Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
If you have Token Vault enabled for your connection, access and refresh tokens will no longer be stored in the user’s
identities array. Instead, they will be stored in a secure tokenset within the Token Vault. To enable Token Vault, read Configure Token Vault.This article assumes that you have already configured the connection with the IdP of your choice. If not, go to Identity Providers Supported by Auth0, select the IdP you want, and follow the configuration steps.
- If your code runs in the backend, then we can assume that your server is trusted to safely store secrets (as you will see, we use a secret in the backend scenario). If that’s the case, proceed to the backend section of this article.
- If your code runs in the frontend (for example, it’s a SPA, native desktop, or mobile app), then your app cannot hold credentials securely and has to follow an alternate approach. In this case, proceed to the frontend section of this article.
From the backend
Once you authenticate a user, the IdP often includes an Access Token in the user profile it returns to Auth0. For security and compliance reasons, Auth0 does not send this token to your app as part of the user profile. To get it, you must access the Auth0 and retrieve the full user’s profile:- Get an Access Token that allows you to call the Auth0 Management API.
- Call the Auth0 Management API’s Get Users by ID endpoint using the Access Token obtained in step one. This endpoint returns the full user’s profile, which contains the IdP Access Token.
- Extract the IdP Access Token from the response and use it to call the IdP’s API.
Step 1: Get a Token
You will need an Access Token to call the Management API.Create a test application for the Management API
If this is the first time you are requesting a Management APIv2 Token, you will need to create and configure an application that can be used to call the Management API:- Navigate to Auth0 Dashboard > Applications > APIs, and select the Auth0 Management API.
- Select the API Explorer view, and click Create & Authorize a Test Application.
Can't see the button?
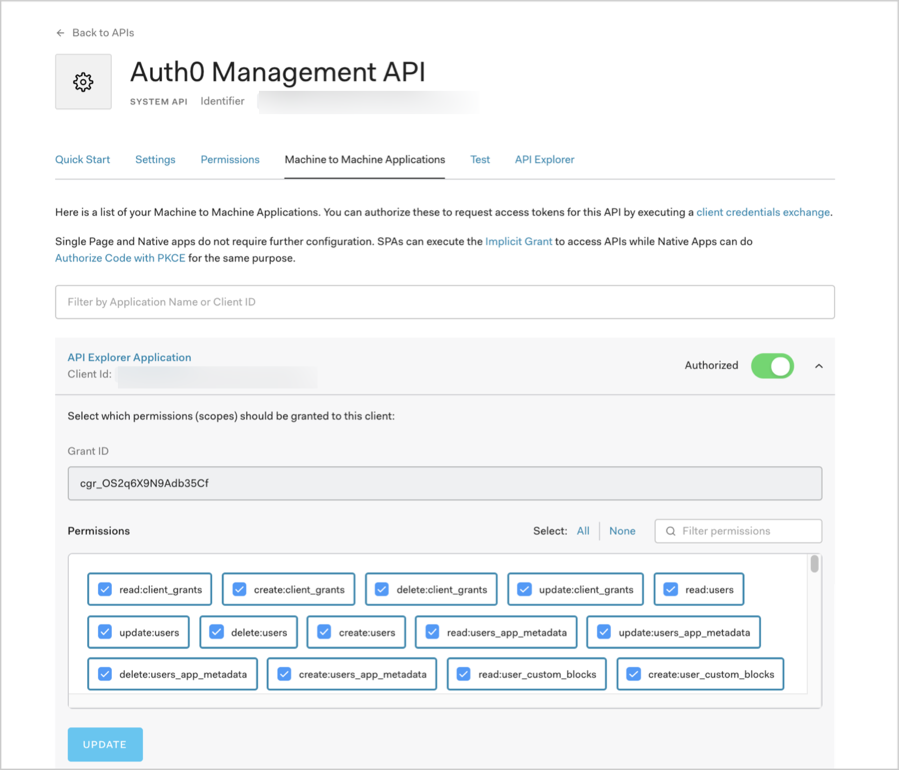
If you don’t see this button, it means that you already have at least one authorized application for the Management API. In this case, you can either update the scopes of the existing application and use that, or create a new one following these steps:
- Navigate to Auth0 Dashboard > Applications > Applications, and select Create Application.
- Select Machine to Machine Applications, and then Create.
- From the Select an API dropdown, select
Auth0 Management API. - Enable required scopes, and select Authorize.
- Select the APIs view, and enable the toggle for Auth0 Management API.
Get the Management API Token
You are now done with configuration and are ready to get your Management API token:- From the registered Auth0 Management API, select the Test view.
- Choose your application from the Application dropdown to pre-populate the ready-to-use snippets with customized variables.
- Choose your language of preference for the snippet, and copy and run it.
- Extract the
access_tokenproperty from the response. This is what you will use to access the Management API.
What are the snippets doing?
The snippets make a
POST operation to the /oauth/token endpoint of the Auth0 Authentication API, using the OAuth 2.0 Client Credentials grant. This is the grant that machine-to-machine processes use to access an API. To learn more about the flow, read Client Credentials Flow.Token expiration
By default, the token you received expires in 24 hours (86,400 seconds). To change this:- Navigate to Auth0 Dashboard > Applications > APIs, and select the Auth0 Management API.
- Select the Settings view, locate the Token Expiration (Seconds) field, enter a new value, and click Save. The maximum value you can set is 2,592,000 seconds (30 days), though we recommend that you keep the default value.
Step 2: Get the full User Profile
To get a user’s profile, call the Get a User endpoint of the Management API using the Access Token you extracted in the previous section: Replace these values:{userId}: ID of the user for whom you want to call the IdP’s API.{yourAccessToken}: Access Token you extracted in the previous section.
Where do I find the User ID?
- For testing purposes, you can find a user ID at Auth0 Dashboard > User Management > Users. Locate a user, and copy the value of the user_id field.
-
For your implementation, you can either extract the user ID from the
subclaim in the ID Token, or call the /userinfo endpoint of the Authentication API and extract it from theuser_idresponse property.
Step 3: Extract the IdP Access Token
You can find the Access Token used to call the IdP’s API within the user’sidentities array: user.identities[0].access_token.
For certain Identity Providers, Auth0 will also store a Refresh Token, which you can use to obtain a new Access Token for the IdP. This works for: BitBucket, Google (OAuth 2.0), OAuth 2.0, SharePoint, and Azure AD. To learn more, read Identity Provider Access Tokens.
google-oauth2.
To learn more about how to request specific scopes for an Identity Provider Access Token, read Add scopes/permissions to call Identity Provider’s APIs.
From the frontend
If you are working with a public application (SPA, native desktop, or mobile app), then this is the place to be. When working with a frontend app, the process for calling IdP APIs differs from the backend process because frontend apps are public applications that cannot hold credentials securely. Because SPA code can be viewed and altered, and native/mobile apps can be decompiled and inspected, they cannot be trusted to hold sensitive information like secret keys or passwords. Specifically, they cannot securely hold the for the Machine to Machine Application, which you use to call/oauth/token during the first step of the backend process.
Instead, you must build a proxy for your backend and expose it to your application as an API.
Build a proxy
First, you will build a process in your backend that will implement the steps included in the backend section of this article, and expose it to your application as an API. You will call the IdP’s API from the same backend process, so the Access Token is never exposed to your public application. Then, you will call your proxy API from your public application using the Authorization Code Flow with Proof Key for Code Exchange (PKCE).Show me how
If you haven’t implemented this before, you might find our Single-page Applications (SPA) with API architecture scenario useful. It covers a different scenario, but it explains how to configure Auth0, how to call an API from a SPA, and how to implement API validations. It comes with a sample that uses Angular 2 and Node.js.We also offer a Mobile Applications with API variation (the sample uses Android and Node.js).

