As digital assets increase in value (in some cases, being the most valuable assets a company owns), threats become more profitable to criminals too. The largest ransomware payout made by an insurance company ($40 million) to date happened in 2021, and the trend doesn’t show any signs of slowing down.
The major problem with attacks like these is that computers today are so fast and interconnected that malware can harness those resources to spread itself throughout the network and encrypt an enormous amount of files before the victim can respond.
Unfortunately, after the files have been encrypted, there is not much that can be done. Most modern ransomware has good, or at least good-enough implementation of encryption algorithms, all but guaranteeing that the victim won’t be able to recover their data.
How Ransomware Works
The first versions of ransomware were poorly implemented, and the victim stood a decent chance of recovering their files without paying the ransom.
Since the virus had to encrypt the victim’s files as fast as possible to increase the chances of a successful attack, it relied on a symmetric cipher, such as AES, as they encrypt data much faster than asymmetric ciphers.
The problem is that symmetric ciphers use the same key to encrypt and decrypt the files.
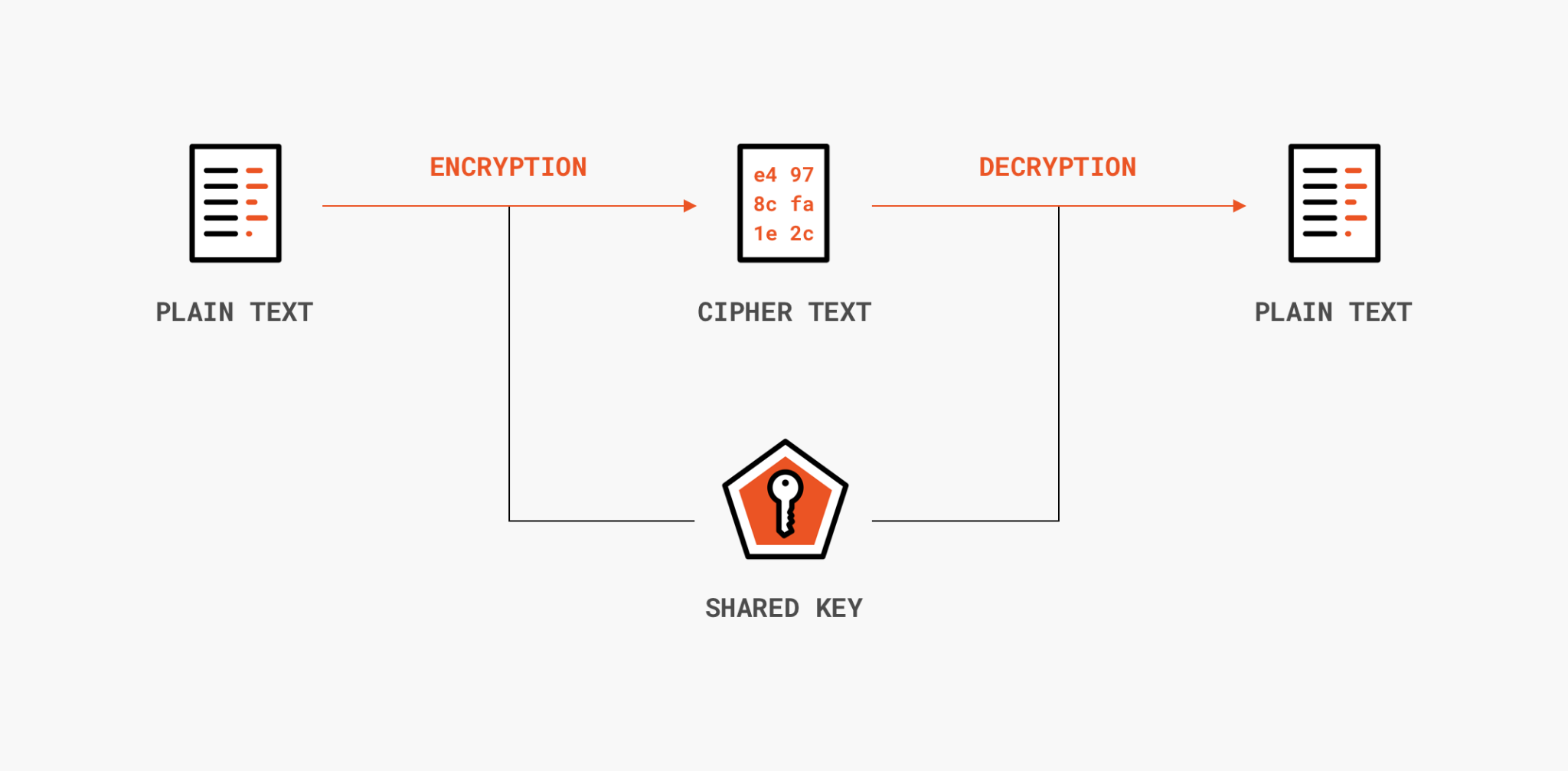
Symmetric cipher encryption
The bad actor would have to hard code the key into the malware and hope that the victim wouldn’t have the means to look for the keys in the code, or they would have to send a copy to a remote server which they controlled and delete the key on the victim’s computer. Neither option is very good for the attacker.
Most modern ransomware uses a hybrid encryption mechanism. While asymmetric ciphers are slow and not meant to encrypt huge amounts of data, using them to encrypt just the encryption key created by a symmetric cipher is not a problem.
Here’s how it works. Before the attack, the attacker generates an asymmetric key pair, and the public key is embedded into the malware. Once the malware is executed, it encrypts the victim’s files with a fast, symmetric cipher, and its key will then be encrypted with the public key from earlier.
To get their files back, the victim would need the attacker’s private key to decrypt the public key to then, finally, decrypt the files using the symmetric cipher key.
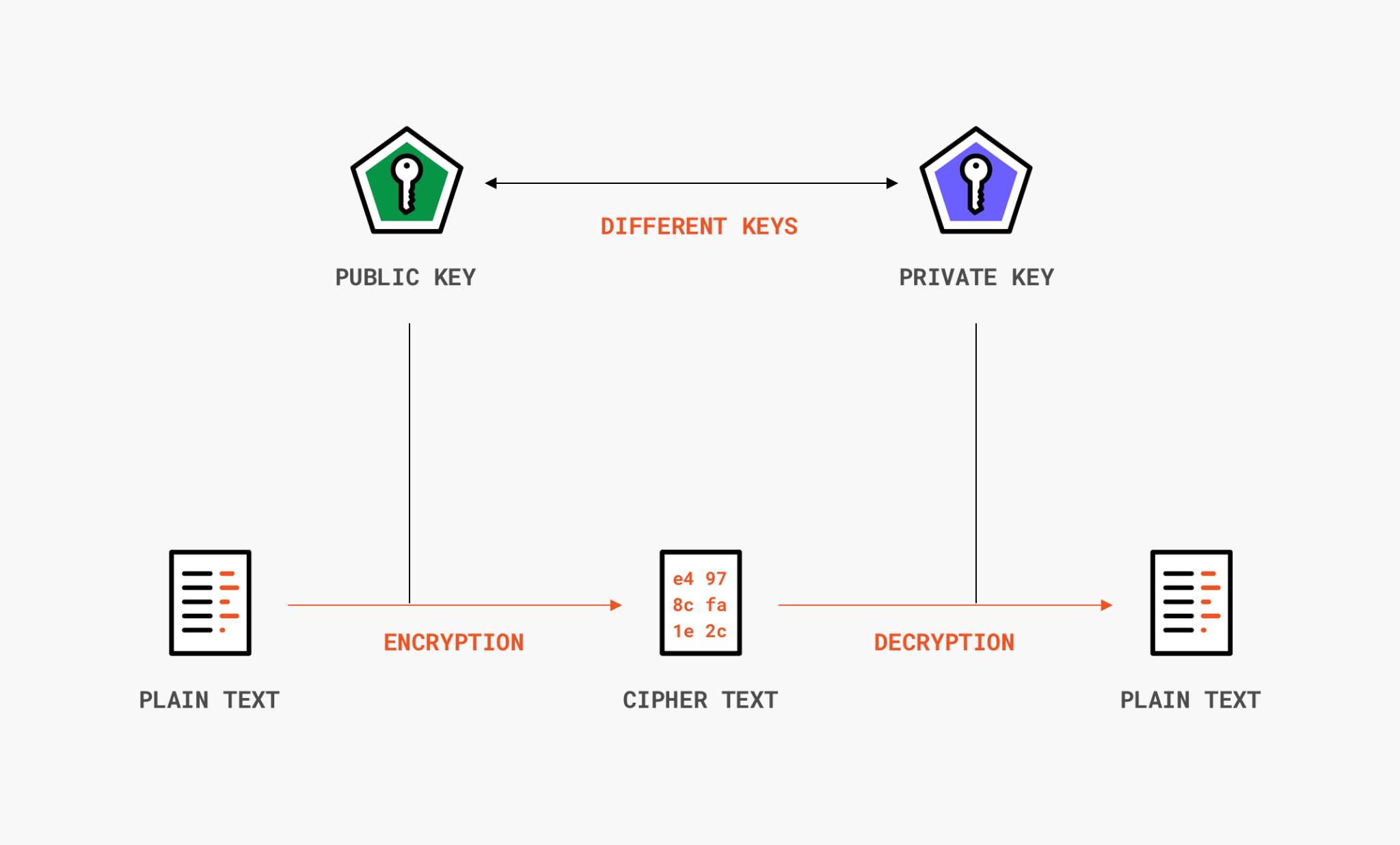
Asymmetric cipher encryption
(This is assuming the attacker went through the trouble of providing a way for the victim to get their data back. They could just encrypt everything with AES and delete the key with no intention of ever recovering the data.)
Other than that, the only “realistic” scenario to decrypt the data is by brute-forcing it. I use quotes because it’s not really realistic – we already went over the math behind it. You would need more time than the age of the universe to decrypt AES-128 even if you were using all the computational power available today.
How To Protect Against Ransomware
When it comes to ransomware, the best defense is being proactive instead of reactive. If you got hit by ransomware and didn’t already have a plan in place, your chances of ever recovering your files are slim.
With that in mind, the tips below will help you mitigate some of the risks before something bad happens.
1. Update Your Systems Regularly
In May 2017, a strain of ransomware known as WannaCry was deployed around the world, affecting more than 230,000 computers in 24 hours.

Screenshot of the WannaCry note
The malware exploited a vulnerability in SMB, a file-sharing protocol in Windows, that allowed the virus to spread itself through the network without being executed by the user.
To get infected, you didn’t need to run anything – being connected to the same network as someone else who ran it and having an unpatched version of Windows was enough.
Microsoft had released a security update a month before, in April, so only the organizations that weren’t as diligent with their software updates were affected by the attack.
Keeping your systems up-to-date is your first line of defense, and in most cases, can be automated. Low-effort, high-reward.
2. Think Hard Before Paying The Ransom
If you’re hit by ransomware and your data is now encrypted, you might be tempted to throw the flag and pay the ransom. After all, in the short term, paying the ransom might seem like the less expensive option. But you should think hard before paying.
There’s a reason why the official US government response is to “never negotiate with terrorists.” Caving in opens a can of worms and doesn’t guarantee that your problem will be solved.
First of all, paying the ransom doesn’t guarantee that the attackers will decrypt your data – they could just ask for more money instead. Furthermore, it signals that it’s profitable to target your company, and they (and others) will target your organization again in the future. A report by Cybereason found that 80% of the companies that pay the ransom are attacked again soon.
You should also be aware that, to pressure you into paying the ransom, criminals may perform a double extortion attack, where they first exfiltrate proprietary company information before encrypting the files and then threaten to release those secrets if the ransom isn’t paid.
3. Make a Plan For “Foul-Weather” in Advance
Regardless of the decision, it’s best if it’s made in advance. The stakeholders can keep a cool head and aren’t in a bind to come up with a solution on the fly.
Ever noticed that laminated paper that every NFL coach holds during the games? They contain the plays they have planned for different game situations. It was pioneered by Bill Walsh during the 80s:
Having a well-thought-out plan ready to go in advance of a change in the weather is the key to success. In the closing moments [of a playoff game against the Raiders], we recovered a fumble. We were trailing by three points, and a field goal would send us into overtime. My job [as an assistant coach] was to figure out how to get us within range of a field goal quickly. Unfortunately, the severe pressure and absolute pandemonium up at the booth where I was sitting destroyed my thinking. I completely forgot the plays we had practiced that would have worked best under those circumstances, but equally important, I recognized (in retrospect) that I had no specific plan for what to do in that “foul-weather” circumstance.”
He started scripting his entire opening drive after that game and then every “foul weather” situation he could think of before the game even started. Consider doing the same for ransomware – the procedures for what to do during an attack should be prepared in advance when you are not under duress.
Your plan should be as detailed as you can get away with. Here are some things you could write explicit instructions for:
- What to do during an attack (step-by-step)
- How to contact the person in charge during an attack
- How communication will happen during the attack
- Where the backup is stored and how to retrieve it
- How to wipe the disks clean and how to restore backup images
- List the partners or clients that would have to be notified and in which order, should such an attack happen
- Answer to difficult questions: Do you need to contact insurance? Which equipment would you need to rent or buy immediately to keep the operation running?
4. Be Aware of Phishing Emails
Phishing is the main attack vector used in ransomware cyberattacks. The attacker will send an initial malware disguised as a seemingly harmless file – for example, an Excel or Word document.
This malware, known as a dropper, is responsible for downloading the main malware that will encrypt the files and possibly other malware to exfiltrate other valuable data it finds on the organization’s network: intellectual property, passwords, trade secrets, etc.
Phishing is a hard problem to solve; it works because people are focused on work and aren’t expecting to be tricked. However, here are some things that you can consider doing to reduce the attack surface of phishing attacks:
- Implement email filtering. Block emails with dangerous extensions, such as .exe and .bat attached. It may stop some, but as mentioned before, sophisticated attacks will try to disguise the files.
- Create a process for phishing response. Here’s what we do at Auth0 when someone receives a phishing email.
- Train employees at your organization. Spam filters are very smart today, but even Google’s spam filter lets around 0.1% of spam emails reach your inbox. Employees must understand the risks of phishing emails.
These measures won’t stop you from getting compromised, but they will stop the low-effort attacks that can be automated.
5. Implement IAM (Identity and Access Management) and a Password Manager Where You Can
The second most common attack vector is trying to penetrate the network directly, either by brute force or by exploiting a vulnerability. Bloomberg reported in June that hackers were able to get into the network of the largest fuel pipeline in the US, Colonial Pipeline, and deploy a ransomware attack.
The bad actors got in through a company VPN by using employee credentials found in a data breach. The VPN also wasn’t protected by 2FA, which could have prevented the hackers from getting in.
Implementing IAM (Identity and Access Management) controls help organizations manage who has access to what and prove they are who they say they are (for example, via fingerprint scanning or hardware tokens).
On top of that, consider using a password manager. It’s likely that the employee used the same password elsewhere, and the bad actors simply used those same credentials to connect through the company’s VPN. A password manager ensures good password policies for all employees and makes sure that they don’t use duplicate passwords elsewhere.
6. Remove Local Administrative Rights From Endpoints
Most ransomware (and malware in general) perform many actions that require administrative rights during an attack. Removing such rights reduces the chance it will spread throughout the network.
Employees shouldn’t have access to local administrative accounts, and the IT staff should not have administrative rights for day-to-day activities.
Moreover, the local admin passwords should never be the same across workstations, as the attacker may pass the hash across machines with the same password to move laterally throughout the network.
7. Restrict Permissions To Run Software (And Macros)
Only a few applications are needed to run the business on a day-to-day basis. Determine the few applications that are needed, and block any other application from running using Microsoft’s Group Policy if you’re a Windows user (macOS and Linux users must look for third-party solutions).
This will prevent unauthorized processes, including those created by malware, from running.
8. Limit Network Access
As mentioned earlier, direct network exploits, such as remote services like RDP (Remote Desktop Protocol), are the second most common infection vector.
Review your ports and block anything that you don’t use. For example, port 3389 (RDP) and port 445 (SMB) are commonly exploited by hackers to infiltrate your network.
If you need them, limit them as much as possible. You probably don’t need your RDP port open to the Internet. Make it so that it’s only accessible via the organization’s VPN and secure it with 2FA.
Also, create firewall rules to automatically block incoming access after sufficient failed attempts and use a filter to block any outgoing connection from unauthorized applications. Most malware will need to connect to a remote server to carry on its attack.
Make sure that your network is properly segmented to avoid losing network drives to a single endpoint infection. Create a guest network with extremely limited access for untrusted devices. Implement read-only shares so that you can restore backups with limited attack surface; separate subnets according to purpose or application.
9. Create a Robust Backup Solution
No system in the world is impenetrable – even the most well-funded corporations in the world have been compromised. Instead of betting that you are the exception, assume the worst and create a plan to mitigate the damage when all else fails.
At roughly 3 cents per GB, it’s tough to beat hard drives when it comes to insurance against ransomware (but it doesn’t hurt to check if your insurance policy covers cyberattacks too).
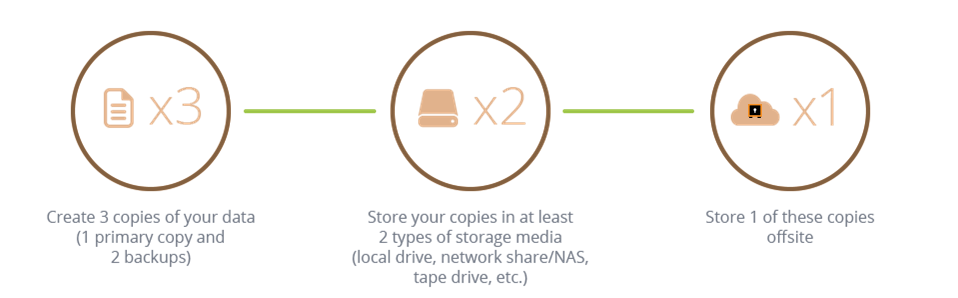
When designing your backup plan, keep in mind that:
- It must be automated. Any backup that depends on human intervention is prone to be neglected at some point.
- It must be rock-solid. Test your snapshots from time to time. You don’t want to think you have your files backed up, only to discover it hasn’t been copying the proper files this whole time.
- It must have at least one air-gapped copy. Air-gapped backups (disks not connected to another computer or network) make sure that, if the ransomware spreads through your systems, at least one copy is safe. Since they require manual intervention – someone has to plug the drive-in and disconnect it afterward – air-gapped copies generally aren’t as up-to-date as other hard drives in your backup plan. Still, it’s better to have a one-week-old copy than to have no copy at all.
- It must follow the 3-2-1 backup rule. You must have three copies of your data, in at least two different media types, with one of them in an offsite location.
How that plan is going to be implemented will depend on company policy (or personal preference). Having a backup in an offsite location could be as easy as using a third-party cloud provider, but it could be against company policy to have proprietary data uploaded to someone else’s cloud. So, it will vary.
In the majority of cases, though, it makes sense to have central storage connected to the network performing automated backups, even if it is at risk of being affected by ransomware. It’s much easier to mirror the data to an offsite location or to air-gapped hard disks from one location than every computer on the network.
Staying Safe
Do the tips above guarantee you won’t be hit by ransomware? No, but no one can make such a promise when it comes to security. Staying safe is a process you must continually engage in, and the pointers above are a good starting point.
Ransomware attacks are still one of the most profitable attacks for bad actors, which means it’s one of the most costly for you. You can’t stop attacks from happening, as it’s completely outside of your control. What you can do, however, is to make it as costly as possible to attack your organization. And as the saying goes, you don’t have to outrun the bear, only the person running next to you.
About the author

Arthur Bellore
Cybersec Writer