This week Microsoft announced the general availability of Windows Azure Active Directory (read ScottGu, Vittorio and Alex for the official word). We are very happy to see this milestone happening. We've been privileged to have been working with their team for quite some time now, and we think it is great news for the identity community. Congrats again on the release! This opens lots of opportunities for developers.
Why we think Windows Azure AD is important
Every app that creates a new user database contributes to Global Warming, and kills millions of kittens :-) -- the internet
This last release of Azure AD contributes greatly to the adoption of more modern identity architectures. Hundreds of thousands of companies rely on Active Directory today. Azure AD brings you closer to the (not anymore) utopia of connnecting organizations seamlessly and securely.
But what exactly is Azure AD? It is not a Domain Controller in the cloud. It is more like a combination of AD and ADFS with a more modern API to query the directory. It runs on the cloud and it can run as a the primary user directory for an organization or synced against an on-premise AD and federated with ADFS (it won't save passwords in the cloud). Even more enticing is the fact that it is free!
How does Auth0 work with Azure AD?
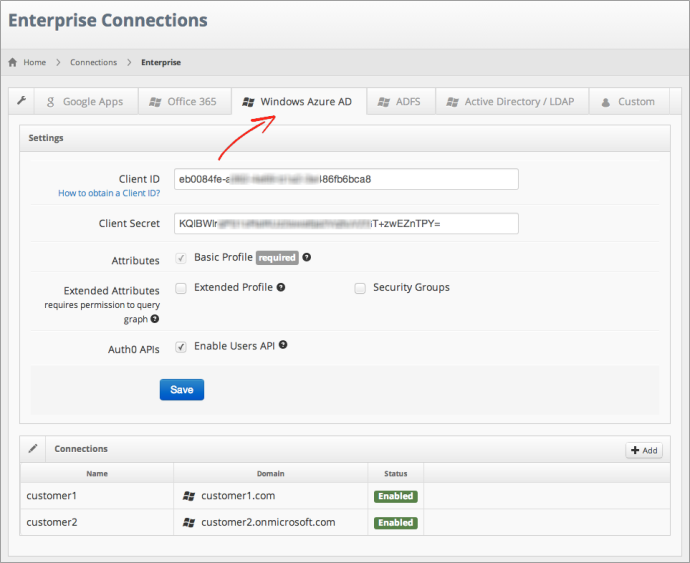
On our side, we've just completed the integration of Windows Azure AD in Auth0, and it is already enabled for our customers.
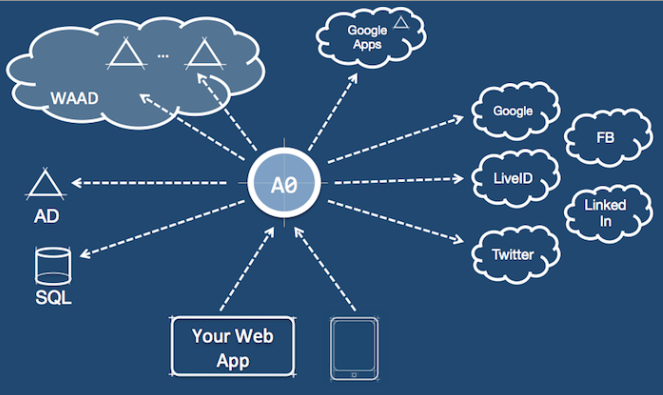
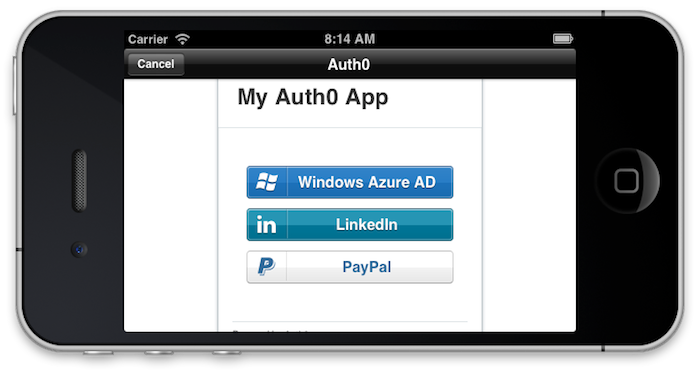
This means you can integrate your app with a single standard API and you will now enjoy easy access to Windows Azure AD and the rest of the identities we support: Google Apps, on-premises Active Directory with and without ADFS, user accounts stored in SQL databases, Facebook, GitHub, LinkedIn, Twitter, PayPal, etc.
In summary, with Auth0 you get:
1. Support for ANY kind of app
Using our SDK, it is straight forward to connect with users on Windows Azure AD and requires just a few lines of code. We support:
- Any .NET app: ASP.NET MVC3, 4, WebApi, ServiceStack
- Any device: iOS, Android, Windows Phone, Windows 8
- Any Platform: Java, Node.js, Ruby, PHP, etc.
Here is an example for iOS:
Auth0Client *client = [Auth0Client auth0:tenant clientId:clientId returnUrl:returnUrl connection:@"customer.onmicrosoft.com"];
[client showInViewController:self allowsClose:NO withCompletionHandler:^(BOOL authenticated)Auth0 uses a non-intrusive, standard, small footprint approach for identity integration that works with any identity provider. If you are working on a platform not listed above, take into account that anything that talks HTTP(s) can connect with Auth0.
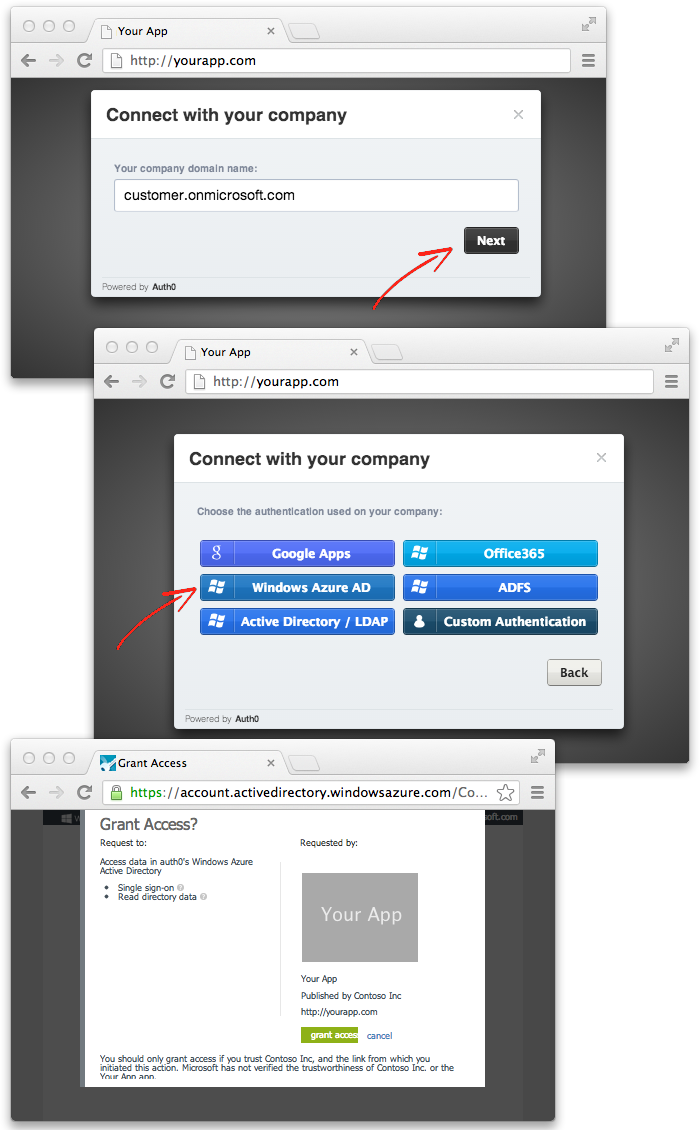
2. Sign up companies with the Provisioning Widget
If your app will accept users from multiple Azure AD domains, you will need to configure it for multitenancy (see the tutorial by Microsoft)
We have simplified this process with the Auth0 Provisioning Widget. With just a couple lines of JavaScript code your app can signup users from any organization, using any identity system: Azure AD, Google Apps, AD, etc.
This single line of code will display the Auth0 Provisioning Widget on your app:
window.Auth0.showProvisioning('/yourapp/callback')Here is how it would look (you would probably fire this from the control panel of your app)
This provides an easy way to add Single Sign On capability to your enterprise customers. You can also control the full user experience using the provisioning API instead of the widget.
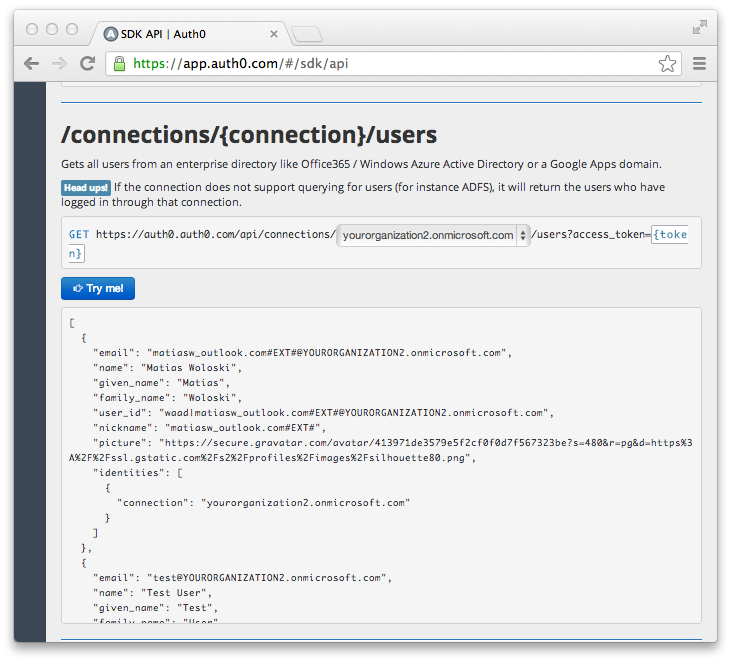
3. Query users from any provider
Once the organization/s have been provisioned through Auth0, you can query users of those organiztions through the Auth0 Users API. A very simple to use abstraction on a "Directory". Azure AD Graph API is of course different from Google Apps, or (on-premises) AD, or a Membership database. And social logins like LinkedIn, Google or Facebook; have no direct notion of a "Directory", but they do have equivalent concepts that bind people together (e.g. Friends, Contacts, Network).
This is Auth0 API explorer and we just did a GET on /connections/yourganization2.onmicrosoft.com/users. We keep the same API for every provider.
4. Native support for SharePoint, RMS, CRM, WAMS
Auth0 is already integrated with SharePoint, MSCRM, Rights Management and Azure Mobile Services.
Connecting these apps with Azure AD is fully automated and straight forward. It requires no customization, or specially complicated steps for configuration. Simple steps that get you up and running very quickly.
5. Mobile and native apps SDKs
If you are you building a mobile app on iOS or Android or Windows based devices, then again; authenticating users in Azure AD is readily available:
And if you enable the Azure Mobile Services add-on, we'll issue a token (JWT) compatible with it.
6. Sign up from the Azure Store
We are part of the Windows Azure Store. With a few clicks, you can have your own account, for free.
About the author

Matias Woloski
CTO and Co-founder