Better, Easier Identity Management for Real Estate Companies
Deliver a pain-free login process and meet compliance mandates quickly and easily.

Modern Identity Management & Real Estate
At the Real Estate Standards Organization’s (RESO) annual conference in Nashville this October, identity authentication was the topic of focus. The real estate sector is quickly adopting to modern identity practices to lower risk, provide a better user experience and modernize their platforms. Specifically, any listing services affiliated with National Association of REALTORS® require adoption of the RESO Web API. The RESO Web API specifies that authentication is performed with OpenID Connect.
OpenID Connect is an authentication layer that sits on top of the widely used OAuth 2.0 authorization standard. OpenID Connect extends the same kind of security that large enterprises have been using for years as an open standard that any organization can adopt.
How to implement OpenID Connect

You have two options for adopting OpenID Connect: internal development or using vendor solution. If you have internal developers, OpenID Connect can be integrated by developers, however, Auth0 supports OpenID Connect out-of-the-box, making adoption faster and easier. There’s no need to spend a month writing your own provider and getting it compliant.
Auth0 is as close to plug-and-play as it gets. You can implement an OpenID Connect solution in four simple steps by copying a few lines of code. You do not even need to learn the protocol to use Auth0.
- Set up a callback URL from your Auth0 dashboard
- Integrate Auth0 Lock on your site or trigger login manually
- Send the
codeyour app receives to the Auth0 with aPOST - Use a
GETto retrieve the user profile from the server’s response
Then, when users visit your website, this is what they’ll see (you can customize the look of the box, of course!)
National Association of REALTORS®

To make adoption easy, the National Association of REALTORS® turned to Auth0 to meet this standard.
“When we were looking to implement OpenID Connect, we first considered building a solution ourselves. Ultimately we chose to work with Auth0 because it enabled us to unify authentication across dozens of disparate web properties while dramatically improving our time to market.”
-Mark Lesswing – SVP and CTO, National Association of REALTORS®
Video: OpenID Connect in less than 6 minutes
Advantages Beyond OpenID Connect
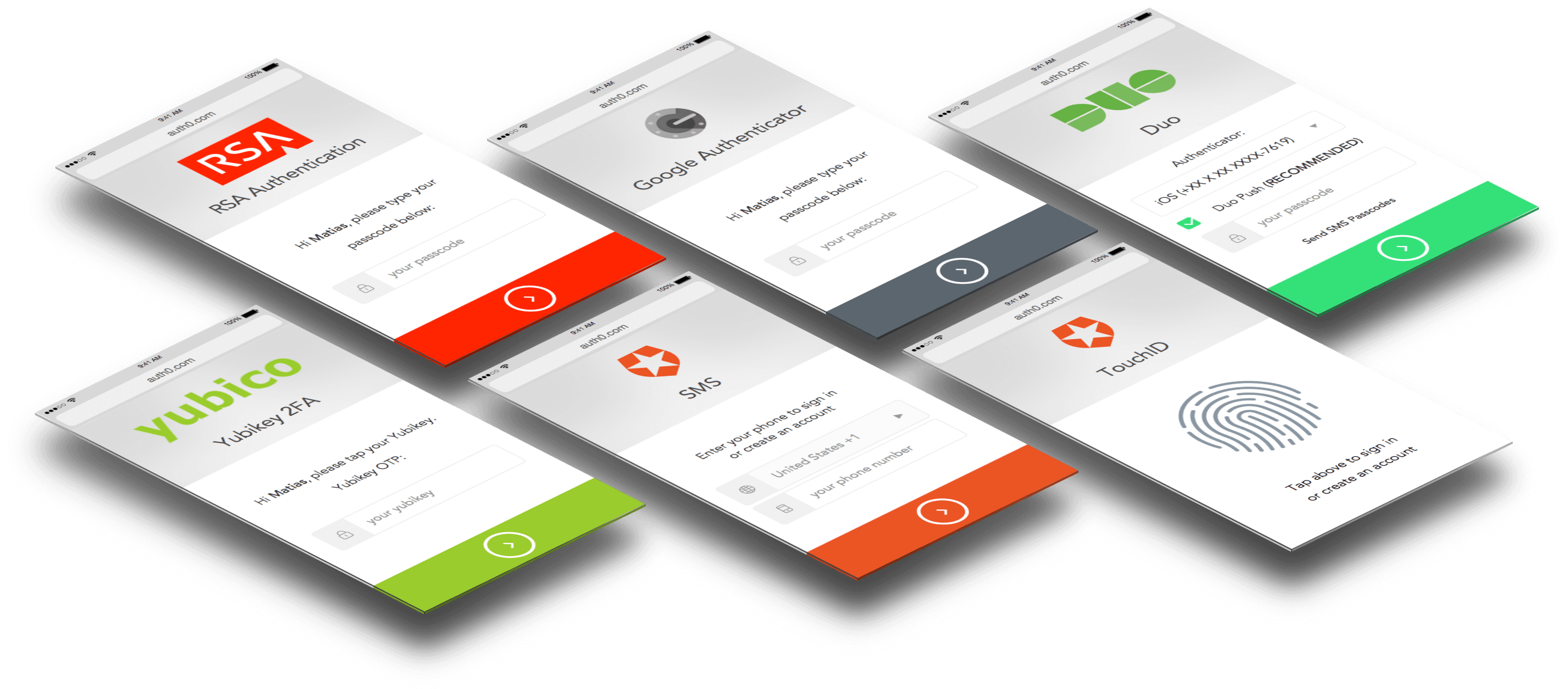
Once OpenID Connect is implemented, you can also take advantage of other Auth0 benefits including:
- Enriched user profiles with important identity provider data
- Choose your preferred identity providers (30+: Google, LinkedIn, etc.)
- Multi-Factor Authentication
- Breached Password Detection
Auth0 is a universal identity clearinghouse. Any application – mobile, web, enterprise – written with any framework. And any Identity Provider (IdP) from popular social sites to enterprise IdPs like Active Directory, SAML, and legacy databases. With just a few lines of code, you can the implement secure, comprehensive identity management system to meet your needs.
Sign up for free
Start building today and secure your apps with the Auth0 identity platform today.
