TL;DR: Credential stuffing can threaten user accounts and service availability. Security expert Duncan Godfrey shows how Auth0 defends customers with breached password protection.
Anyone operating a web application which authenticates users will know credential stuffing attacks all too well. It’s a constant hum of bots knocking on your infrastructure trying to take over user accounts. OWASP defines it as "the automated injection of breached username/password pairs in order to fraudulently gain access to user accounts."
Credential stuffing is an efficient type of brute force attack which uses the vast amount of available breached user credentials to exploit the still all too often story of users reusing their passwords across different services.
The most recent Akamai State of the Internet Report focuses on credential stuffing and gives some insight into the scale of the problem — between May to June 2018 they recorded 8.35 million credential stuffing attempts. It brings into focus the dire state of using passwords as a single authentication factor in 2018. As Auth0 handles authentication for our customers, we find ourselves at the epicenter of these kinds of attacks.
“@akamai_soti reported 8.35M credential stuffing reports in a single month. Security expert @duncangodfrey shares how to protect your customers with the help of @auth0.”
Tweet This
On particularly busy days at Auth0, we will detect up to 600K logins being made with known breached passwords. The attacks are not always random and are often targeted against companies whose customers resources can be drained or where access to the account itself can be sold (i.e. it gives access to premium content).
Defending Credential Stuffing with Breached Password Detection
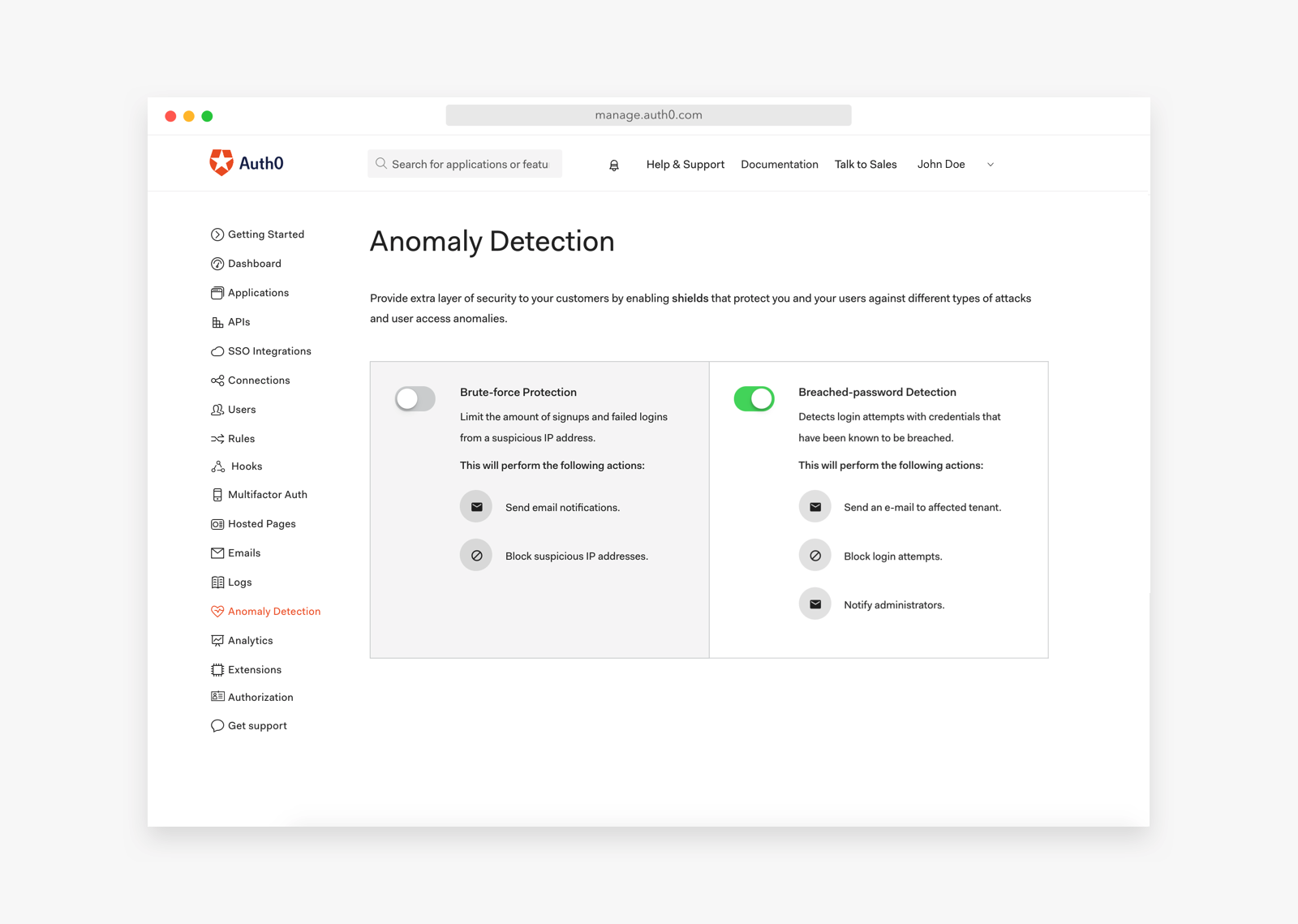
In response to the growth of credential stuffing attacks, we developed the breached password detection service to help our customers defend their users. Once enabled, the service will monitor for logins using known compromised credentials and can be set to lock out that user until they have reset their password.
The botnets that carry out these attacks not only threaten our customers’ accounts but they are a threat to the availability of our service. An attacker can slowly try the credentials aiming to avoid detection or they can burst attempts using all their capacity to test credentials as quickly as possible. When that happens it is effectively a DDoS attack — so we have to proactively manage our capacity, scaling, and rate limiting to protect our customers and our infrastructure.
Auth0 maintains a continuously-updated collection of breached credentials, with hundreds of millions of entries. All password-based login attempts are checked against this database, and any matches are blocked in real-time. Auth0 offers a free tier to get started with modern authentication. Check it out, or sign up for a free Auth0 account here!
FTC: "Innocent Corporate Victim" No Defense
Credential stuffing is also a developing legal threat to companies who hold sensitive data for their customers. The Federal Trade Commission (FTC) recently took action against online tax preparer TaxSlayer because they were leaving customer data open to credential stuffing, going so far as to state that being an “innocent corporate victim” was no defense in an enforcement case. Rather, in the FTC’s view companies holding sensitive customer information should be taking proactive action to reduce the risk of credential stuffing.
There are things which can be done now to reduce the risk of automated attacks. Firstly, they are not effective against logins protected with MFA. Authenticating with two factors should be considered a minimum good practice for protecting your users. The TaxSlayer attack was halted when the company implemented MFA.
Educating your users against reusing their passwords and helping them to improve their password hygiene can help protect your users and your business. Password management apps like 1Password or lastpass make maintaining a unique password for all your accounts more manageable.
“Automated cyber attacks can be overwhelming. Protect your customers with tips from @auth0 security expert @duncangodfrey.”
Tweet This
The reality is that right now it’s just too simple for attackers. This is an Internet-scale security problem and one which we are working actively with our customers to solve. Auth0 was created to help make managing authentication simple for everyone, and, underpinning that is the desire to make it secure for everyone too.
About Auth0
Auth0 by Okta takes a modern approach to customer identity and enables organizations to provide secure access to any application, for any user. Auth0 is a highly customizable platform that is as simple as development teams want, and as flexible as they need. Safeguarding billions of login transactions each month, Auth0 delivers convenience, privacy, and security so customers can focus on innovation. For more information, visit https://auth0.com.
About the author

Duncan Godfrey
Sr. Director of Security and Compliance (Auth0 Alumni)