The thought of a hacker remotely seizing control of your vehicle sounds like something from a science fiction movie. But car hacking is not only possible today; it has been since 2005, according to a computer science researcher from New York University. And many auto manufacturers may not be adequately addressing the growing threat of automotive cyberattacks.
In 2019 alone, automotive-related cyber incidents doubled from the year prior (a 605% increase from 2016). These include carjackings, data breaches, and even taking control of moving vehicles. But as Justin Cappos (the computer science researcher at New York University) told The Times, the potential threats are even worse than anything we’ve seen yet:
“If there was a war or escalation with a country with strong cyber-capability, I would be very afraid of hacking of vehicles,” Cappos says. “Once in, hackers can send messages to the brakes and shut off the power steering and lock people in the car and do other things that you wouldn’t want to happen.”
Considering the rate at which manufacturers are adding connectivity to their vehicles, this is concerning. Even more so considering that last year’s 2019 Synopsys and SAE study found 84% of manufacturers worry their current cybersecurity programs aren’t keeping up with the technology they support.
Simply put, manufacturers must take steps to improve automotive cybersecurity moving forward. Here are the most common ways that car hacks happen, as well as how manufacturers can better protect their vehicles from them.
What Is Car Hacking?
Car hacking refers to all of the ways hackers can exploit weaknesses in an automobile’s software, hardware, and communication systems in order to gain unauthorized access.
Modern cars contain a number of onboard computerized equipment, including an electronic control unit (ECU), a controller area network (CAN), Bluetooth connections, key fob entry, and more. Many also connect to central servers through the internet. And each of these different computerized technologies can be attacked in a variety of ways.
The Most Common Types of Vehicle Hacking
Today’s vehicles are more reliant on computers than ever before (Forescout estimates that software in modern cars contains 15 times more code than what is in most airplanes). And as such, hackers have a number of points of access to break into a car’s systems.
So what kinds of cars can be hacked? And how?
The type of car hack depends on the kind of car. But Upstream has cataloged every major car hacking incident in the world for the last decade and found several trends. Here is where its research indicates car companies should look to bolster their cybersecurity efforts.
1. Key Fob Hacks
The most common way hackers gain access to cars today is through the computerized key fob — often in order to steal the vehicle (or what is inside of it). This is typically done by spoofing or cloning the signal that a car and key use to communicate with each other.
Researchers in Beijing, for example, were able to extend the effective range of a key fob (convincing a car they were close together) with just $22 worth of equipment that anyone can buy. And they were able to do so without the driver even knowing.
Other security researchers hacked a Tesla Model S using a cloned key fob, even though it’s supported by an extensive security team and uses encrypted keys (the encryption turned out to be the weak link).
While both of these were done for the sake of research, Upstream’s data shows a number of real, malicious occurrences of key fob hacking across the globe. Meaning it should be a top concern for automakers.
2. Server Hacks
Server hacks have the potential to be catastrophic in more ways than one, as breaking into a central server gives hackers access to everything: sales data, mobile apps, and even the controls of every vehicle connected to it.
“This can lead to multi-vehicle or fleet-wide attacks, which are extremely risky to all parties involved, from OEMs to telematics service providers, and companies who manage fleets to the drivers themselves,” Upstream mentions in its report.
While a large-scale attack on vehicle controls has yet to occur, researchers Charlie Miller and Chris Valasek proved this threat was possible back in 2015 in a piece by Wired Magazine, when, from their couch, they stopped a Jeep that was traveling 70 mph on a highway.
Large-scale data breaches, on the other hand, have already occurred and have resulted in the exposure of millions of peoples’ sensitive data (Toyota’s server breach in 2019, for example).
3. Mobile App Hacks
The mobile app market has exploded since its inception in 2008, when Apple first launched its App Store. The auto industry joined in soon after.
But while automotive mobile apps have been nice for consumers, the increase in their utilization has also given hackers new ways to access automobiles. And when hackers gain access to the information and control available in automotive apps, the results can be devastating.
For example, one hacker found that he could kill thousands of cars’ engines remotely through two GPS tracking apps (ProTrack and iTrack) by exploiting weak password protocols. And in another instance, a security researcher found that they could control a Nissan Leaf’s functions using just the VIN number from the car’s windshield and the associated mobile app.
Here are four ways manufacturers can address these vulnerabilities and mitigate the risks.
How to Improve Vehicle Cybersecurity and Prevent Automotive Hacking
Unfortunately, there is no one-size-fits-all solution for car cybersecurity. However, based on the most common auto hacking methods above, here’s what we recommend manufacturers do to secure their vehicles.
Threat Detection
Car hackers have more ways to attack your car today than ever before (not to mention ways to hide those attacks too). So it’s critical that you’re able to detect suspicious activity at every vulnerable point before it turns into a breach (and a PR nightmare).
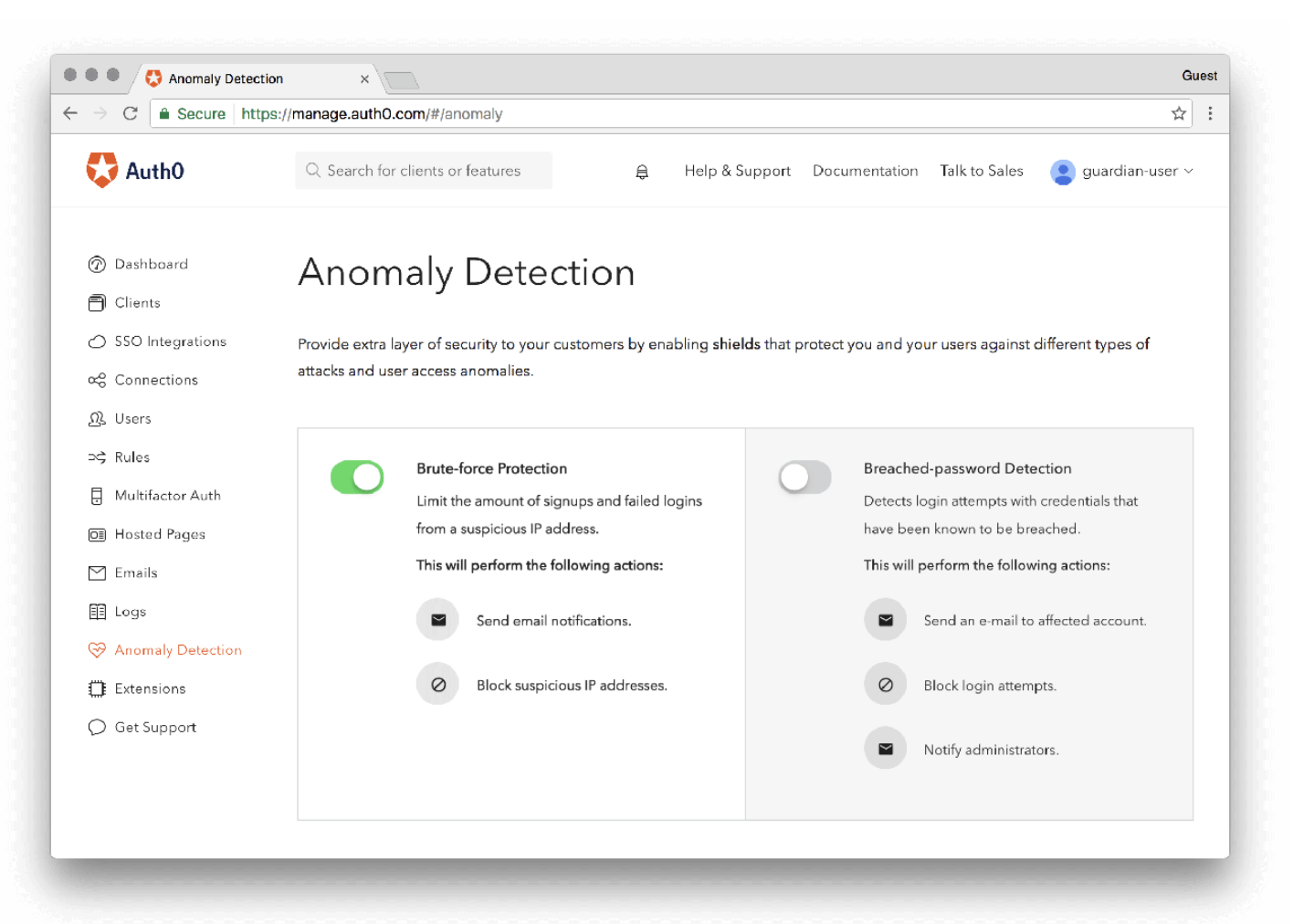
A great example of threat detection for car manufacturers is Auth0’s anomaly detection, which provides both brute-force and breached-password detection (both of which could have helped protect ProTrack and iTrack customers from L&M’s hacking efforts, for instance).
This alerts you to any potentially malicious activity within your system that otherwise may go undetected. And it automatically blocks any unauthorized access that could result in a data breach.
Simpler, More Secure Logins
Many of today’s cars come equipped with a number of remote control features (remote start, for instance). This list will likely only increase as manufacturers continue to increase the number of connected cars they produce.
However, each of these remote access points creates dangerous vulnerabilities if any of them are weak. So it’s critical to secure each one.
This includes improving the encryption on key fob radio frequencies. But maybe, more importantly, it means securing the logins and passwords to mobile apps and critical server access (which would help prevent major breaches like the iTrack and ProTrack vulnerability could create).
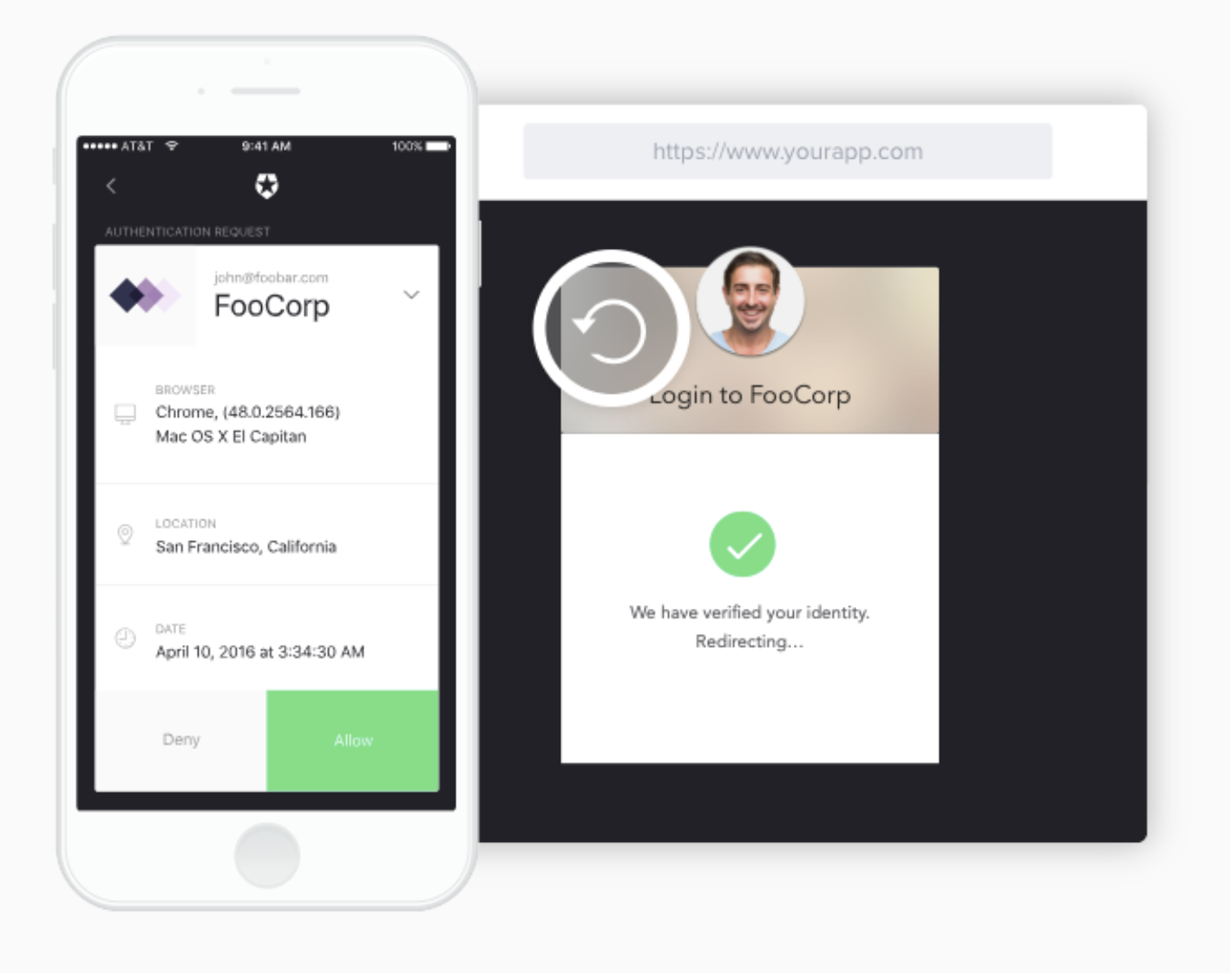
Features like multi-factor authentication (MFA) and biometrics can help secure that access — and block hackers looking for a quick way in. With multi-factor authentication, for example, a user needs more than their name and password to log in. Access requires an additional credential, such as a voice snippet, thumbprint, or mobile device.
However, implementing these authentication features can often create a sluggish user experience. That’s why we created Auth0 Guardian, which streamlines this kind of authentication across devices and secures your systems while keeping authentication as lightweight as possible:
Auth0 Guardian makes multi-factor authentication simple by removing the need for one-time codes. Instead, administrators download the app and approve login requests with the tap of a button. When you’re dealing with a high volume of login requests, Guardian makes the process more efficient, so you can focus on developing and distributing new features.
Regardless of how you go about it, though, it’s critical to confirm user identities at login in addition to monitoring their behavior once they have access. Without this layer of protection, it’s easier for dishonest users to enter a system and wreak havoc.
Secure APIs
APIs are how different proprietary software systems integrate with each other. And as more automotive systems expose APIs for remote access through third-party software, it will be critical that these entry points be protected with modern authentication features to ensure that each one is protected from hackers.
One way to do that is by using the OAuth Device Flow — an emerging standard for securing cloud APIs that devices like in-car systems reach out to directly.
Device Flow extends browser-based authentication to input-constrained devices, allowing users to sign in to their accounts via a secondary device (such as a smartphone). This offers a secure and convenient way to ensure the right user is in control and lets developers integrate authentication features like threat detection and multi-factor authentication directly through other devices.
Device Flow is already used to authenticate people accessing their favorite streaming services sitting on a couch in the living room in front of the TV, for example. But it can also be applied to in-car systems that have limited input functionality (in-car infotainment systems that have cumbersome keyboard input, for instance).
Adaptable Cybersecurity Solutions
The auto industry is extremely dynamic. And to keep up with the changes that occur on the cybersecurity front, your systems for threat detection, authentication, and identity management must be flexible enough to support your shifting business goals.
Your infrastructure should be able to adapt to changes like:
- New features. These could introduce new entry points/vulnerabilities that you’ll need to address.
- New ways and places to use those features. For example, some users may want to connect their cars to local Wi-Fi hotspots when they park at a restaurant, introducing a potential security threat.
- New ways, hackers can access automobile systems. Hackers are always looking for weaknesses to exploit. So staying on top of any new developments in the automotive industry is critical.
However, when your IT team is busy with daily operations, it can be difficult to create systems that meet your current requirements and are also able to transform based on future priorities.
That’s where an outsourced identity provider can take the burden of keeping pace with evolving standards and threats off your shoulders. Auth0, for instance, offers its partners 100+ pre-built Rules and Extensions (along with the ability to write original code) that allow you to tailor your user management systems as your needs change.
Rules can enrich user profiles, notify other systems via an API when a specific login occurs, deny access to a white list of users, and more. For a full list, see here.
Manufacturers Must Lead the Way
While the modern connectivity features of today’s cars are a wonderful thing, it also means vehicle security is a lot more complicated than remembering to lock the doors these days.
There are a whole host of vulnerabilities that the average consumer simply cannot secure. And as a result, it’s up to manufacturers to step up and lead the way.
Auth0 has helped companies like Mazda secure their automotive systems from car hacking. Learn more about how Auth0 could help you improve your cybersecurity as an auto manufacturer here.
About Auth0
Auth0 by Okta takes a modern approach to customer identity and enables organizations to provide secure access to any application, for any user. Auth0 is a highly customizable platform that is as simple as development teams want, and as flexible as they need. Safeguarding billions of login transactions each month, Auth0 delivers convenience, privacy, and security so customers can focus on innovation. For more information, visit https://auth0.com.
About the author

Diego Poza
Sr Manager, Developer Advocacy (Auth0 Alumni)