You can enable (MFA) for your tenant in the . When you enable MFA, select the factors (such as push notifications or phone messages) you intend to make available to users and define a policy to determine when you require them to authenticate.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Select factors
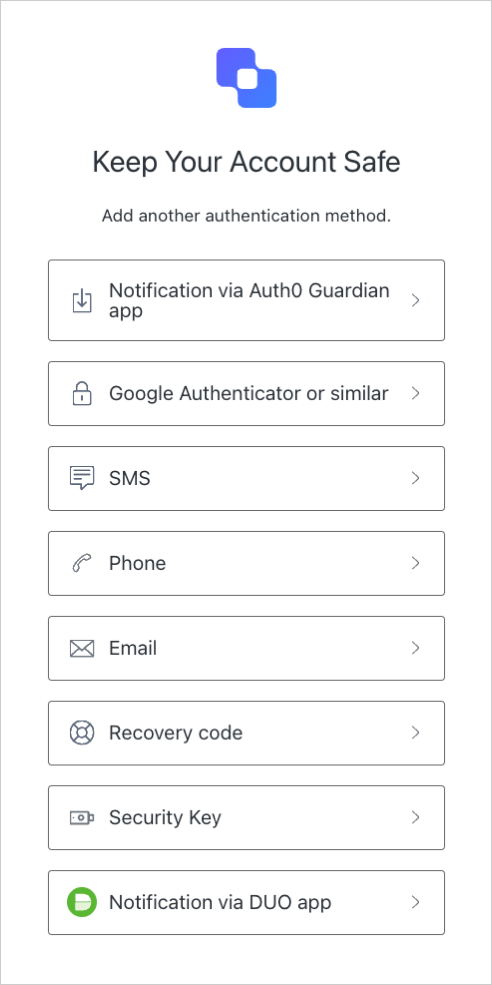
Auth0 supports a variety of factors you can enable for your users to complete authentication.Independent factors
You must enable and configure at least one independent factor to require MFA for users on your tenant. You may enable multiple independent factors simultaneously as you’d like. Available independent factors are:- WebAuthn with FIDO Security Keys
- One-time Password (OTP)
- Push Notification using Auth0 Guardian
- Phone Message
- Cisco Duo Security
Dependent factors
You may enable one or more dependent factors once you’ve already enabled and configured at least one independent factor for users on your tenant. Available dependent factors are:Enable MFA in the Auth0 Dashboard
- Go to Dashboard > Security > Multi-factor Auth.
- In the Factors section, enable and configure the factors you’d like to make available to users.
-
In the Define policies section, select a policy to determine when users will be prompted for MFA.
- Never: MFA is not required for any logins.
- Use Adaptive MFA: MFA is required based on Auth0 risk determination. To learn more, read Enable Adaptive MFA.
- Always: MFA is required for all logins.
- If you choose the Never or Always policy, the MFA Risk Assessors section appears. By default, the Enable Adaptive MFA Risk Assessment setting is disabled. Enable the toggle to assess and record risk for all login transactions in your tenant logs.
-
In the Additional Settings section, configure the following options as needed:
-
Show Multi-factor Authentication options: Enable this toggle to allow users to select authentication factors upon enrollment. When disabled, Auth0 automatically presents the most secure authentication factors to users upon enrollment.
-
Customize MFA Factors using Actions: Enable this toggle to customize your MFA flows using
post-loginActions. This allows you to challenge users with a specific factor or sequence of factors, as well as use contextual information to create more individualized experiences. To learn more, review Customize MFA Selection for Universal Login.
-
Show Multi-factor Authentication options: Enable this toggle to allow users to select authentication factors upon enrollment. When disabled, Auth0 automatically presents the most secure authentication factors to users upon enrollment.
- Click Save.

