Choice is good. We like it when our supermarket shelves are stocked with hundreds of varieties of breakfast cereal. We pick the smartphones we use and the cars we drive. The same should be true for businesses and the technologies they use.
Today, we brought the Auth0 Identity Platform to Microsoft Azure, giving our private cloud customers the ability to pick the right infrastructure provider for their needs.
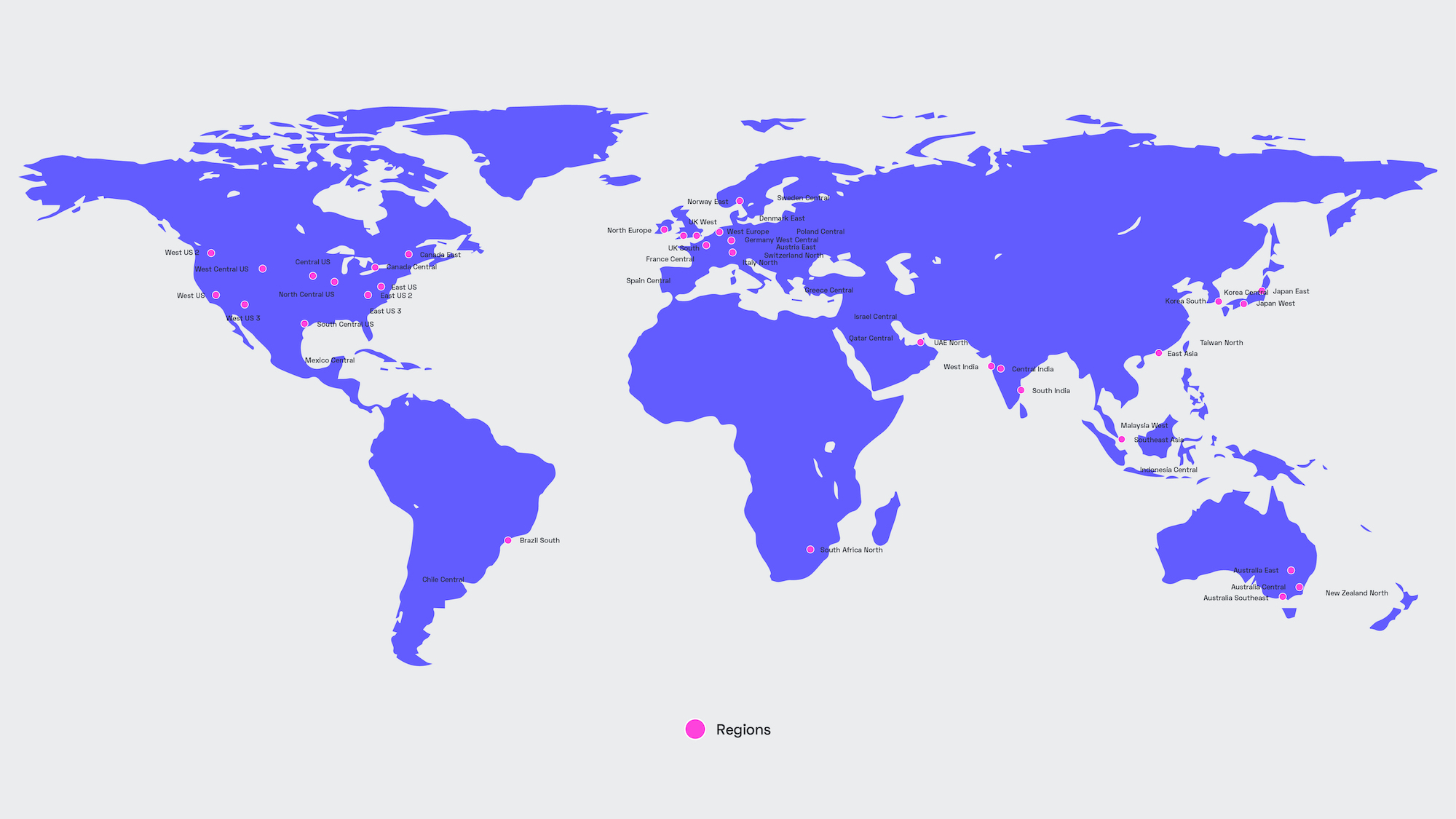
This means a greater selection of regions. Microsoft currently operates in over 60 regions around the world, making it easier to comply with data residency and sovereignty requirements.
And if you’re already running your app on Azure’s cloud servers, you’ll benefit from a converged infrastructure, with every component running on the same underlying cloud platform.
Shifting Security Left on Microsoft Azure
We’re equally excited to tell you about the development process. Auth0 has always prioritized security. Last year, we took this a step further with the adoption of “Shift-Left” principles. This puts security-related tasks at the start of the Software Development Life Cycle (SDLC), making it easier to build a stronger, more resilient product.
We remained true to these principles when building the Auth0 Identity Platform for Microsoft Azure, and are thrilled with the end result. The final product is one that reflects our Secure by Design philosophy and faithfully adheres to industry best practices.
Let’s talk about what “Shift-Left” means. This is an established term in the software development sphere, and refers to a variety of domains, both security-related and otherwise. In short, you take something that would typically happen at the end of the development lifecycle and tackle it at the beginning. Test-driven development (TDD) is a notable example.
As Auth0’s CISO Jameeka Aaron said: “Nobody wants their CISO to show up at the last minute with 800 vulnerabilities to be fixed before release.” Our security engineering team looks for vulnerabilities during the design and development phases, and remediates issues early on to prevent a last-minute crunch, or worse, having to rework the design.
At Auth0, our Shift-Left process tackles both the human and technical elements of secure software development. All code must meet strict security requirements and is constantly tested against sophisticated static analysis benchmarks.
We also provide all developers with secure coding training, with some designated as “security champions.” These employees act as liaisons between the engineering and our dedicated platform security teams. They also receive additional training to act as security advocates within their teams.
Security First Architecture
As we developed the Auth0 Identity Platform for Microsoft Azure, we emphasized “shift-left” principles and focused on building a strong security architecture at the start of the development cycle.
We established a dedicated Azure AD tenant and automated governance controls to support resource and identity isolation, required MFA and Azure PIM for privileged access, and enforced security standards with Azure Policy. Prioritizing security in the early stages of the development process is part of our Secure by Design strategy to mitigate risk and keep customers safe from cyberthreats.
The Security Engineering team is also responsible for Azure customer account provisioning and management. In Azure, these are called subscriptions. These are used to isolate private cloud environments and all the associated provisioned resources, like VMs, data storage, and more.
We built a new service for managing Azure subscriptions, and it is integrated directly into our platform infrastructure workflows. This helped to automate how we manage our Azure Private Cloud environments and dramatically improved environment creation time. This was another part of our Azure governance to keep customer environments isolated and secure.
Cloudflare on the Edge
To help protect against network-based attacks, the Auth0 Identity Platform uses Cloudflare — a popular reverse proxy and content delivery network (CDN) product.
Cloudflare acts as a gateway between the application and the outside world. The service proactively analyzes all inbound traffic, and blocks things that could harm the smooth functioning of the Azure instance, including malicious bots and DDoS attacks. Further protection comes from its customizable rate limiting and firewall rules.
This means a better, more reliable service for your users. It also comes with some significant performance advantages, too. With Cloudflare's CDN, static assets (like images and scripts) are hosted close to the user, thereby reducing load times. Traffic is routed through Cloudflare's Anycast network, which consists of over 250 locations in 100 countries, and provides greater resiliency and latencies below 50ms.
Detection & Response
In the hands of an IT engineer, security professional, or developer, logs are a powerful tool. They're the first place you look when remediating a fiendishly tricky problem, or trying to identify an attempted intrusion.
When building the Auth0 Identity Platform for Microsoft Azure, we wanted to make it easy to audit and monitor. Logging is enabled by default on all Azure instances, as well as with the back-end databases. By default, we retain logs for 13 months.
Each Azure environment is covered by Auth0's host monitoring agents. This monitors the security, performance, configuration and state of each host. We also enabled Azure Security Center & Defender by default, further bolstering our security monitoring capabilities.
Disaster Recovery
Identity is fundamental to business. Your CIAM system is the gateway between your application and its users. You can’t afford significant downtime. With this in mind, we spent a lot of time thinking about resilience when designing the Auth0 Identity Platform for Microsoft Azure.
All services are provisioned across three Availability Zones (AZ). In the case of an AZ failure, service are designed to automatically resume in one of the other healthy AZs. Backups are captured every six hours and securely retained in the same region as the deployment, and we can restore an instance from the last snapshot in four hours.
Azure’s Solid Foundations
Let’s wrap up by talking about Microsoft Azure itself. After all, what’s the point in building a secure platform if the underlying infrastructure isn’t up to standard?
Fortunately, there’s no such concerns here. We have come to appreciate the security features and tools within the underlying Azure platform and ecosystem. Microsoft also has the right mindset. The Azure access control best practices urge users to regard identity as the primary security perimeter. This reflects the changes in enterprise IT, particularly the rise of BYOD and cloud computing, which make it harder to build watertight network defenses.
Identity is the best way to protect your most important data. Well-defined permissions can limit the impact of a security breach, while using MFA and SSO can help prevent an account being compromised in the first place. To find out how the Auth0 Identity Platform on Microsoft Azure can benefit your organization, click here.
About the author

David Telehowski
Director, Security Engineering
