Using Multi-Factor Authentication (MFA) to secure your accounts is something you should always do. MFA adds a layer of security during login that requires users to provide more than one credential to prove their digital identity.
Why is it so important? Well, it's not so unlikely for attackers to steal usernames and passwords or programmatically attack user accounts. Having additional steps to prove your identity can nullify the effectiveness of these violations.
However, not all MFA options provide the same level of security assurance. So, let's review them and understand why some are stronger than others.
Factors, Authenticators, and Assurance
Okta's Businesses at Work Report 2023 shows that more organizations realize that not all multi-factor authentication (MFA) is created equal.
Low-assurance security questions are experiencing the slowest growth across the board, while high-assurance security keys and biometrics (including WebAuthn) are growing more quickly
— Todd McKinnon on the Businesses at Work Report post
But what does low-assurance or high-assurance mean?
To understand how strong or weak an MFA option is, we need to explore a few related concepts: authenticators, authentication factors, and authenticator assurance level.
Authenticators
An authenticator is something that can confirm the user identity. It can be a shared secret, such as a security question or a password, but it can also be a device or something the user needs to demonstrate to possess or control.
Based on the specific authenticator, there are methods to demonstrate the possession or control of the authenticator. For example, sending a code via SMS is a method used to prove a user possesses a device. Another method could be an authenticator app like Google Authenticator or a Security Key.
Authentication factors
In the authentication process, there are many options you can use to prove your digital identity. These are called authentication factors and there are three main types:
- Knowledge: Something you know, like a password or the answer to a security question.
- Users are familiar with authenticating with a password or answering a security question and are easy to use. Still, this information is usually easy to lose or guess, making it vulnerable to data breaches, social engineering, and phishing.
- Possession: Something you own, like a device or other physical tokens.
- The device stores or receives the user information, making it more secure than knowledge-based factors. Users are familiar with, for example, SMS authentication, where they receive an MFA code or one-time password (OTP) to their phone. At the same time, devices can be lost or stolen, making them vulnerable to person-in-the-middle and phishing attacks.
- Biometrics/Inherence: Something you are or is inherent to you, like a fingerprint.
- Biometrics are unique for each user; they don't have to remember or store their fingerprints or face. These factors are phishing-resistant and offer a seamless end-user experience but have yet to be widely adopted.
Every authenticator has one or more authentication factors.
Authenticator Assurance Level (AAL)
Assurance refers to the degree of confidence that an end user signing in to an application is the same end user who previously signed in to the application.
The Authenticator Assurance Level (AAL) is measured based on the use of one or more authenticators and the characteristics of their methods, as we will see in a moment.
What Makes an Authenticator Stronger than Another?
Now that you know the concept of assurance, factors, and authenticators, how can they help you understand when an authenticator is stronger? We said that the level of assurance is based on the authenticators and the characteristics of their methods. To measure this level of assurance, we need to answer the following question: "How confident am I that the user is who they say they are?"
Authenticators and assurance level
For example, a password provides some confidence in the user's identity. Only the user should know this password. But passwords can be stolen and used by other users. If I can get the user's fingerprint, I have more confidence in their identity: stealing their fingerprint is way more complicated than stealing their password. In other words, the user's fingerprint provides a higher level of assurance than a password.
There are intermediate levels of assurance between a password and a fingerprint. For example, proving that a user possesses a device provides a higher level of assurance than a password but lower than a fingerprint. While a password can be stolen and used by an attacker without the user realizing it, a device is less likely to be stolen, and if it happens, the user is usually aware of the theft in a short time.
The following diagram shows the different factor types and assurance levels for some of the most common authenticators:
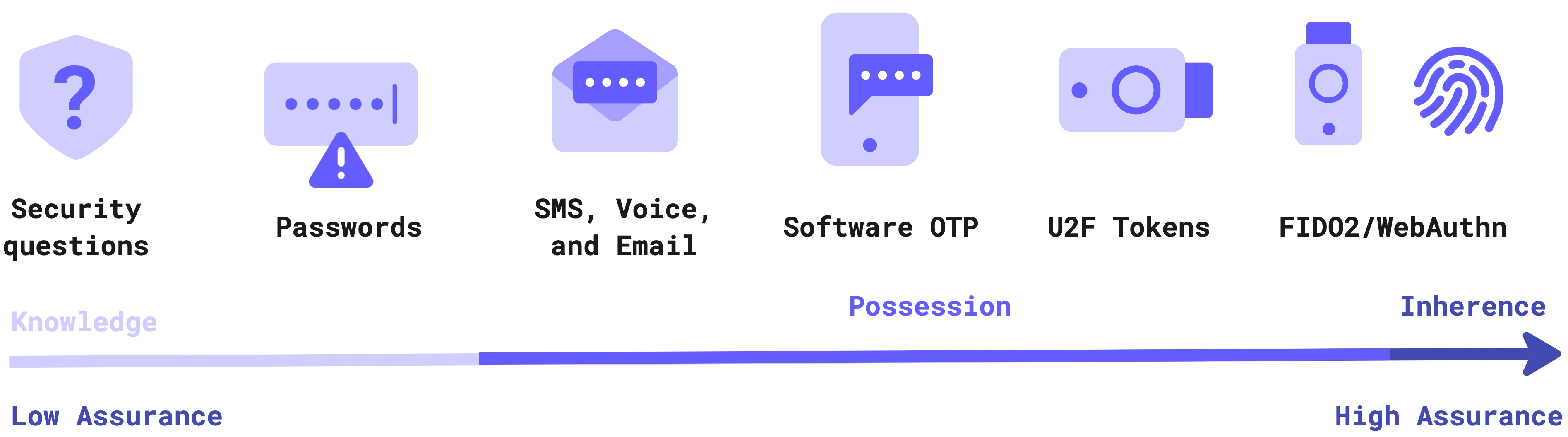
Depending on the authenticator method, you can be more or less confident about the user's identity. As you see in the diagram, security questions and passwords have low assurance because it is easier for the user to forget them and for attackers to guess when users use weak answers or passwords. On the other hand, FIDO2/WebAuthn credentials and biometrics have the highest assurance level because they rely on cryptographic algorithms and inherent characteristics that are hard to break.
MFA and assurance level
Authenticator assurance levels are not intended to measure the level of assurance of individual authenticators. They measure the level of assurance of the authenticated session. Therefore, if you use one authenticator to authenticate your user, the AAL of that authenticated session will match the AAL of the authenticator used. However, by combining authenticators, you can achieve a higher AAL for a session than you could with individual authenticators. That's where MFA comes in.
Also, using authenticators with different factor types is strongly recommended to make MFA effective. For example, by combining password and SMS authentication, you get an authenticated session with a higher assurance level than just the password. In this case, you combine a knowledge factor authenticator (the password) with a possession factor authenticator (the phone) through the SMS method.
If you use a combination of password and security key as your MFA, the assurance level of the authenticated session is stronger than the password and SMS combination. Indeed, the assurance level of the security key is higher than the SMS authentication.
Low-Assurance Authenticators
Following the NIST's Digital Identity Guidelines, low-assurance authenticators provide some confidence that the user controls an authenticator that confirms their identity. These authenticators permit single-factor authentication, provide baseline security at low cost, and most users are familiar with the authenticating process. Some of these authenticators are:
- Passwords
- Security Questions
- SMS, Voice, and Email One-Time Password (OTP)
- One-Time Password (OTP) Apps
In addition to single-factor authentication, this level of assurance allows multi-factor authentication based on the proof that the user possesses and controls an additional authenticator. However, no mandatory cryptography is required at this level, so you can find MFA options based on the combination of password and email or password and SMS, for example.
Most of the authenticators falling in this assurance level are low-cost, and users are familiar with them. However, their vulnerability ranges from being easy to guess or discover to being exposed to social engineering and phishing.
Mid-Assurance Authenticators
This level of assurance offers a higher level of confidence of the user's identity. It requires using two authentication factors, which are either a physical authenticator and a memorized secret or a physical authenticator and a biometric associated with it. Some of these authenticators are:
- Push Notifications
- Physical token One-Time Password (OTP)
MFA can be performed using either a multi-factor authenticator or through the use of two independent authenticators. Multi-factor authenticators use an additional factor, either something you know or have, to unlock a secret stored in the (physical) authenticator.
High-Assurance Authenticators
Authenticators with a high level of assurance introduce a new requirement beyond the mid-level assurance: using multiple authentication factors with a hardware-based authenticator. Some authenticators with a high level of assurance are:
- FIDO2/WebAuthn with security keys or biometrics
FIDO2 is an open authentication standard hosted by the FIDO Alliance that consists of the W3C Web Authentication specification (WebAuthn API), and the Client to Authentication Protocol (CTAP2).
WebAuthn is a W3C recommendation for defining an API enabling the creation and use of strong, attested, scoped, public key-based credentials by web applications for strongly authenticating users.
Using FIDO2/WebAuthn credentials guarantees users a phishing-resistant and seamless end-user experience. The use of higher-assurance security keys and biometrics ticked up to 24% in 2022, up from 21% a year ago, according to the 2023 Businesses at Work Report so even though it is not widely adopted yet, using high-assurance MFA is growing rapidly.

Sign up to try out Auth0 for free.
Get started →Conclusion
In this post, you learned about Multi-Factor Authentication and the different types of authenticators, assurance levels, and existing factors.
Depending on your authenticator method, you can be more or less confident about the user's identity. When you combine authenticators, you can achieve a higher level of assurance that the user is who they say they are than when you use individual authenticators. Therefore it's recommended that you use authenticators with different factor types.
If you want to learn more about MFA, factors, and authenticator assurance levels, you can download the Factor Types and Authenticator Assurance Levels datasheet or download the entire 2023 Businesses at Work Report.


