Create third-party applications that allow external developers, partners, or AI agents to access your APIs with enhanced security controls.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
Before creating a third-party application, make sure you have:- An Auth0 tenant with at least one API (resource server) configured
- At least one connection promoted to the domain level (for user-facing flows)
Create a third-party application
Create a third-party application using the Auth0 Dashboard or Management API.- Auth0 Dashboard
- Management API
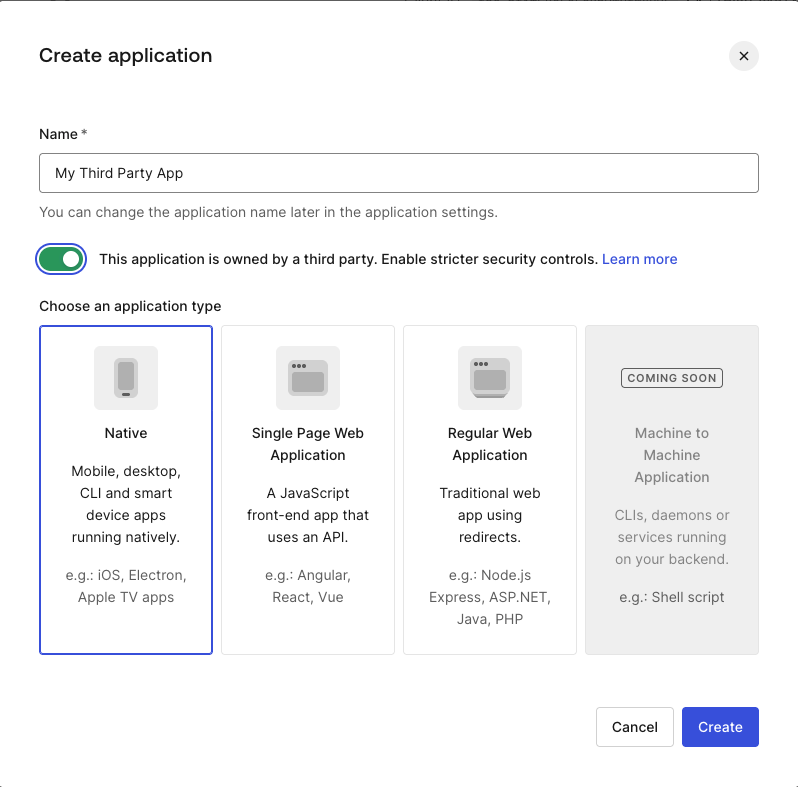
- Navigate to Applications > Applications.
- Select Create Application.
- Enter a name for the application and select the application type:
- Regular Web App for server-side confidential clients
- Single Page App for browser-based public clients
- Native for mobile or desktop public clients
- Check the This application is owned by a third party toggle.
- Select Create.
The
third_party_security_mode property is set at creation and cannot be changed. To use a different security mode, create a new application.Configure API access policies
Third-party applications require explicit client grants to access APIs. You can configure API access policies in the following ways:- Per-application permissions: Apply granular permissions to each application in your tenant.
- Default permissions for all third-party applications: Apply default permissions to all third-party applications in your tenant.
Per-application permissions
To grant a specific third-party application broader or narrower access than the defaults, create a client grant for that application’sclient_id:
- Auth0 Dashboard
- Management API
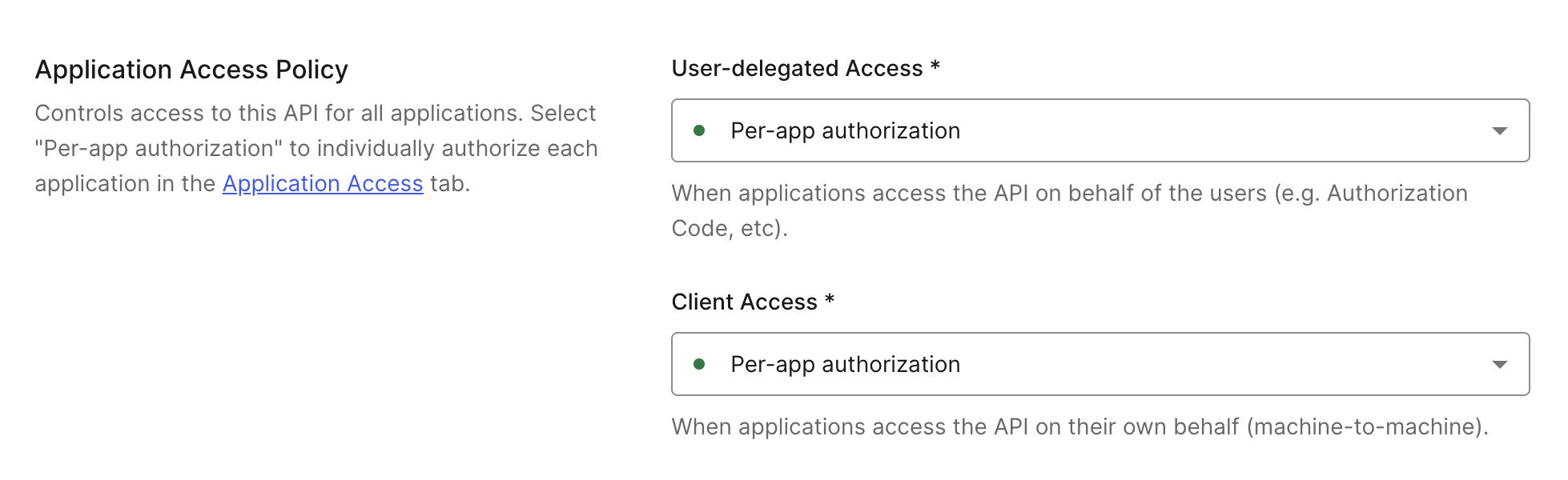
- Navigate to Applications > APIs and select the API.
- Go to the Settings tab.
- Scroll to Application Access Policy and set User-Delegated Access and Client Access to Per-app authorization.
- Select Save.
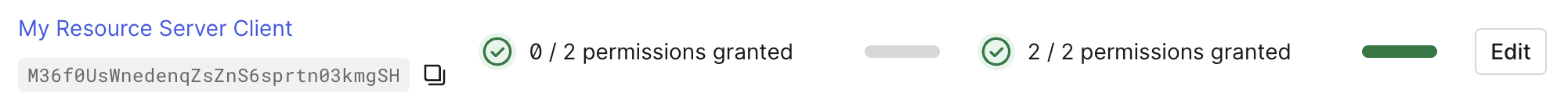
- Navigate to Applications > APIs and select the API.
- Go to the Application Access tab.
- Scroll to the application, select Edit, and then Grant Access for User-Delegated Access and/or Client Access. Then, select your desired permissions.
- Select Save.
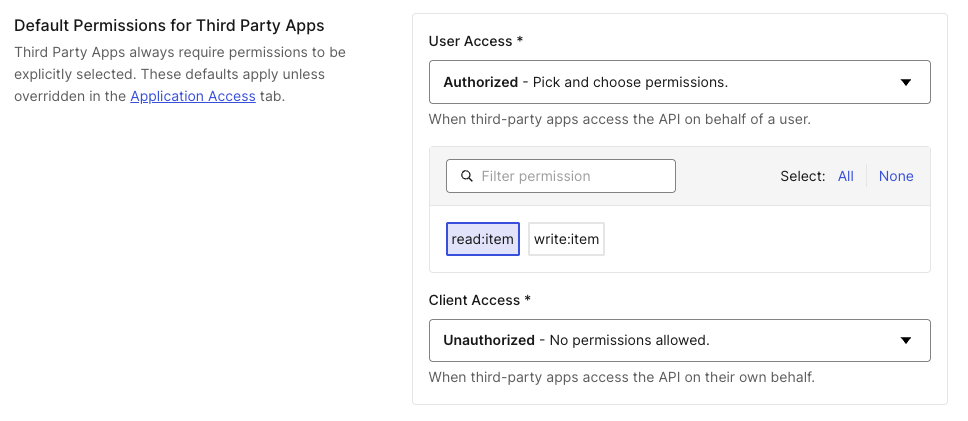
Default permissions for all third-party applications
Default permissions define a baseline set of APIs and scopes available to all third-party applications. This is required for Dynamic Client Registration, where you cannot configure access for each application individually.- Auth0 Dashboard
- Management API
- Navigate to Applications > APIs and select the API.
- Go to the Settings tab.
- Scroll to Default Permissions for Third Party Apps.
- Select Authorized for User-Delegated Access or Client Access.
- Select the scopes to grant, then select Save.
Configure connections
Third-party applications can only authenticate users through domain-level connections. Once a connection is promoted to the domain level, it becomes available to all third-party applications in the tenant. To promote a connection:- Navigate to Auth0 Dashboard > Authentication and select the connection type (Database, Social, Enterprise).
- Select the connection you want to use with third-party applications.
- Enable the Promote Connection to Domain Level toggle.
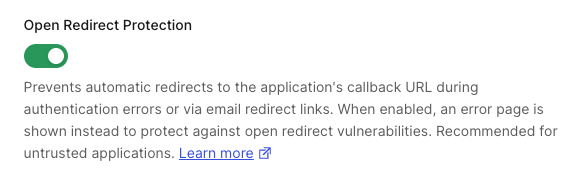
Configure open redirect protection
Third-party applications with enhanced security controls have Open Redirect Protection enabled by default. When enabled, Auth0 does not:- Redirect to the application’s callback URL on authentication errors
- Expose
application.callback_domainin email templates
- Auth0 Dashboard
- Management API
- Navigate to Applications > Applications and select the third-party application.
- Go to the Settings tab and scroll to Open Redirect Protection.
- Toggle the setting on or off.
- Select Save.