How it works
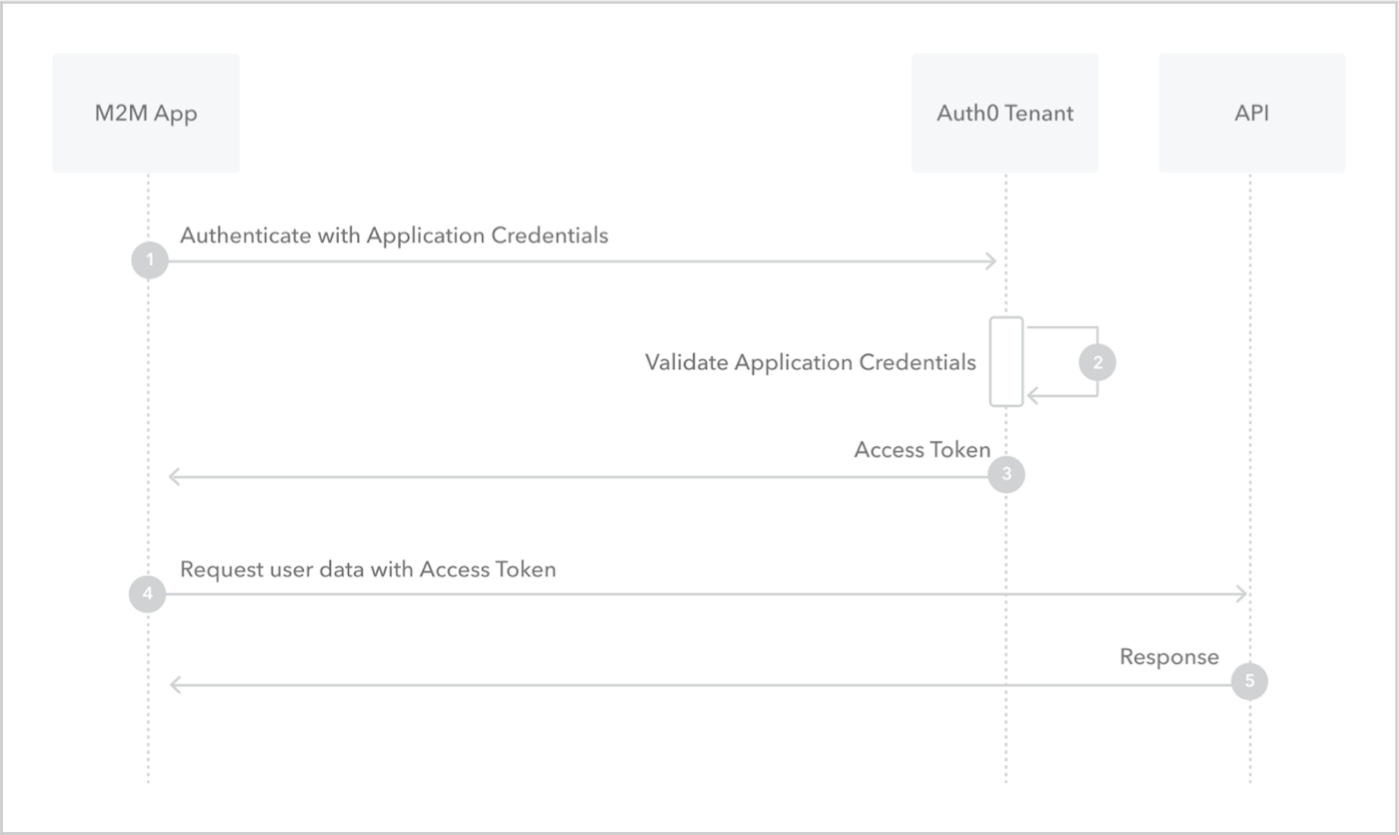
- Application sends application’s credentials to the Auth0 Authorization Server. To learn more about client authentication methods, read Application Credentials.
- Auth0 Authorization Server validates application’s credentials.
- Auth0 Authorization Server responds with an access token.
- Application can use the access token to call an API on behalf of itself. For more information on this process, see Validate JSON Web Tokens.
- API responds with requested data.

