Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Before you register any APIs in the Auth0 Dashboard, one API will already exist: the Auth0 Management API. To learn more about the features of the Management API and its available endpoints, see Management API.
- Go to Dashboard > Applications > APIs, and select + Create API.
-
Provide the following information for your API, and click Create:
Field Description Example Name A friendly name for the API. Does not affect any functionality. yourDomainIdentifier A unique identifier for the API. Auth0 recommends using a URL. Auth0 does differentiate between URLs that include the last forward slash. For example, https://example.comandhttps://example.com/are two different identifiers. The URL does not have to be a publicly available URL. Auth0 will not call your API. This value cannot be modified afterwards.https://{yourDomain}JSON Web Token (JWT) Profile The profile determines the format of the access tokens issued for the API. The available values are Auth0andRFC 9068. To learn more, read Access Token Profiles.Auth0JSON Web Token (JWT) Signing Algorithm The algorithm to sign the access tokens with. The available values are HS256,PS256,RS256. If you selectRS256, the token will be signed with the tenant’s private key.RS256Access Policy for Applications within user flow Allow applications to access the API on the user’s behalf. To learn more read, API Access Policies for Applications. Allow via client-grantAccess Policy for Applications within client flows Allow Machine to Machine applications to access the API. To learn more read, API Access Policies for Applications. Allow via client-grant -
Make the implementation changes to your API that are described in the QuickStart. These changes consist of choosing a JWT library from a predefined list and configuring this library to validate the access tokens in your API.
- Settings: Lists the settings for your API. Some are editable. Here you can change the token expiration time and enable offline access (this way Auth0 will allow your applications to ask for for this API).
- Scopes: Define the scopes for this API by setting a name and a description.
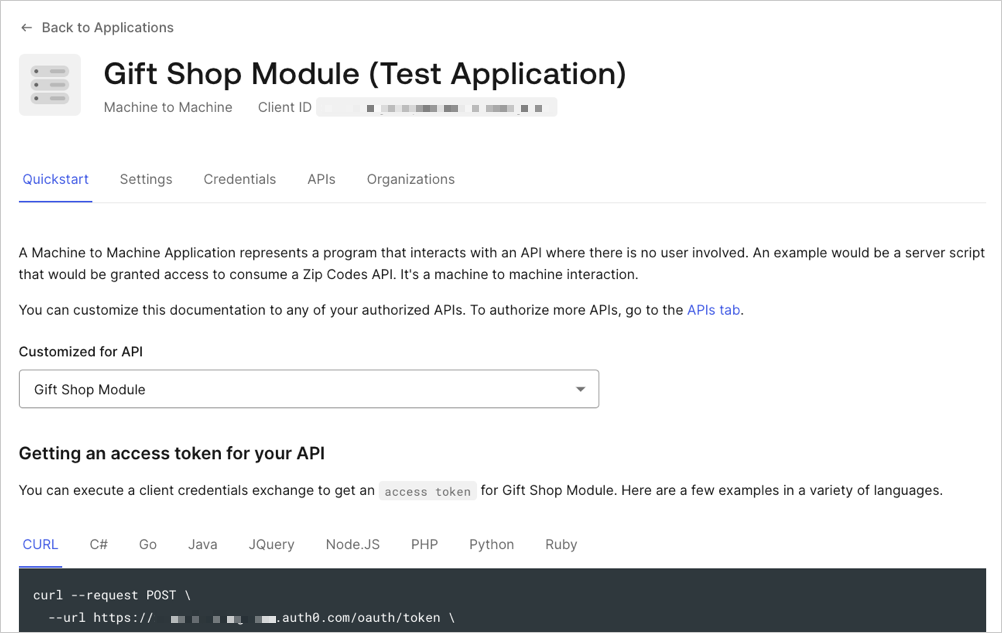
- Machine to Machine Applications: Lists all applications for which the Client Credentials grant is enabled. By default, this grant is enabled for regular web applications and machine-to-machine applications. You can authorize any of these applications to request for your API. Optionally, you can select a subset of the defined scopes to limit your authorized application’s access.
- Test: Execute a sample client credentials flow with any of your authorized applications to check that everything is working as expected.

