The shift to the cloud is accelerating. Teams of all sizes, including giants like Microsoft, IBM and SAP, are racing to catch up (as we just saw with SAP's enormous recent acquisition of Qualtrics).
Every company wants to become faster, smarter, more nimble, and more secure. The best place to begin improvements is with your customer relations. A strong customer identity and access management (CIAM) strategy can be the cornerstone of a team's success. It helps you organize your sensitive customer data in a single place, which ensures you're compliant with current regulations. It can also help you form a more creative and targeted strategy moving forward.
Moreover, if you're going through a digital transformation, maintaining continuous customer engagement throughout this challenging process can help keep sales on track.
What a CIAM solution allows you to do:
- Create a single view of your customers from disparate pieces of data.
- Reduce customer churn with frictionless registration.
- Stay safe in an environment with rising cybercrime.
We dig into these three benefits below and highlight how Auth0's customer identity and access management tools can help you achieve your goals.
1. Why customer identity and access management is the first step in single view.
Single view is becoming the norm for teams that wish to stay competitive. While this is especially clear among retail and media companies, it's highly relevant for all customer-facing teams. Catering to customers requires an in-depth knowledge of their interests and behaviors.
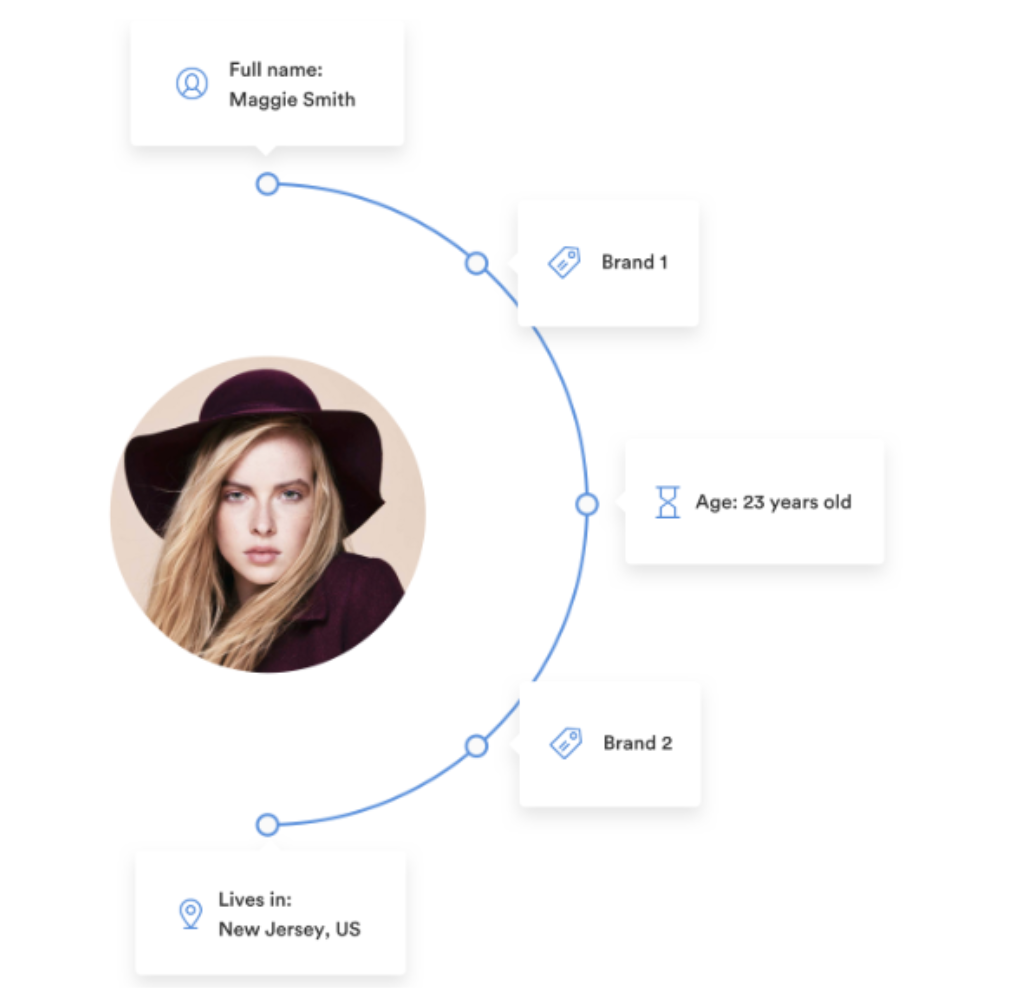
Outsourced CIAM providers like Auth0 are able to create an extensive profile for each user in a company's system, which tracks and manages their logins and devices along with their purchase histories.
Auth0 facilitates the collection of customer data from all available public sources that combine into a comprehensive picture that you can use to underpin more targeted marketing materials, communications, and product rollouts. Knowing that Maggie Smith is 23, for example, will ensure you don't try to push products for aging on her. You can focus instead on developing a relationship, based on her millennial interests.
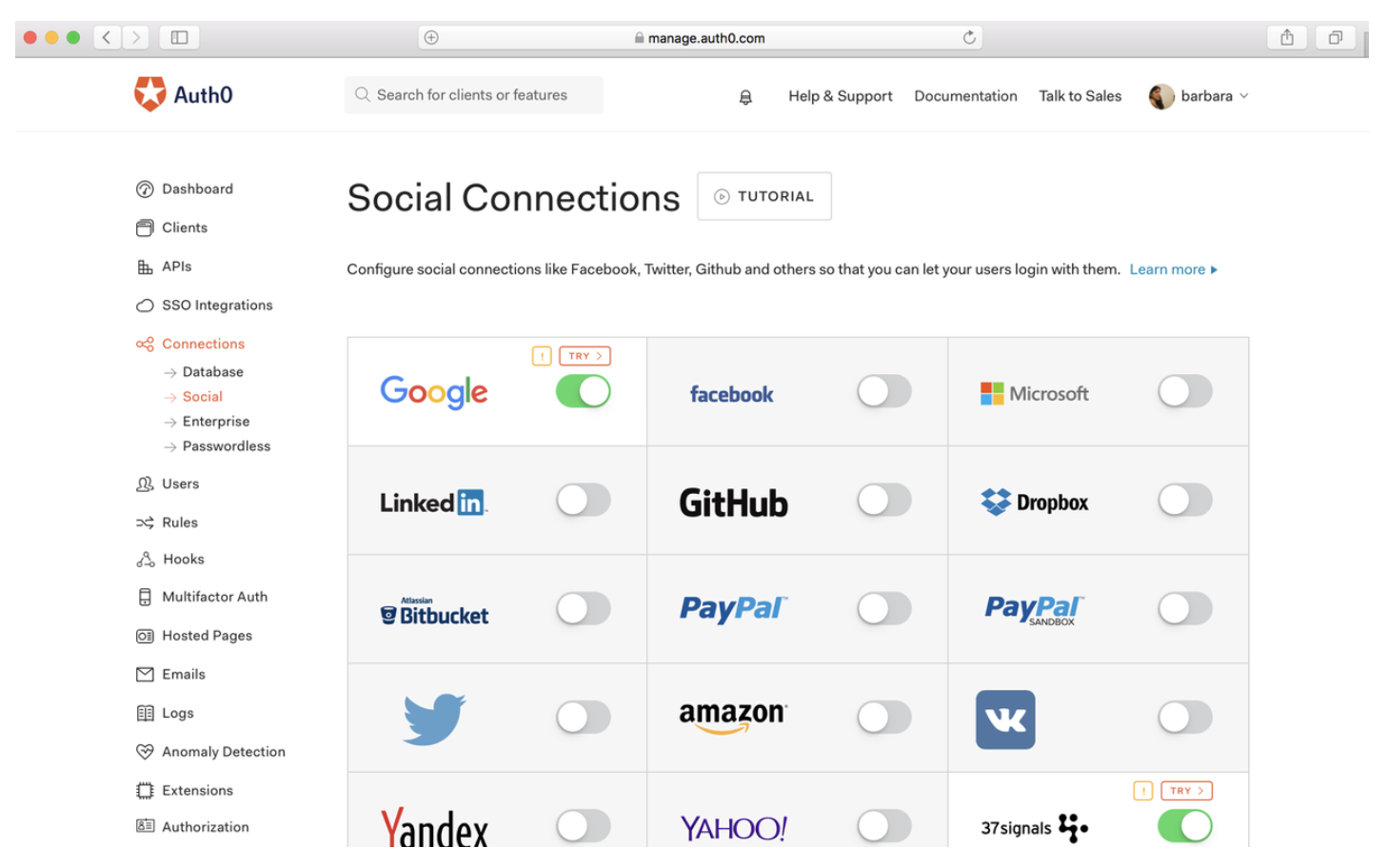
If your company opts for social login, this profile will also pull Maggie's specific interests from the social providers you choose for authentication.
If a user opts to log in from multiple sources (e.g., both Facebook and Google), your team can link these accounts back together, integrating both sets of information.
A single, detailed view of each of your customers is an excellent starting point for integrating this rich information into your CRM and making more calculated decisions — such as tailoring which pieces of content your users see. Matching articles and/or advertisements to your audience's specific likes, interests, and histories can give them a more personalized experience on your platform and ensure you stay a step ahead of the competition.
2. How frictionless registration keeps customers engaged.
Customer retention is an enormous concern for teams today — particularly when the cost of switching among products and services is low, and product reviews and complaints are ubiquitous, along with nearly every other piece of information about your company via social media and a constant stream of news.
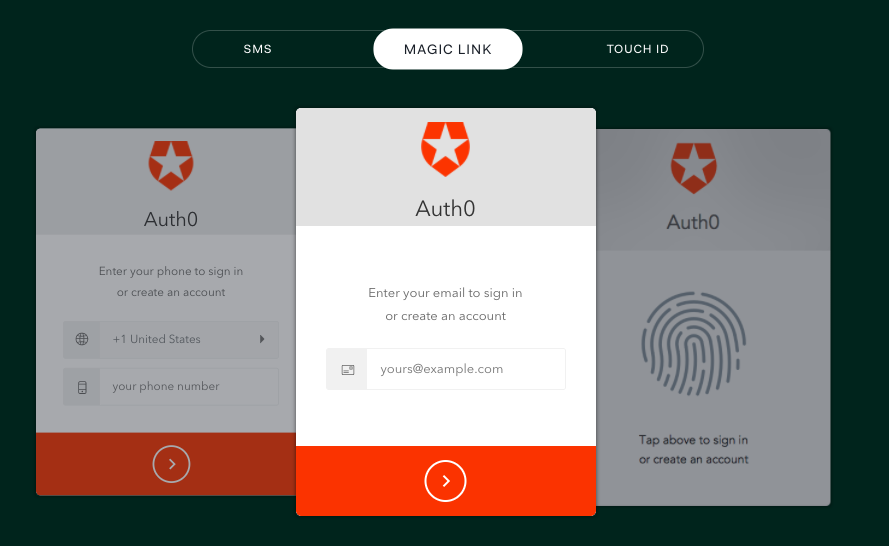
Yet there's still an enormous opportunity to shine and create a better experience for your users in this environment. Many companies still struggle with bad login UX. Users often have to refresh tabs several times just to access a homepage. They quickly lose interest if they have to recover a password more than once. A CIAM strategy that encompasses passwordless methods, however, can ensure success:
SMS, magic link, and Touch ID are three tools Auth0 uses to help its customers ensure a smooth set-up process.
- SMS involves users entering just their phone number to sign up.
- Magic link relies on just an email address.
- Touch ID uses your unique thumbprint.
In addition to simplifying sign-ups, these three solutions contribute to a consistent user experience after an account is created, supporting a higher level of engagement with a company's suite of products and/or services over the long term.
Finally, passwordless authentication can also help mitigate the insecure practice of users recycling the same password for several accounts when a password reset procedure is triggered. This feature is easy to implement with a robust provider like Auth0.
3. How an outsourced customer identity and access management provider can help you secure sensitive data.
In addition to being a cornerstone of your team's growth strategy, an impenetrable CIAM setup can help ensure the data of your users is safe from cyberthreats.
Several studies show that data breaches are on the rise. According to Dark Reading, 2018 is set to be one of the worst years in history for data breaches, with more than 3,600 reported breaches and over 3 billion records exposed. While no tool can 100% guarantee the safety of user data, CIAM mitigates the risk of your company shelling out for fines and lawsuits in the short term and potentially losing its good standing in the long term.
Users will appreciate your implementation of multi-factor authentication (MFA), for example — i.e., relying on additional sets of information, such as SMS codes, fingerprints, or voice recognition to gain access.
Auth0 Guardian can make the process of switching to MFA simple. In fact, it even makes MFA itself easier by allowing immediate approvals or denials a login attempt — from a desktop or mobile device (including Android Wear or an Apple Watch).
MFA has a strong success rate for keeping cyberthieves out—largely because it avoids reliance on passwords. A 2017 study found that breached passwords were responsible for 81% of data breaches (up from 66% in 2016).
Tracking and securing your customer data is essential to maintaining integrity; however, if you're processing any data of EU citizens, it is also critical for complying with GDPR. With fines for non-compliance being up to €20 million or 4% of the global annual revenue (whichever is greater) — even if your team is an industry leader, the financial and reputational costs of thieves stealing this sensitive information could be a hard recovery.
Go beyond customer identity and access management: think platform identity and access management
Many companies have yet to make the investment to modernize — regardless of industry. Consumer packaged goods and automotive companies, for example, lag furthest behind — only completing 31% and 32% of the digital shift they need, according to recent research from McKinsey.
The separation between those that have made the right updates and those who haven't is stark: as digitization sweeps through all industries, McKinsey finds that companies in the top quartile of modernization will capture disproportionate gains, while those in the bottom quartile will see increasingly depressed revenue and profit growth. The gap will continue to widen.
CIAM can help ensure your team is a leader within its peer group by improving your interactions with customers.
While customer identity and access management is a critical component of a digital shift, it cannot solve all of your organization’s needs. Companies must consider B2B, B2E and IoT use case scenarios as well. A combination of CIAM with B2B or B2E use cases, in particular, can help you achieve and maintain an industry-leading position.
About the author

Martin Gontovnikas
Former SVP of Marketing and Growth at Auth0 (Auth0 Alumni)
Gonto’s analytical thinking is a huge driver of his data-driven approach to marketing strategy and experimental design. He is based in the Bay area, and in his spare time, can be found eating gourmet food at the best new restaurants, visiting every local brewery he can find, or traveling the globe in search of new experiences.View profile