(JWT), pronounced “jot”, is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. Again, JWT is a standard, meaning that all JWTs are tokens, but not all tokens are JWTs. Because of its relatively small size, a JWT can be sent through a URL, through a POST parameter, or inside an HTTP header, and it is transmitted quickly. A JWT contains all the required information about an entity to avoid querying a database more than once. The recipient of a JWT also does not need to call a server to validate the token.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Benefits
- Compact: JWTs are small in size, which makes them a good choice to be passed in HTML and HTTP environments.
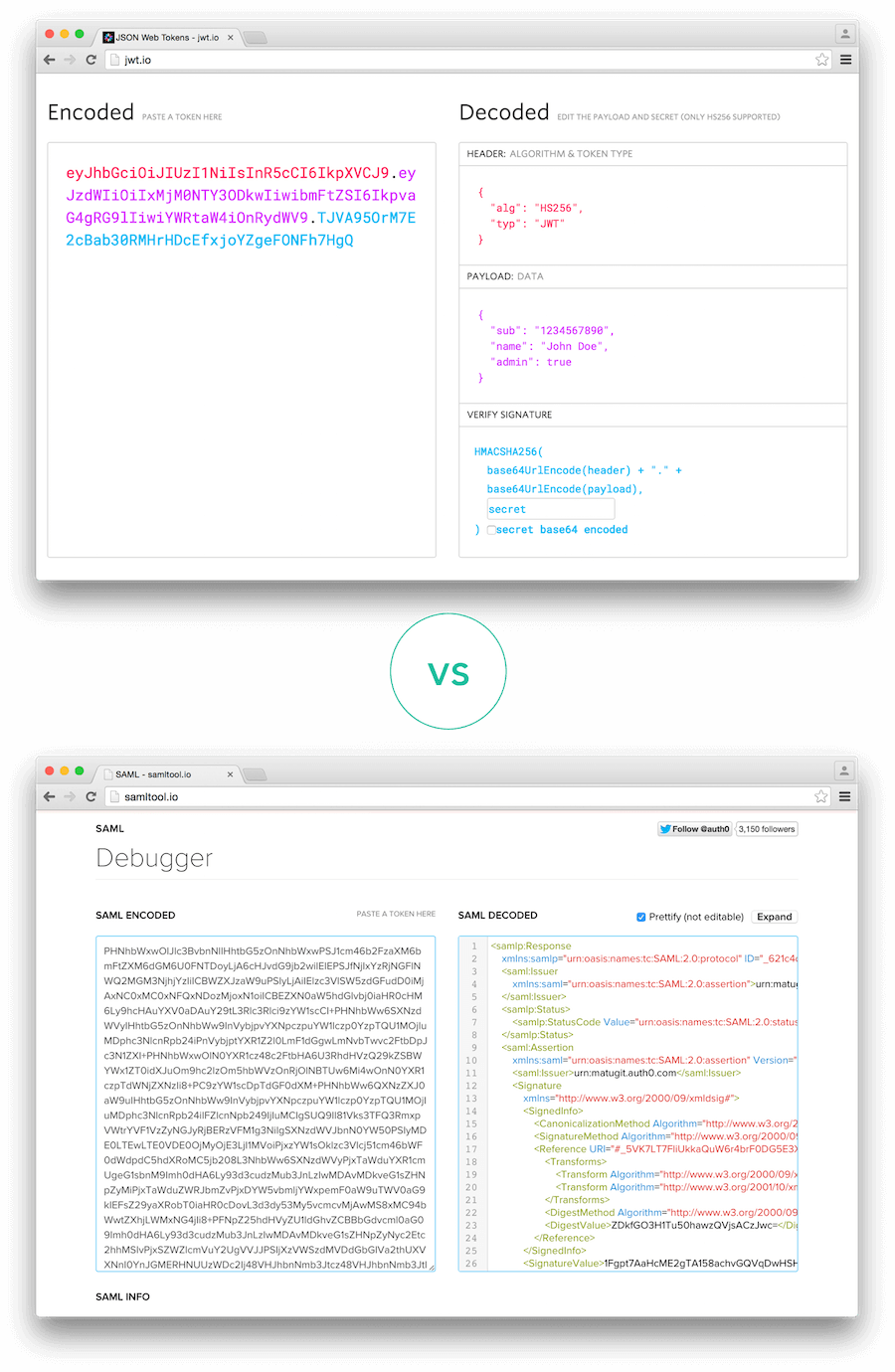
- Secure: JWTs can use a public/private key pair in the form of an X.509 certificate for signing. A JWT can also be symmetrically signed by a shared secret using the HMAC algorithm. To learn more, read Signing Algorithms.
- Common: JSON parsers are supported by most programming languages.
Usage
- Authentication: When a user successfully logs in using their credentials, an ID token is returned. According to the OpenID Connect (OIDC) specification, an is always a JWT.
- Authorization: Once a user is successfully logged in, an application may request to access routes, services, or resources (for example, APIs) on behalf of that user. To do so, the application must pass an in every request, which may be in the form of a JWT.
- Information exchange: JWTs are a good way of securely transmitting information between parties because they can be signed, which means you can be certain that the senders are who they say they are. Additionally, the structure of a JWT allows you to verify that the content hasn’t been tampered with.

