In today's interconnected digital landscape, ensuring robust security for online platforms has become a top priority. As the number of data breaches and cyber-attacks continue to rise, businesses and organizations must employ innovative solutions that go beyond traditional authentication methods. Two industry giants, Auth0 and ID.me, have joined forces to create a powerful alliance that offers advanced security measures by integrating Auth0's identity and access management expertise with ID.me's cutting-edge authentication and identity verification capabilities.

The Power Duo: Auth0 and ID.me
In the realm of consumer identity and access management, Auth0 has been a trailblazer with its versatile authentication solutions, catering to diverse needs across industries. By providing a seamless and secure way for users to log in to applications and services, Auth0 has revolutionized the way developers handle identity and access management. But what happens when consumer authentication is not enough, and the business needs a way to associate a user’s true identity to their request to access your application? That's where ID.me comes in.
How Does It Work?
ID.me exists to put individuals in charge of their own login, their own data, and their own ID cards to allow the login and the data to move with the user. ID.me’s primary focus lies in validating users' identities through a multi-layered approach, ensuring that the person on the other end of the screen is who they claim to be, and our user’s know they can take their portable identity with them anywhere they see the green ID.me button. This level of assurance goes far beyond the standard username-password-OTP combination, effectively thwarting potential fraudulent activities for higher-risk transactions.
Turnkey Integration of ID.me on Auth0
We wanted a way for developers and business decision makers to easily leverage the benefits of ID.me’s trusted and portable credentials within their existing Auth0 implementation in a turnkey manner - eliminating the need of custom development. Therefore, we worked closely with the Auth0 team to create three turnkey marketplace listings:
In just four configuration steps, you can benefit from ID.me’s network of 110M+ members and 47M+ IAL2 verified members for your secure authentication and identity verification needs.
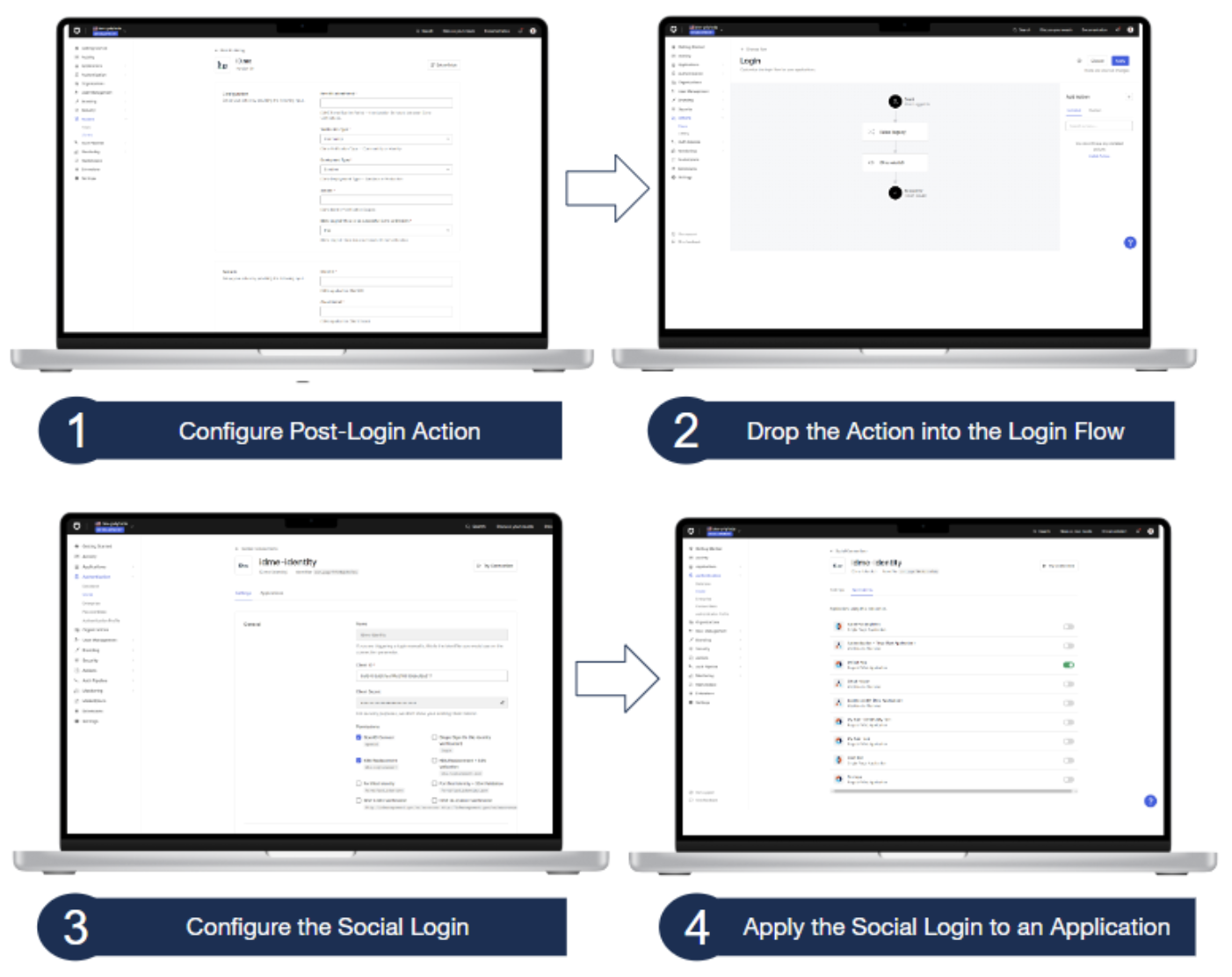
It’s as simple as selecting the Add Integration button on the marketplace listings, entering your ID.me credentials, and applying the post-login action and social login to your appropriate Auth0 applications. We’ll go into more detail in the next section, but as a sneak peak, your end result will look something like this:

- Pathway #1
- By providing users with the choice of how they prefer to log into your application, customer satisfaction increases, pass rates improve, and ID.me provides support for any of your users that elect to log in through ID.me - effectively reducing the burden and lowering the costs of password resets to your call center or IT Help Desk. After successful authentication or verification, a corresponding Auth0 user account will be created with appropriate ID.me-validated attributes mapped within the user account. support for any of your users that elect to login through ID.me - effectively reducing the burden and lowering the costs of password resets to your call center or IT Help Desk. After successful authentication or verification, a corresponding Auth0 user account will be created with appropriate ID.me validated attributes mapped within the user account.

- Pathway #2
- In order to support your existing user base, users can log into their existing account, and can be redirected to ID.me for verification. After successful verification, the individual’s ID.me attribute payload will automatically be mapped within the existing Auth0 user account.
For Developers - Let’s Dive a Little Deeper
While integrating ID.me is turnkey within your Auth0 tenant, it’s still important to understand the nuances of the user journey and data flow. The architecture diagram below provides an overview of the two pathways we just discussed: ID.me as a Social Login and ID.me as a Post-Login Action.
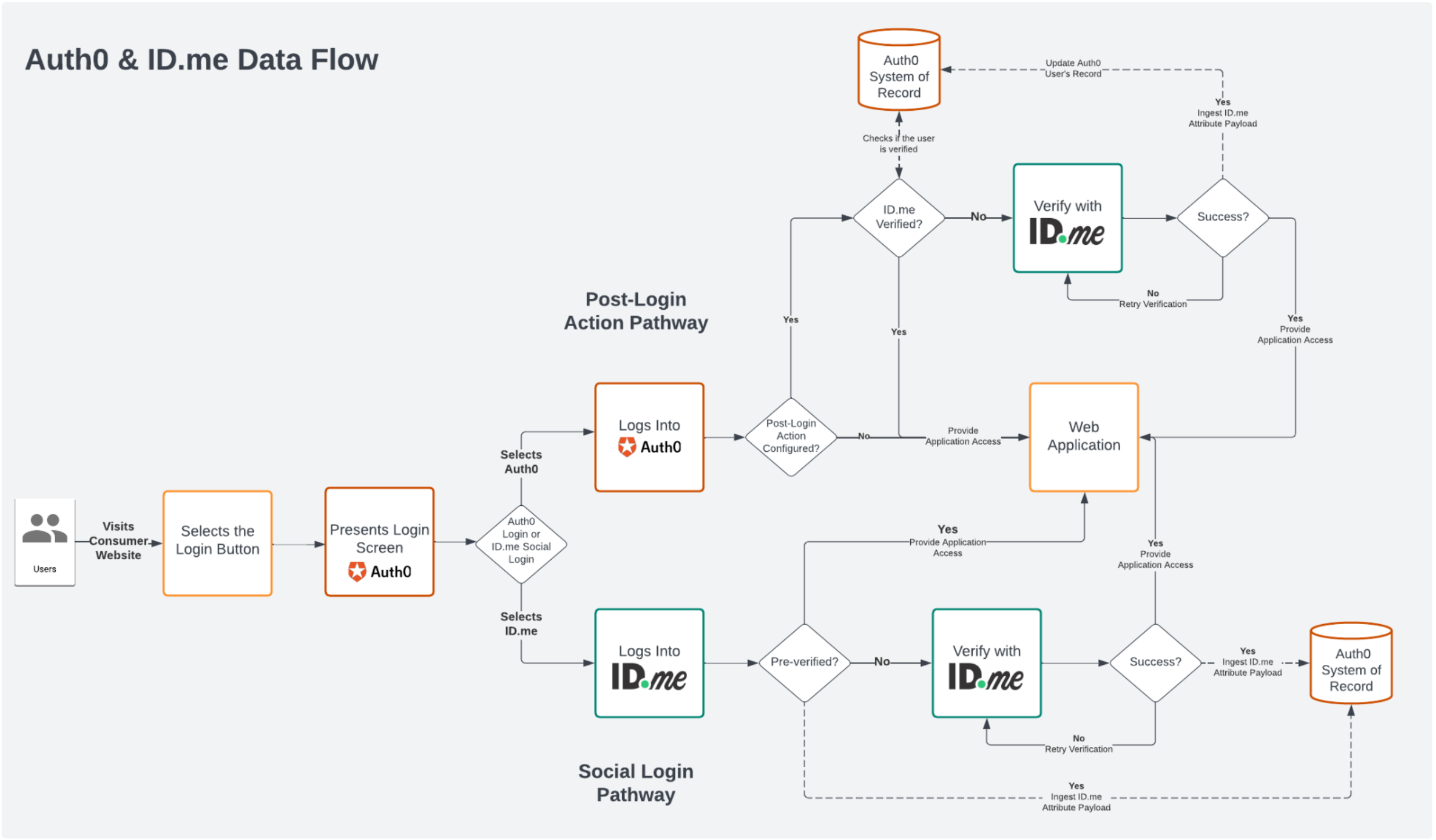
The top half of the architecture diagram highlights the Auth0 login with the ID.me post-login action pathway, in which the user elects to log into their existing Auth0 credentials, and will be redirected to ID.me for verification. Take note that an indicator is used to determine when to prompt an existing user for verification with ID.me, and that post-successful verification, that indicator will be updated within the user's application metadata.
The bottom half of the architecture diagram demonstrates the data flow for the Social Login pathway. This is where our partners receive the benefit of the ID.me network, allowing 110M users to login to your application with their pre-verified ID.me credentials in just a few clicks.
Now, let’s take a look at an even deeper dive and look at an overview of ID.me, as well as what the exact steps needed to configure the ID.me integrations in this video.
Conclusion
The digital landscape is continually evolving, demanding innovative solutions to combat cybersecurity threats effectively. The partnership between Auth0 and ID.me brings together two industry leaders, each contributing its strengths to create a security ecosystem that surpasses traditional authentication methods. By combining Auth0's identity and access management prowess with ID.me's authentication and identity verification capabilities, we can ensure a higher level of trust, security, and compliance while providing a seamless user experience. Together, we are transforming the way to approach digital security, setting a new standard for safeguarding user identities in an ever-changing world.
About the author

Ryan Friess
Sr. Sales Engineer - ID.me
