparate networks and various sets of data floating all around the web, it can be difficult to get a clear understanding of your users, but companies that can will have an upper hand.
Security
Finally, the security part of the modern identity story ensures that user data is protected both in motion and at rest. Security can be looked at through various lenses. The first, starts when a user attempts to login. Protecting user accounts at time of login with multifactor authentication, anomaly detection, and breached password detection are just some of the quick wins that will make your application more secure and stand out from the crowd. Ensuring data is protected at rest, passwords properly encrypted, and adherence to industry standards and certifications are other aspects of security that must be enforced.
Application Modernization and Identity
Looking at identity as a constantly evolving and unified view of your user base, rather than a one-and-done requirement, will help you understand the importance of this component in your application. Application modernization is the refactoring, repurposing or consolidation of legacy software to align it more closely with current business needs. Whether you call it application modernization, digital transformation, platform refactoring or re-architecting, the need to have a software that meets the needs of your business is a priority.
Read our initial application modernization post to learn more about why application modernization is sweeping the software industry. In today’s post, we will look at how you can kickstart your modernization journey by tackling identity first.
Identity has to be done right, not as an afterthought or side project, making it an ideal candidate for a service that needs to be separated out from the legacy behemoth applications. Identity requires ongoing efforts to secure and maintain but expertise is scarce. Much like how you generally wouldn’t build your own database or email platform, identity is best left to experts whose sole job is to ensure that your platform is as safe and secure as it can be, leaving your developers to focus on your organization's core competencies.
Modern Identity with Auth0
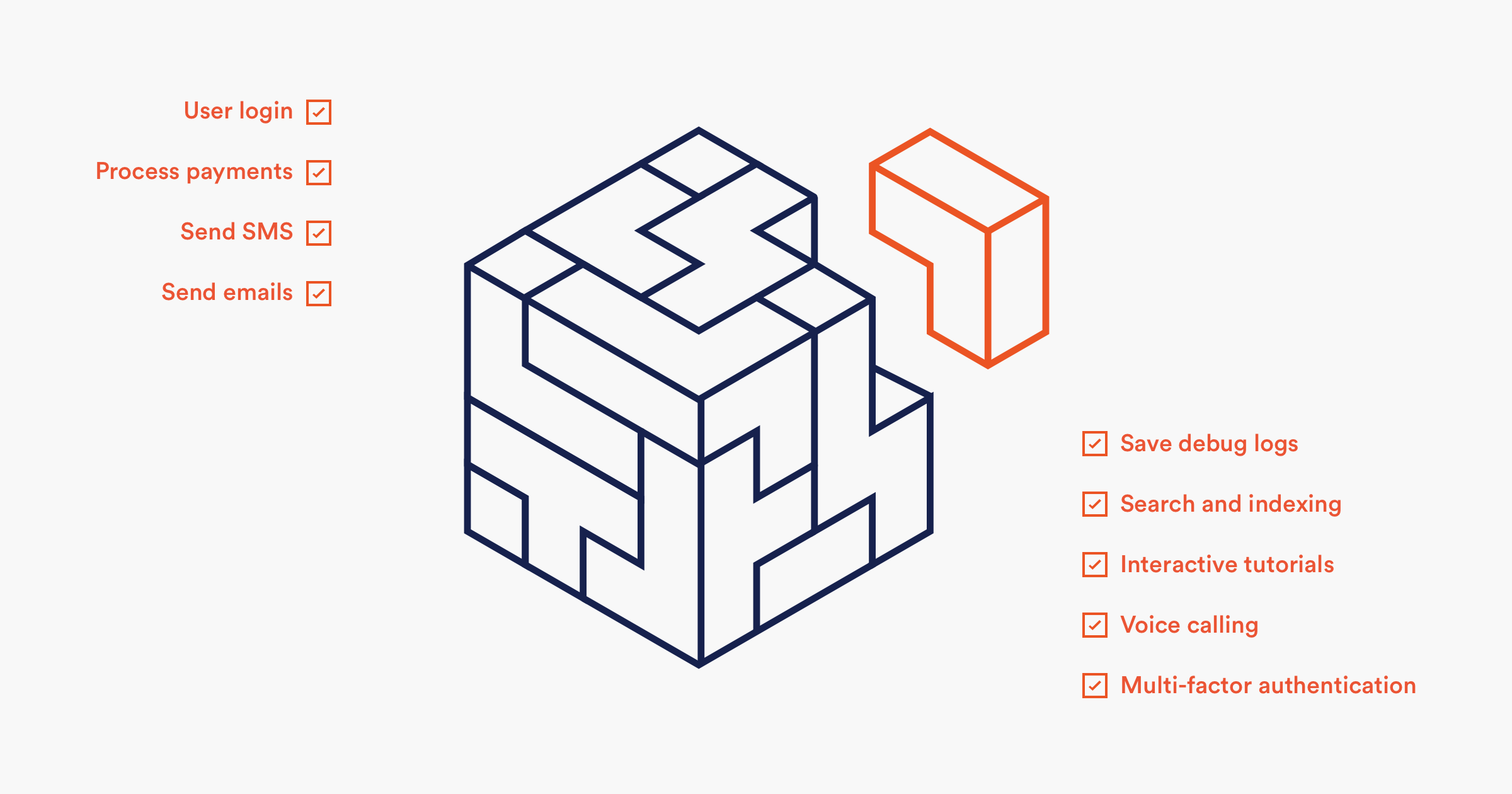
Auth0 is an Identity as a Service provider that takes a completely new approach to providing a modularized, pluggable identity service by simplifying the most complex identity challenges with a powerful, secure, extensible, and easy to integrate platform. Rather than re-inventing the wheel when it comes to identity, leveraging Auth0, can help you reach your goals faster.
Wherever you are in your digital transformation journey, Auth0 can help. Whether you are re-building your legacy application from scratch altogether or going about a phased restructuring of the legacy system, it’s ideal to offload a the critical part of the application, which not your core competency or expertise, externally as a cloud-based service. With Auth0, you can do just this, and the benefits will be immediate including:
- Code as an asset
- Stop every line of code from becoming a cost center - for maintenance, audit, upgrade and so on. The more you externalize using services, the lesser you actually pay. Auth0 provides identity as a service, ensuring your identity remains an asset - always.
- Ease of deployment and integration
- Auth0 Identity works with any technology stack, language, and framework. Get your identity system up and running quickly within your existing ecosystem, and get back to modernizing the rest of the app.
- Easy configuration to meet your needs
- Once Auth0 is integrated into your app, adding additional configuration, like multifactor authentication, anomaly detection, or breached password detection, is as easy as flipping a switch.
- Support for virtually any identity source
- Username and password, social connection, enterprise federation, and single sign on (SSO). Auth0 allows quick and easy integration with any identity source you choose.
- Flexible deployment
- Your apps are evolving but you still have legacy systems to work with. Auth0 gives you flexible deployment options - our public cloud, a private cloud controlled by Auth0, or, for AWS users, a private deployment in your own cloud.
Implementing a modern identity solution will present many benefits to your business. Providing your users multiple ways to access your application on their terms will lead to increased conversion rates. Having a better understanding of your users will allow you to provide a more personalized and enhanced user experience, increased user efficiency, and better management. Going above and beyond to protect your user data will build trust and loyalty as well.
Your users are not the only ones that will benefit. You will be able to react to market events faster, gain a deeper understanding of your users, and your developers will be able to focus on building software that makes your product stand out. Over 80% of Auth0 customers were able to go to production within two weeks and with over 42 million login transactions processed daily, Auth0 is ready to serve your users today regardless of where you are in your application modernization journey.
Summary
The question is no longer “should we or shouldn’t we”, but rather “how do we modernize our platform” for current and future needs. The software industry is going through a radical transformation and legacy monolithic applications are no longer compatible with today’s business needs and user expectations. Application modernization is not something that can be achieved overnight and there are many paths to the end goal, but starting with identity is a surefire win-win for both your organization and your users.
About the author

Ado Kukic
Former Auth0 Employee (Auth0 Alumni)