blocks traffic from any IP address that rapidly attempts too many logins or signups. This helps protect your applications from high-velocity attacks that target multiple accounts. Suspicious IP throttling is enabled by default when you create your Auth0 tenant. When Auth0 detects a high number of signup attempts or failed login attempts from an IP address, it responds to subsequent attempts with the HTTP 429 Too Many Requests status code until that IP address is no longer throttled. For more information on signup and failed login attempts logged by your tenant, read Log Type Codes.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Configure Suspicious IP Throttling
You can configure Suspicious IP Throttling in the Auth0 Dashboard or with the Auth0 Management API.- Go to Dashboard > Security > Attack Protection, and select Suspicious IP Throttling.
- Select the toggle at the top of the page to enable or disable Suspicious IP Throttling.
Allow trusted IP addresses exceed throttling limits
You can make up to 100 discrete IP addresses and/or CIDR ranges (IPv4 or IPv6) exempt from Suspicious IP Throttling by adding them to the IP AllowList. Auth0 does not block or alert tenant administrators when these IP addresses exceed the throttling limits.- Go to Dashboard > Security > Attack Protection, and select Suspicious IP Throttling.
- In the IP AllowList field, enter the IP addresses and/or CIDR ranges you want to allow unlimited login and signup attempts. Separate multiple IP addresses and/or CIDR ranges with commas.
Configure response
By default, Auth0 sends email to tenant administrators when an IP address is marked as suspicious. You can configure how Auth0 responds to high-velocity login or signup attempts.- Go to Dashboard > Security > Attack Protection, and select Suspicious IP Throttling.
- Locate the Response section.
- In the Block Settings section, enable Limit high-velocity traffic targeting too many accounts to throttle traffic from IP addresses that exceed the login or signup threshold.
- In the Notifications section, enable Send notification to account administrator to automatically send an email to tenant administrators when an IP address exceeds the login or signup threshold.
- Select Save.
Configure throttling limits and rates
You can customize how Auth0 throttles suspicious IP addresses. You can change:- The maximum number of failed login and signup attempts allowed from a given IP address.
- The rate at which throttled IP addresses allow new login and signup attempts.
-
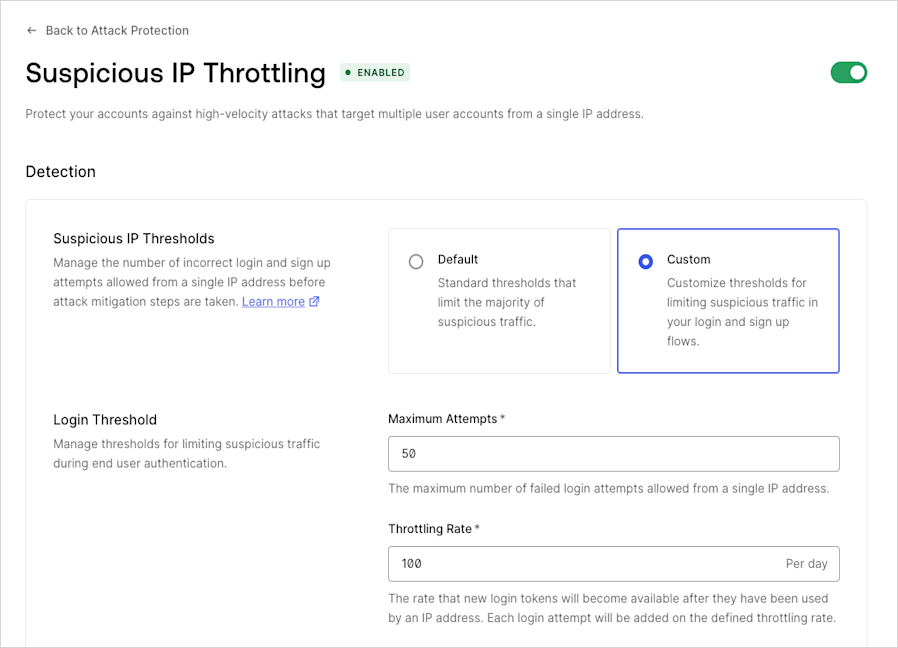
Go to Dashboard > Security > Attack Protection, and select Suspicious IP Throttling.
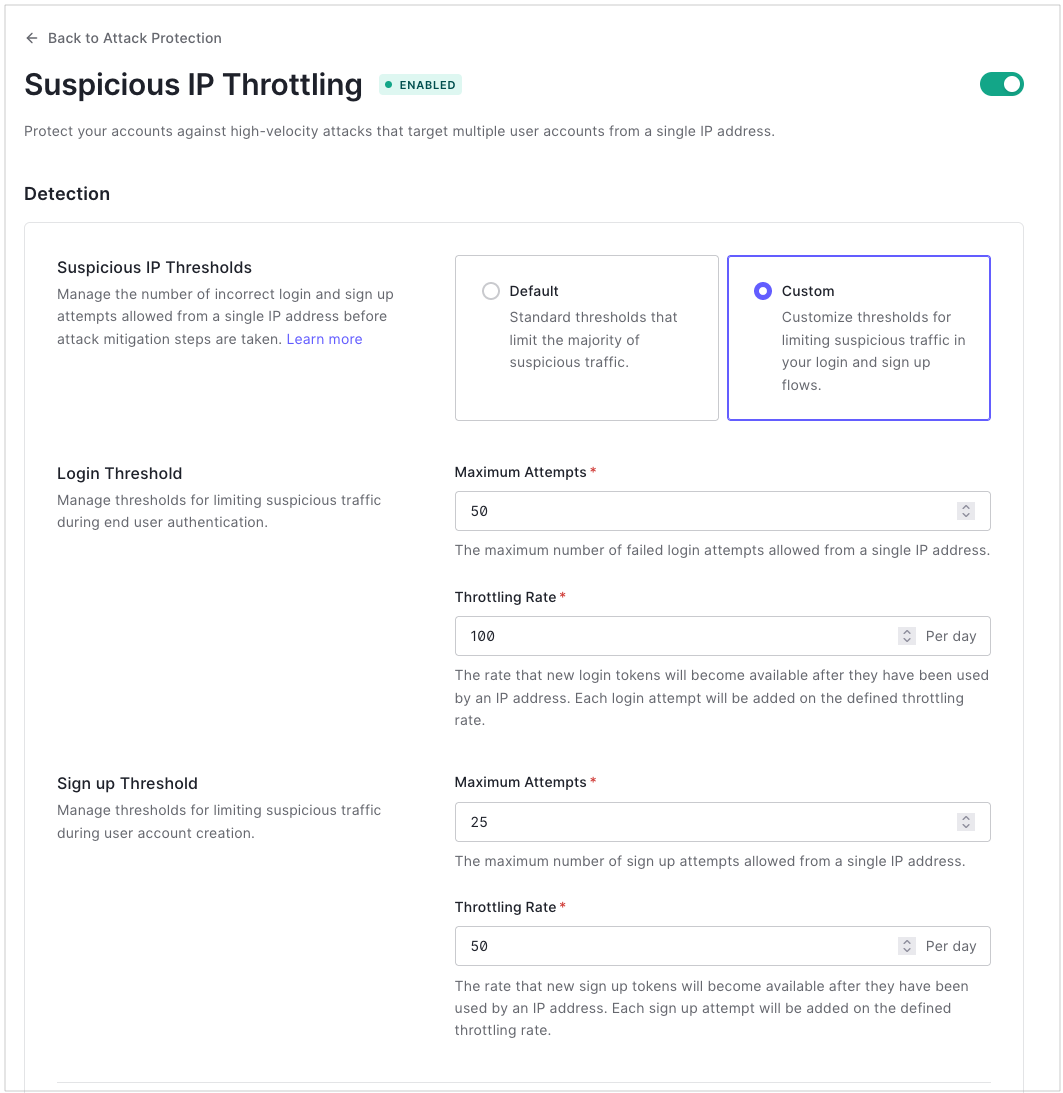
- Locate the Detection section.
- Select Custom for Suspicious IP Thresholds.
-
Configure the Login Threshold settings:
- Maximum Attempts: Enter the number of failed login attempts a single IP address can make in one day before Auth0 blocks the next attempt.
- Throttling Rate: Enter the rate at which to grant new login tokens.
-
Configure the Signup Threshold settings:
- Maximum Attempts: Enter the number of signup attempts a single IP address can make in one minute before Auth0 blocks the next attempt.
- Throttling Rate: Enter the rate at which to grant new signup tokens.
- Select Save.
How suspicious IP throttling works
Auth0 counts and allows login and signup attempts separately. IP addresses suspended from further login attempts can still try to sign up. IP addresses suspended from further signup attempts can still try to log in.Login attempts
Auth0 throttles any IP address that attempts and fails too many logins in a day. The login throttling rate determines how many login attempts Auth0 grants to an IP address evenly over 24 hours. For example, a throttling rate of 100 means that Auth0 grants a new attempt approximately every 15 minutes.Signup attempts
Auth0 throttles any IP address that attempts too many total signups in a minute. For example, if an IP address makes 50 signup attempts, Auth0 blocks further attempts. Unlike logins, the signup attempts do not need to be failures. The signup throttling rate determines how many signup attempts Auth0 grants to an IP address evenly over 24 hours. For example, a throttling rate of 72,000 means that Auth0 grants a new attempt approximately every second.Malformed requests and schema validation errors
Login and signup requests that do not follow the proper structure or formatting are not considered valid attempts, and therefore do not count toward your configured threshold. For more information about login and signup requests, read Auth0 Authentication API.Special cases
Because suspicious IP throttling depends on the IP address of the user, the following use cases require additional configuration:- Using the Password Grant from the backend of an application: Using this call does not get the IP address of the user; however, to make suspicious IP throttling work correctly, you can configure your application to send the IP address of the user as part of the request. See Avoid Common Issues with Resource Owner Password Flow and Attack Protection: Send the user’s IP address from your server.
- Authenticating a large number of users from the same IP address: Users who are behind a proxy are more likely to reach set limits and trigger throttling. You can avoid erroneously triggering throttling by configuring an AllowList for the proxy’s IP and CIDR range. See Avoid Common Issues with Resource Owner Password Flow and Attack Protection: Configure your Application to trust the IP address.

