Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
By Evan Sims
This guide demonstrates how to integrate Auth0 with a PHP backend API using the Auth0 PHP SDK.We recommend that you log in to follow this quickstart with examples configured for your account.New to Auth0? Learn how Auth0 works and read about implementing API authentication and authorization using the OAuth 2.0 framework.
Configure Auth0 APIs
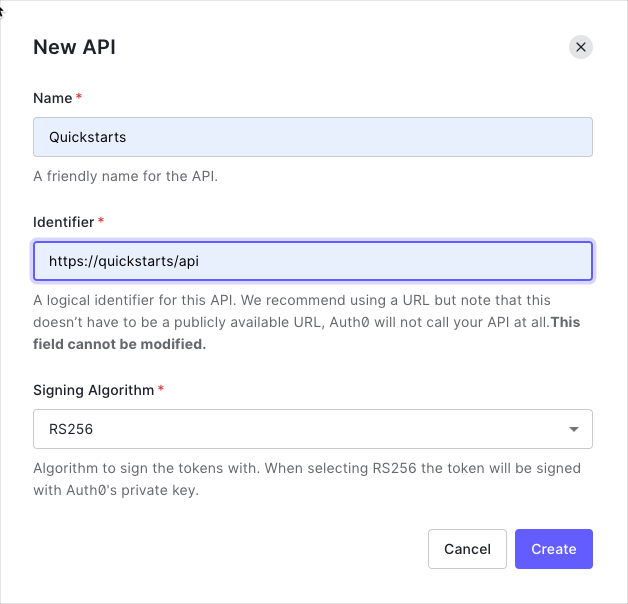
Create an API
In the APIs section of the Auth0 dashboard, click Create API. Provide a name and an identifier for your API, for example,https://quickstarts/api. You will use the identifier as an audience later, when you are configuring the Access Token verification. Leave the Signing Algorithm as RS256.
Define permissions
Permissions let you define how resources can be accessed on behalf of the user with a given access token. For example, you might choose to grant read access to themessages resource if users have the manager access level, and a write access to that resource if they have the administrator access level.
You can define allowed permissions in the Permissions view of the Auth0 Dashboard’s APIs section.
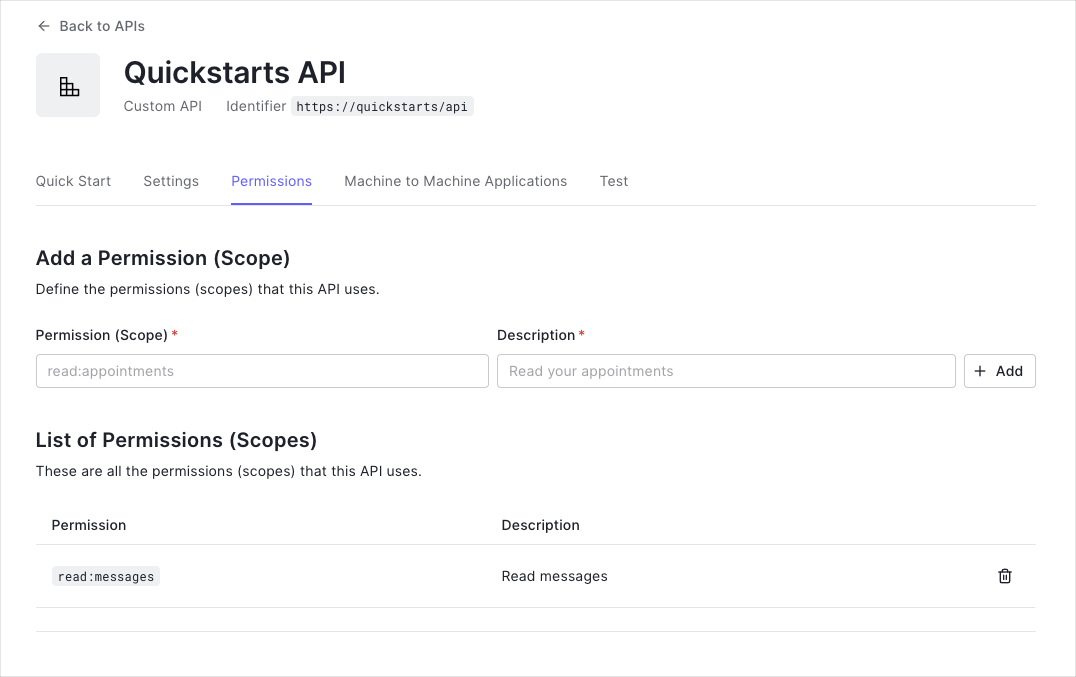
This example uses the
read:messages scope.- How to check for a JSON Web Token (JWT) in the
Authorizationheader of an incoming HTTP request. - How to check if the token is valid, using the JSON Web Key Set (JWKS) for your Auth0 account. To learn more about validating Access Tokens, see Validate Access Tokens.
Integrating your PHP Backend API
Let’s create a sample application that authorizes an Auth0-signed token with a backend API we’ve written in PHP. We’ll take a simple approach here, appropriate for the written format. Still, you should check out the accompanying Quickstart app on GitHub for a more robust example.Installing HTTP Client and Messaging Factories
The Auth0 PHP SDK supports many PHP-FIG standards to offer maximum interoperability with your project’s architecture, but two of particular importance are PSR-17 and PSR-18. These standards allow you to “plugin” networking components of your choice to handle messaging and requests. You will need to install compatible libraries in your project for the SDK to use. The most prolific networking library for PHP is Guzzle, although many are available to pick from within the PHP community. Let’s use Guzzle for this sample application:Installing the PHP SDK
The Auth0 PHP SDK requires Composer, a tool for dependency management in PHP. Composer allows you to declare the dependent libraries your project needs and installs them for you. Please ensure Composer is installed and accessible from your shell before continuing. Run the following shell command within your project directory to install the Auth0 PHP SDK:vendor folder within your project and download all the dependencies needed to use the Auth0 PHP SDK. This will also create a vendor/autoload.php file used in the sample to load all necessary classes for your application to function. It’s important you require this autoload file in your project for the SDK to work.
Configure the SDK
To begin, let’s create a.env file within the root of your project directory to store our sample application’s configuration and fill in the environment variables:
As PHP isn’t able to read our .env file by itself, we’ll want to install a library to help with that. Although we’ll be using a particular library for our sample application’s purposes, any ‘dotenv’ loader of preference will work in a real-world application. From our project directory, let’s run the following shell command to install the library:
index.php, and let’s configure an instance of the Auth0 PHP SDK for our sample application:
Authenticating the user
For this sample application, we’re focusing on authorization. There’s numerous routes you could go for authenticating your users before they hit your backend API for authorization, such as using Auth0s SPA.js library. This approach is demonstrated in this Quickstart app accompanying Github project. Regardless of the approach you take, this sample application expects you to pass your Access Token to it through a request parameter or header to work.Authorizing an Access Token
First, we need to extract the JSON Web Token (JWT) from the incoming HTTP request. Let’s look for a?token parameter in a GET request or an HTTP_AUTHORIZATION or Authorization header.

