Last week, the OpenID Foundation posted an open letter to Apple, encouraging them to bring the recently announced Sign In with Apple login feature in line with the OpenID Connect (OIDC) protocol. As we pointed out when it was first announced, Sign In with Apple aligns with some of the requirements laid out in the OIDC and OAuth 2.0 specifications, but Apple makes little mention of these standards in their official documentation.
Learn about the de facto standard for handling authentication in the modern world.
Download the free ebook
The letter from the OpenID Foundation was accompanied by a document outlining where Sign In with Apple differs from the OIDC specification. This document, drafted by the OpenID Foundation’s Certification team and other members of the identity community (including Filip Skokan, an engineer at Auth0), calls out the OIDC spec violations that increase the risk of attacks and privacy concerns, as well as additional peculiarities that will make it difficult for developers to incorporate Sign In with Apple into their existing applications.
What This Means For Application Developers
While Sign In with Apple is still very much under development and a number of significant changes can be expected, a lot of attention is being paid to the implementation specifics even at this early stage. This is largely due to the fact that Apple will require the Sign In with Apple option for all applications in their ecosystem that support third-party logins. A new identity provider that complies with established standards could greatly reduce the burden on application developers, as many applications are already set up to handle similar connections that do follow the standards.
Of course, Apple may choose not to align with the OIDC specification for any number of reasons related to their goals and requirements as a hardware and software provider. Identity and access management is not a core product for Apple, and establishing interoperability with systems outside of their ecosystem may very well not be a high priority. As with any identity solution tightly coupled with a company’s other software, features that benefit general use may only be put into place when they overlap with the specific requirements of operating within that company’s primary offerings. But interoperability is not the only concern addressed in the OpenID Foundation’s letter — it remains to be seen how Apple will address the attack surface exposed by not complying with parts of the specifications that deal with preventing known attacks.
Managing Discrepancies with an Independent Identity Platform
Independent identity platforms, focused solely on identity and access management, do not run into these same issues with competing priorities. It is in their best interest, and the interests of their users, to connect as easily and widely with other systems as possible. At Auth0, we provide simple configuration options to set up a variety of social and enterprise connections that follow the standards established by OIDC and OAuth 2.0, SAML, WS-Federation, and many others. For those connections that don’t entirely comply with specifications, we work to bridge the gaps by implementing the best options the providers offer and adding measures where we can to harden against attacks. And while we continue to be active in the identity community to encourage the adoption of recognized standards, the Auth0 platform is built to address and keep up with any differences, so that application developers can be free from worrying about changes that might affect their code.
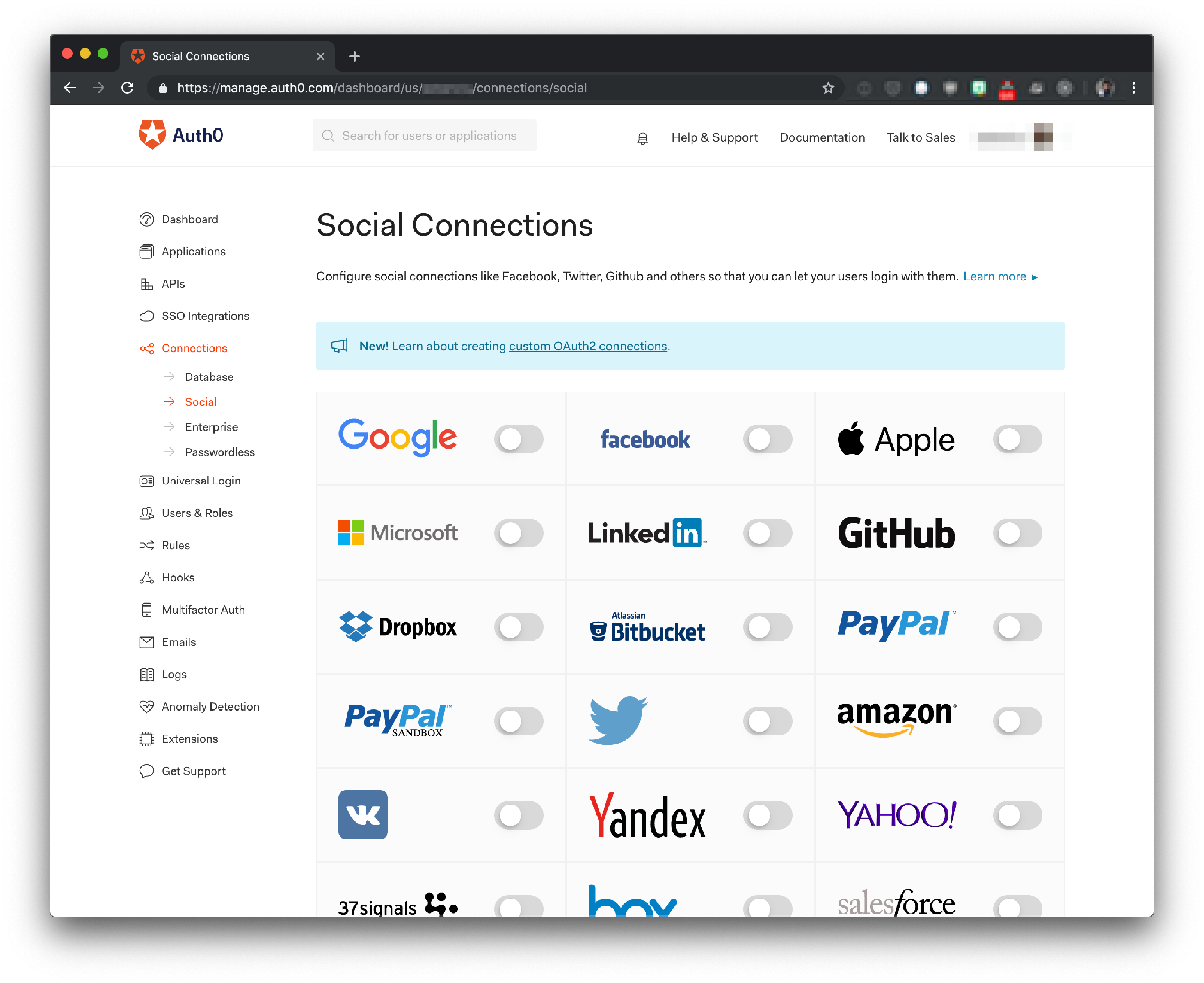
Because Auth0 is a certified OpenID provider, you know what to expect when connecting with our platform. Any application already supporting an OIDC-compliant provider is already set up to quickly integrate with Auth0 and connect to a vast array of identity providers by simply turning on a few switches. And with our collection of SDKs across multiple languages, it’s easy to secure any application with Auth0 without having to worry about implementation details.
Aside: Try Sign In with Apple on Auth0 Today
Auth0's beta support of Sign In with Apple makes it easy to get started:
- Sign up for an Auth0 account.
- Use the QuickStart of your choice to integrate Auth0 into your application, or start from scratch and have a secure app deployed in minutes.
- Add Sign In with Apple under “Connections” > “Social”, and test with Auth0's developer credentials.