You can use Connect (OIDC) with many different flows to achieve web sign-in for a traditional web app. In one common flow, you obtain an using authorization code flow performed by the app backend. This method is effective and robust, however, it requires your web app to obtain and manage a secret. You can avoid that burden if all you want to do is implement sign-in and you don’t need to obtain for invoking APIs. Implicit Flow with Form Post flow uses OIDC to implement web sign-in that is very similar to the way and WS-Federation operates. The web app requests and obtains tokens through the front channel, without the need for secrets or extra backend calls. With this method, you don’t need to obtain, maintain, use, and protect a secret in your application.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
How it works
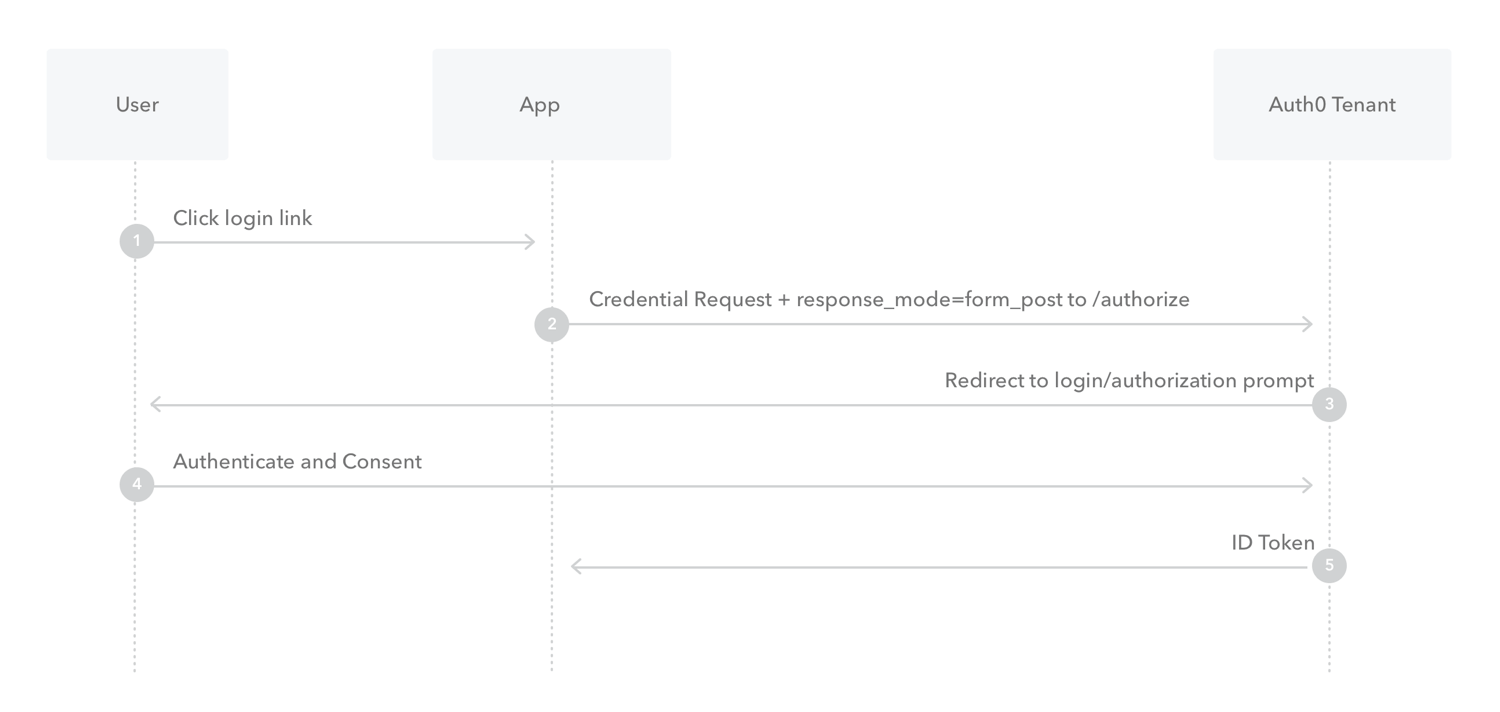
- The user clicks Login in the app.
- Auth0’s SDK redirects the user to the Auth0 Authorization Server (
/authorizeendpoint) passing along aresponse_typeparameter ofid_tokenthat indicates the type of requested credential. It also passes along aresponse_modeparameter ofform_postto ensure security. - Your Auth0 Authorization Server redirects the user to the login and authorization prompt.
- The user authenticates using one of the configured login options and may see a consent page listing the permissions Auth0 will give to the app.
- Your Auth0 Authorization Server redirects the user back to the app with an ID Token.
How to implement it
You can use our Express OpenID Connect SDK to securely implement the Implicit Flow with Form Post.The Auth0 Single-Page App SDK and Single-Page Quickstarts adhere to the new recommendations and use the Authorization Code Flow with PKCE.

