Configure GitHub Enterprise Server as SAML Service Provider
You can configure Auth0 as the identity provider using the SAML2 Web App addon for GitHub Enterprise Server (i.e. your private GitHub appliance). If you are looking for instructions to set up Auth0 as the identity provider for GitHub Enterprise Cloud (github.com), read Configure Auth0 as Identity Provider for GitHub Enterprise Cloud instead.
Configure SAML SSO on Auth0
Go to Dashboard > Applications > Applications and create a new application. Give it a meaningful name like GitHub. You can choose any application type, but the Regular Web App type is recommended.
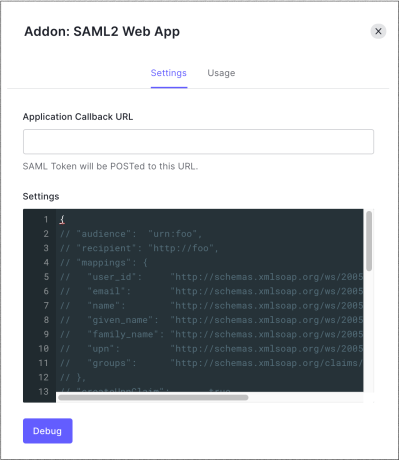
Go to the Addons tab and enable the SAML2 Web App toggle.
On the Settings tab, set the Application Callback URL to :
https://github.com/orgs/{yourGitHubOrgName}/saml/consume.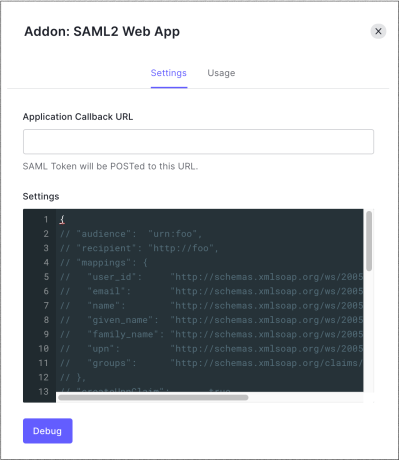
Paste the following code into the Settings text box and click Debug.
Replace{ "audience": "{yourGitHubServerUrl}", "mappings": { "user_id": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier", "email": "emails", "name": "full_name" }, "passthroughClaimsWithNoMapping": false, "mapIdentities": false, "signatureAlgorithm": "rsa-sha256", "digestAlgorithm": "sha256", "nameIdentifierProbes": [ "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier" ] }Was this helpful?
/{yourGitHubOrgName}with the GitHub organization name that corresponds to your GitHub subscription. For examplehttps://github.yourname.com.The above mapping will send the
user_idas the Name Identifier to GitHub. Use this option if you enable more than one connection for the GitHub application, as it will ensure uniqueness (every user will have a different ID).If you are using a single connection, you might prefer to use the
nicknameor another unique identifier as a friendlier Name Identifier, but make sure that the property you choose is unique.
Scroll to the bottom of the tab and click Enable.
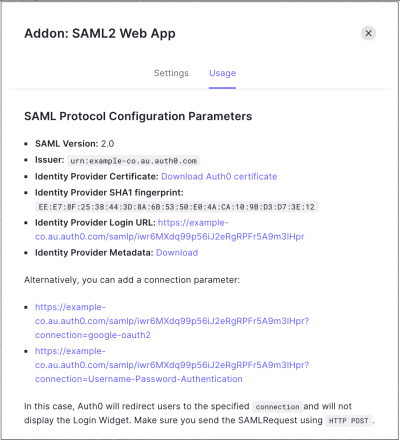
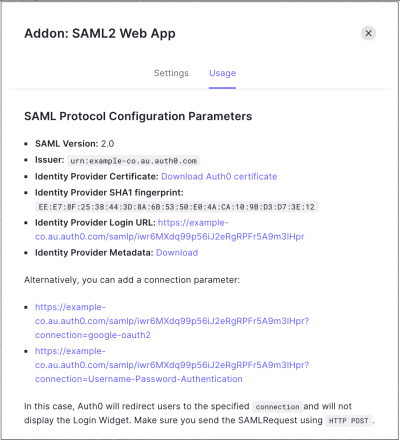
On the Usage tab, locate Identity Provider Metadata, and click Download to download the metadata file. You'll need this when you configure Auth0 as the identity provider.
Configure SAML SSO on GitHub
Follow the instructions in Using SAML on Enterprise Server- GitHub Help to complete the configuration on GitHub Enterprise Cloud. You will need the following information:
| Field | Entry |
|---|---|
| Sign On URL | https://{yourDomain}/samlp/{CLIENT_ID} {CLIENT_ID} will be the client_id for the GitHub application you just created in Auth0. |
| Issuer | urn:auth0:{yourTenant} |
| Verification Certificate | Download it from https://{yourDomain}/pem. Open the downloaded file with a text editor, copy the contents and paste it in the text area on GitHub. |
| User Attributes | Leave the defaults here, as the mapping that we configured in the SAML Web App addon uses the default attribute names proposed by GitHub. |
| Signature method | RSA256-SHA256 |
| Digest method | SHA256 |