Previously, we wrote about the emerging pattern of Serverless Extensibility. Examples of the concept are popping up in many of the services you use daily like Twilio and here at Auth0. In this post, I will talk about challenges our customers were facing with our Auth0 Identity product, and how this led us down the path toward implementing the extensibility pattern in a variety of features.
The problem
Placed into the public domain by NASA using Creative Commons
In the early days at Auth0, there were two groups: Core and Field Engineering. Core focused on the core functionality of the authentication product, and the field engineers helped customers use the product in their applications. The company was discovering what customers needed in the product.
Our customers' focus was on the authentication transaction. A lot of interesting features can attach to the process of someone trying to login:
- Profile Enrichment
- Progressive Profiling
- Authorization
- Claims Transformation
Customers will come up with an unlimited supply of feature requests. We could not possibly build every feature at once.
Moreover, sometimes building features into the core product for customers is not the right approach. We needed a way to try ideas out. An idea may sound great, but in practice be problematic. Investing core engineering resources to these ideas is very expensive.
"The primary use case for extensibility at Auth0 was to empower field engineers to work on the last mile solutions for the customer without involving core engineering."
Eugenio Pace - Co-Founder, CEO
If every interaction with a customer involved identifying an idea, putting it in the backlog and coming back to them at a later date, it would add friction to the process and turn customers away.
For example, we had customers who wanted to do profile enrichment. They used services like FullContact to look up a new user and grab related information about them such as their company, role, and social media accounts. FullContact is just one service as there are several others. We had prospects that were depending on these capabilities to have confidence in using us as a platform, and without it would not become customers.
Custom code extensibility
NASA licensed under Creative Commons 2.0
To solve this problem, we introduced a method of adding custom code into the platform that could be defined by customers. The inspiration for custom code extensibility as a solution came from spreadsheets. Excel has significant functionality out of the box, but you can always add a function, macro or calculation that better reflects your goal. Moreover, you can write them yourself directly in Excel, removing the dependency on Microsoft engineers.
"We wanted a similar experience for our users. A user should be able to log in to the dashboard, write a small amount of node.js code that executes later during authorization transactions."
Eugenio Pace - Co-Founder, CEO
Like Excel, we wanted to offer users a really simple experience for customizing our product through code. We believed a user should be able to write their logic in an editor, debug it in place, and make it live in production, all without having to stand up a service. This differed from the prevalent approach at the time for dealing with customization through webhooks, which were hosted by the user.
We quickly implemented an MVP to prove out the concept. It created a process boundary between the core Auth0 stack and the customer's code. It primarily prevented well behaved, well-intentioned code from accidentally bringing down the authorization service or other sandboxed code.
Although the MVP had its limitations, it proved that the user experience for customization could be greatly improved, aligning well with our philosophy of "Identity made simple for developers."
Evolving customization features
NASA licensed under Creative Commons 2.0
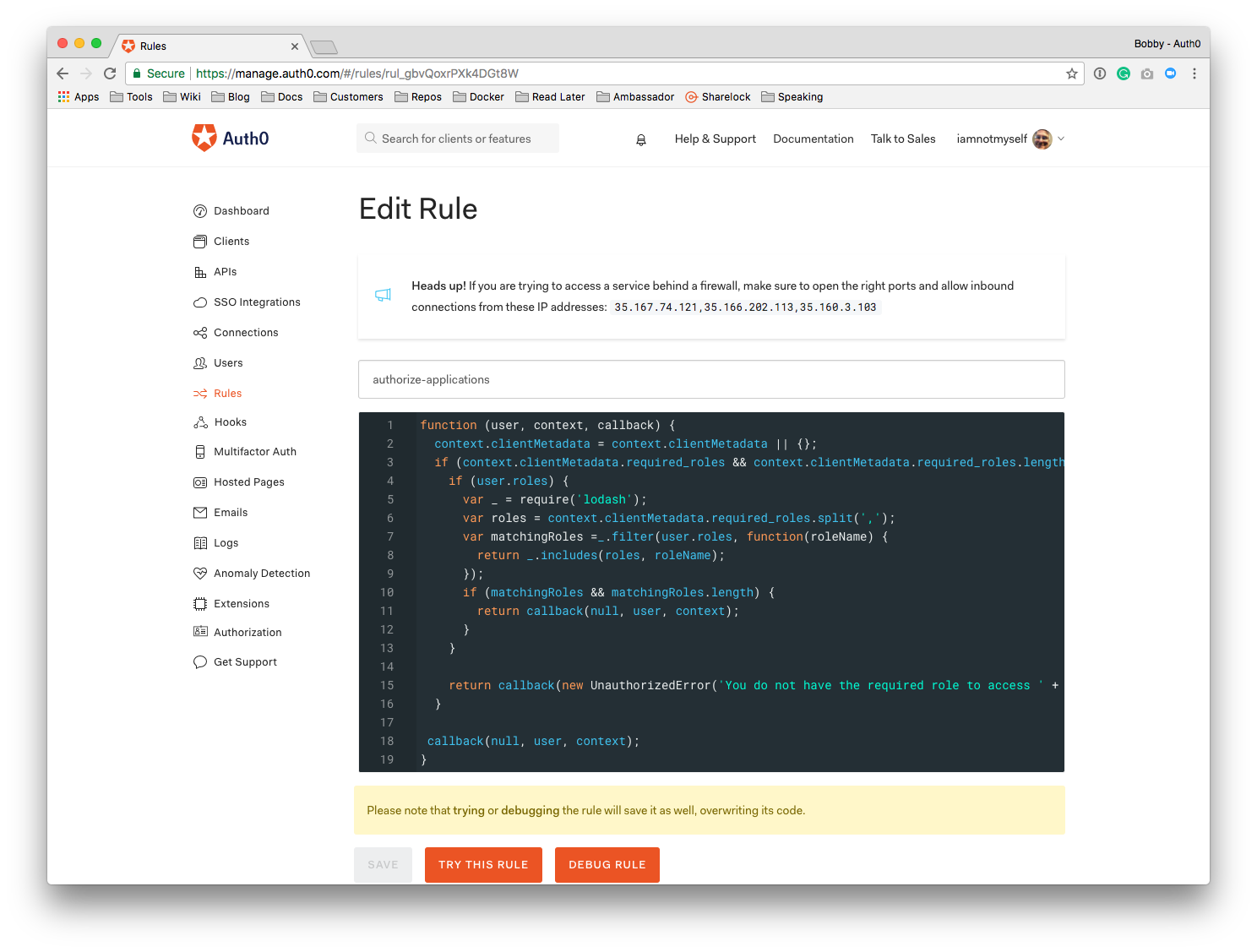
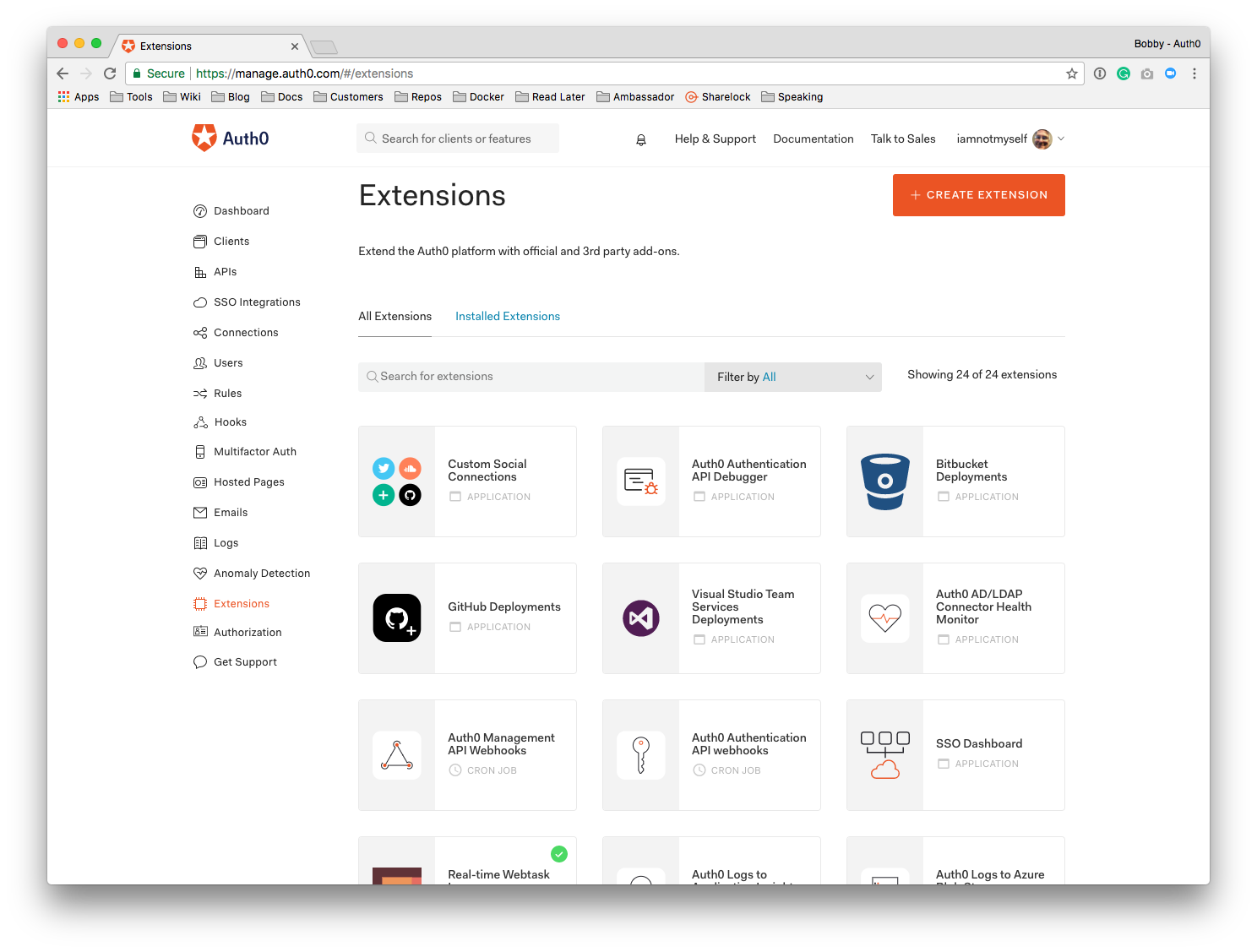
Custom code extensibility is exposed in our customer dashboard in three ways: Auth0 Rules, Hooks, and Extensions.
Auth0 Rules were the first publically available use case where our customers could easily add custom functionality to their authorization flow directly in the dashboard. Rules execute after authentication but before authorization. We offer a gallery of Rule templates that make it easy for customers to address common scenarios out of the box. Because Rules are code though, customers can easily customize the logic further to meet their specific needs.
A customer clicks a button to add a new Rule, selects one from a set of standard templates which they can customize with a simple editor right in their browser. When saved, the Rule is active on their account for all authentication requests.
Rules allow you to easily customize and extend Auth0's capabilities. They can be chained together for modular coding and can be turned on and off individually.
Rules were really powerful but were limited only to login. Once customers got a taste of rules, they started to ask us for more places where they can customize the product, and so Hooks were born.
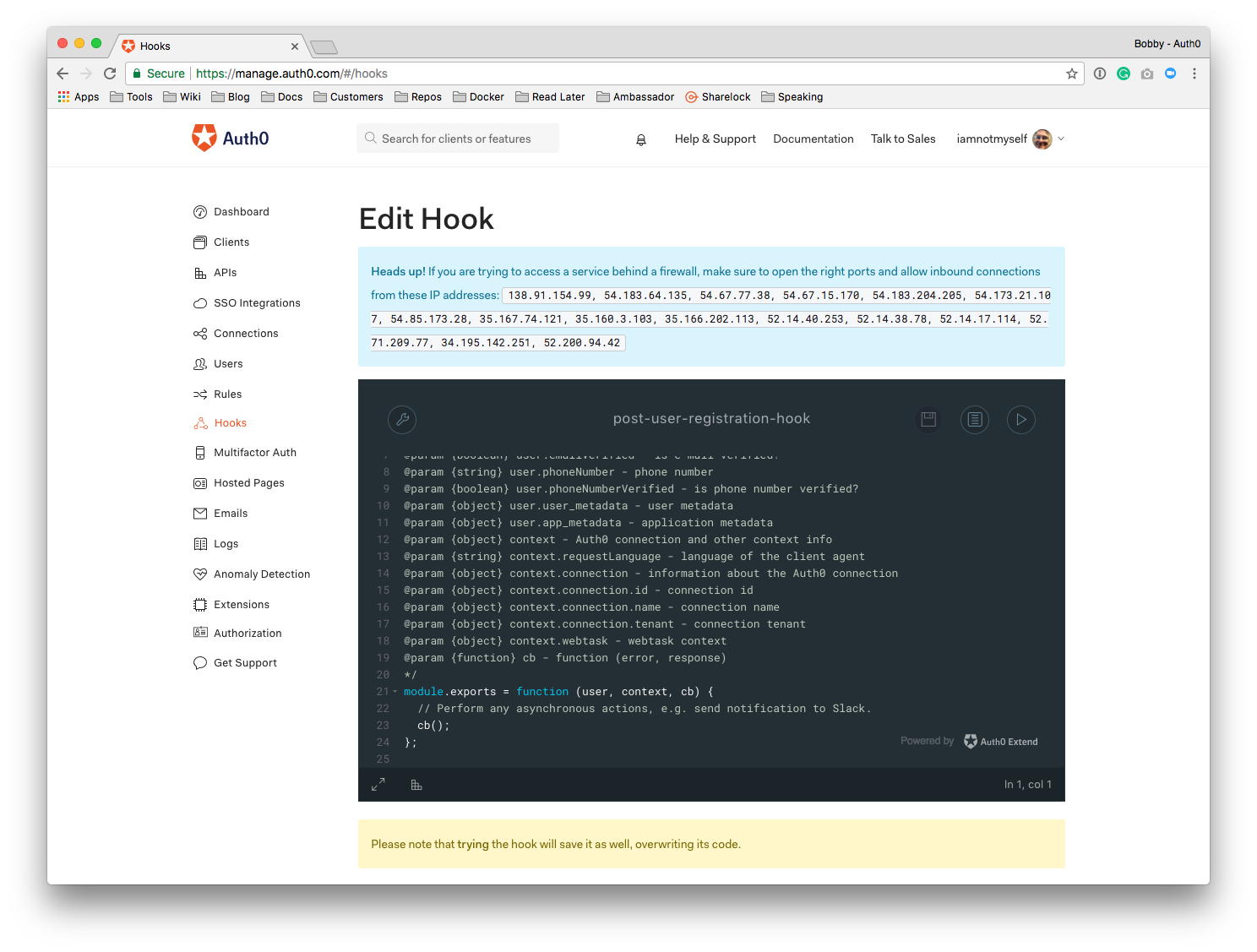
Auth0 Hooks allow you to customize the behavior of Auth0 using custom code that is executed against several extensibility points. Not only can you introduce customization during the client credentials exchange, but also pre and post user registration. Hooks also take advantage of a more feature rich editor.
While both Auth0 Rules and Hooks give you fine-grained control of the authentication pipeline, Auth0 Extensions are mini-applications that extend the Auth0 identity product with 3rd party integrations.
They do not directly tie to any specific event in the system. Instead, they can invoke any Auth0 API, can configure the customer tenant, deploy Hooks or Rules on installation and even have an associated user interface. They are extremely powerful and opened up many use cases.
Auth0 Extensions are written using the Webtasks infrastructure. Customers can select an Extension from our gallery and provide a set of configuration options to begin using one.
This is just the beginning. We're constantly looking to enable richer and richer customization in our product, and you'll continue to see us opening new doors as we learn.
The impact on our sales engineers and customers
Placed into the public domain by NASA using Creative Commons
Adding extensibility to the identity product opened up a window of customization where field engineers could work independently from core engineering. They could deliver customizations very quickly without waiting weeks or even days, enabling many successful sales engagements.
"In some cases, we were able to deliver demos where we implemented feature requests in the demo during the meeting. It was amazing for field engineers and our customers."
Eugenio Pace - Co-Founder, CEO
Putting extensibility into the hands of customers also gives us great insights into where the market is going. If we see an extension being implemented again and again through the use of custom code, that is a validation of that feature and an opportunity to add in the core product.
Multi-Factor Authentication came about this way. MFA was not a switch on the dashboard initially. It was merely a rule you applied to your account. Over time, our customers' usage of this rule indicated MFA was an important feature to have in the core product.
For more examples, take a look at our rules repository on Github. Every single one comes from a real-world customer use case.
"Every event in the life cycle of the user can be expressed through code and in that way we can support any backend out there in a flash. No matter how customers encrypt or hash passwords; whatever they do is supported because they can provide the details using custom code."
Sandrino Di Mattia - Engineering Lead
The impact on our business
Not only did we make our customers happier, opening up customization provided us a direct return on revenue. Looking at our data, we found our customer retention increased up to 10x for those users that took advantage of customizing. Not only that, but our largest deals depend on these customizations even today, bringing 70% of our cloud revenue.
Summary
In the past four years, we've been exploring how to better enable our users to customize and extend our SaaS. On our journey, we discovered the Serverless Extensibility pattern provided a great solution. We found that allowing extensions to be authored in-line provided tremendous value both to our customers and to the business. It allowed us to close more deals and deliver customer features much more quickly and cheaply than before.
I would like to thank Eugenio Pace, Sandrino Di Mattia and Tomasz Janczuk for taking time out of their busy schedules to be interviewed for this post.
About Auth0
Auth0 by Okta takes a modern approach to customer identity and enables organizations to provide secure access to any application, for any user. Auth0 is a highly customizable platform that is as simple as development teams want, and as flexible as they need. Safeguarding billions of login transactions each month, Auth0 delivers convenience, privacy, and security so customers can focus on innovation. For more information, visit https://auth0.com.
About the author

Bobby Johnson
Developer Advocate Engineer