OAuth allows applications to access APIs on the user’s behalf. Before an application can act on a user’s behalf, the user must explicitly approve the requested permissions. This approval step is called user consent. For third-party applications, user consent is always required. The user must approve every authorization request. For first-party applications, consent can be skipped when configured, because you control the application and trust it to act appropriately.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
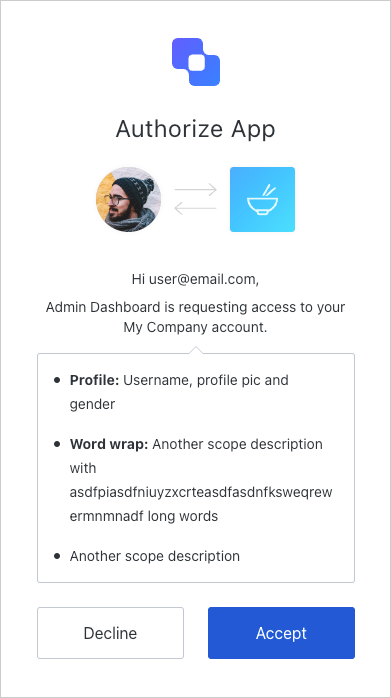
Consent dialog
When a third-party application redirects a user to the/authorize endpoint and requests access to an API, Auth0 displays a consent dialog listing the permissions the application is requesting.
The following authorization request displays a consent dialog asking the user to approve the read:posts and write:posts permissions for the API:
Third-party applications with enhanced security controls do not support OIDC scopes (
openid, profile, email) in this release. The consent dialog shows API scopes only. OIDC support for third-party applications is planned for a future release.Scope descriptions
By default, the consent page uses scope names to prompt for the user’s consent. As shown below, define scopes using theaction:resource_name format for clear display:
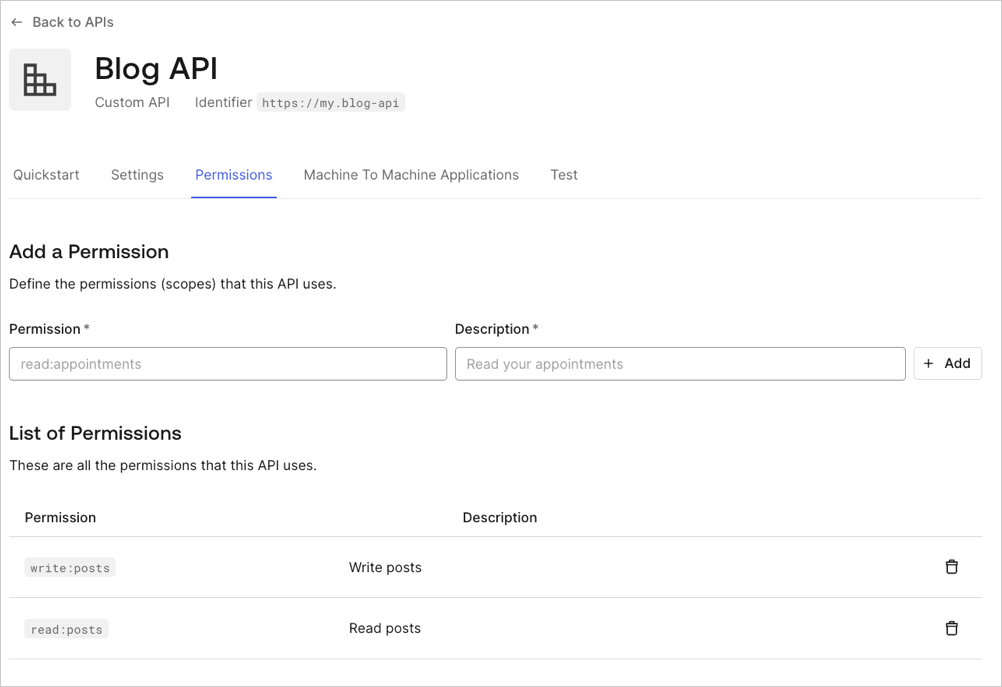
use_scope_descriptions_for_consent flag to true:
This setting affects consent prompts for all APIs on the tenant.
Handle rejected permissions
When a user declines consent, the behavior depends on the application’s redirection policy:open_redirect_protection(default for third-party apps): Auth0 displays an error page instead of redirecting. This prevents open redirect attacks.allow_always: Auth0 redirects to theredirect_uriwith anaccess_deniederror:
Skip consent for first-party applications
First-party applications can skip the consent dialog when the API has the Allow Skipping User Consent option enabled. To navigate to the Allow Skipping User Consent toggle, select Applications > APIs > (select the API) > Settings > Access Settings. Third-party applications always require consent and cannot skip the consent dialog.Even when consent is skipped for first-party applications, a login confirmation prompt may still appear when the application uses a non-verifiable callback URI (such as
localhost or a custom URI scheme). This protects users against application impersonation on the same device. To learn more, read Measures Against Application Impersonation.Revoke consent
To revoke a user’s consent for a specific application:- Navigate to Auth0 Dashboard > User Management > Users.
- Select the user.
- Select the Authorized Applications tab.
- Select Revoke next to the application.
Password-based flows
When using the Resource Owner Password Flow, no consent dialog is involved because the user directly provides their password to the application, which is equivalent to granting the application full access to the user’s account.Force consent
To force users to provide consent on every login (even if they have an existing grant), includeprompt=consent in the /authorize request:

