Auth0 implements Connect’s RP-Initiated Logout 1.0 for end-user logout. This standard is part of the OpenID Connect collection of final specifications.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
How it works
RP-Initiated Logout is a scenario in which a (user) requests the OpenID provider (Auth0) to log them out.- The user initiates a logout request in your application.
- Your application directs the user to the Auth0 Authentication API OIDC Logout endpoint.
- Auth0 redirects the user to the appropriate destination based on the provided OIDC Logout endpoint parameters.
Configure RP-Initiated Logout
To configure RP-Initiated Logout, you must ensure that your application can find theend_session_endpoint parameter in your Auth0 tenant’s discovery metadata document, and that it calls the OIDC Logout endpoint with the necessary parameters.
Enable endpoint discovery
For Auth0 tenants created on or after 14 November 2023, RP-Initiated Logout End Session Endpoint Discovery is enabled by default.
- Dashboard
- Management API
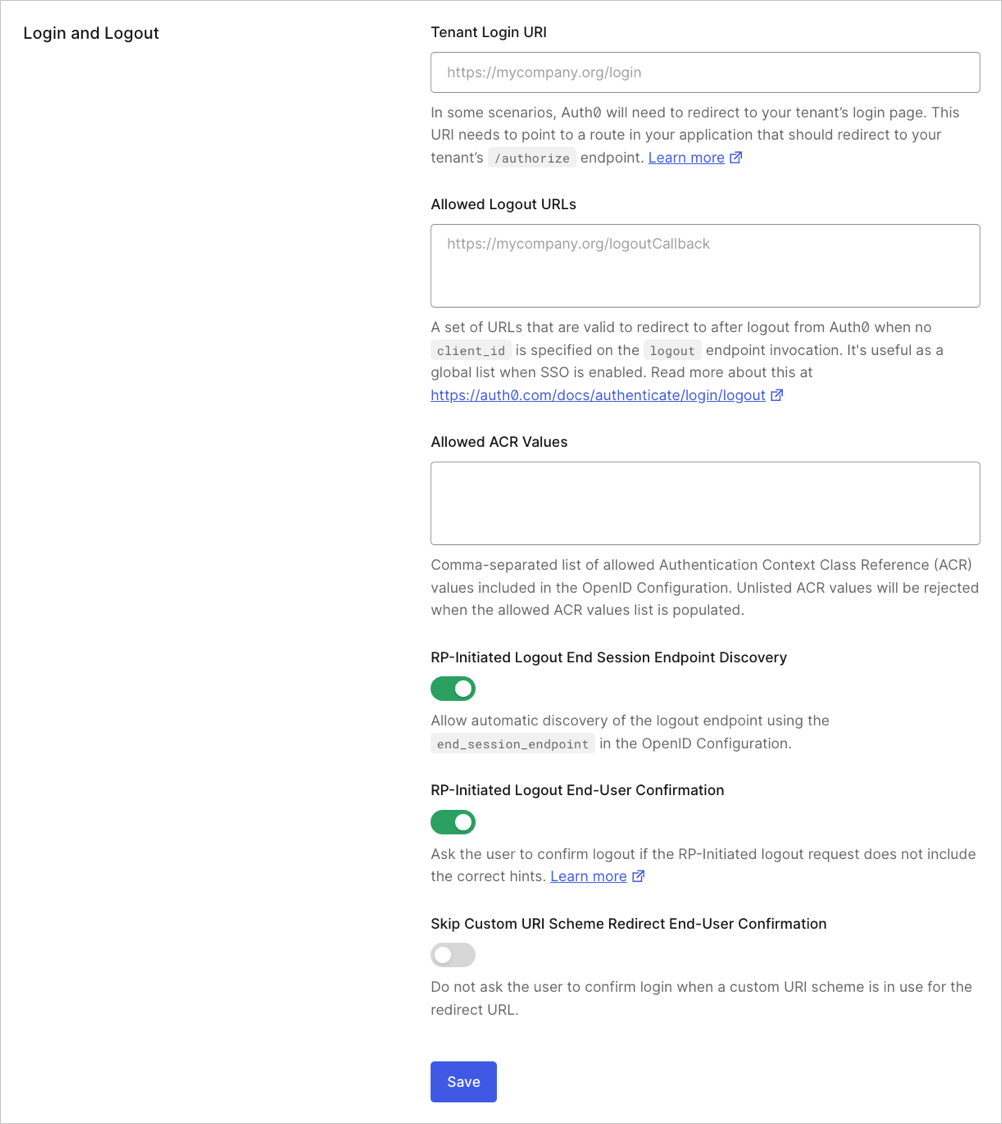
To enable RP-Initiated Logout End Session Endpoint Discovery in the Dashboard:
- Go to Dashboard > Settings > Advanced.
- Locate the Login and Logout section.
- Enable the RP-Initiated Logout End Session Endpoint Discovery toggle.
Call the OIDC Logout endpoint
Most of Auth0’s SDK libraries are OIDC-compliant and support RP-Initiated Logout by design.
id_token_hint parameter.
If your application cannot securely store , you may provide the logout_hint and client_id parameters instead.
You may call the OIDC Logout endpoint with redundant information.For example, you may send the
id_token_hint and logout_hint parameters, or the id_token_hint and client_id parameters.In all cases, Auth0 checks for consistent user and session data, and returns an error if there are any discrepancies.OIDC Logout endpoint parameters
The Authentication API OIDC Logout endpoint supports the following parameters:| Parameter | Required? | Description |
|---|---|---|
id_token_hint | Recommended | ID token previously issued for the user. That indicates which user to log out. |
logout_hint | Optional | Session ID (sid) value that indicates which user to log out. |
post_logout_redirect_uri | Optional | Redirect URL value that indicates where to redirect the user after logout. |
client_id | Optional | Client ID of your application. |
federated | Optional | Directs Auth0 to log the user out of their identity provider. |
state | Optional | Opaque value that the application adds to the initial logout request, and that Auth0 includes when redirecting the back to the post_logout_redirect_uri. |
ui_locales | Optional | Space-delimited list of locales used to constrain the language list for the request. The first locale on the list must match the enabled locale in your tenant. |
id_token_hint parameter
Auth0 recommends that you use the
id_token_hint parameter when you call the OIDC Logout endpoint.id_token_hint parameter must be the ID token that Auth0 issued to the user after they authenticated.
The ID token contains the registered claims issuer (iss), (aud), and the Auth0 session ID (sid) for verification. To learn more about ID token claims, read ID Token Structure.
Examples
logout_hint parameter
The value of thelogout_hint parameter must be the session ID (sid) of the user’s current Auth0 session.
The session ID (sid) is provided as a registered claim within the ID token that Auth0 issued to the user after they authenticated.
Example
post_logout_redirect_uri parameter
The value of thepost_logout_redirect_uri parameter must be a valid, encoded URL that has been registered in the list of Allowed Logout URLs in your:
- Application settings: If you provide the
id_token_hintparameter, or thelogout_hintandclient_idparameters. - Tenant settings: If you provide only the
logout_hintparameter.
Example
Update application Allowed Logout URLs
You can register a URL with your application’s list of Allowed Logout URLs in the Auth0 Dashboard or with the Auth0 Management API.- Dashboard
- Management API
To register a URL with your application’s list of Allowed Logout URLs in the Dashboard:
- Go to Dashboard > Applications > Applications.
- Select your application.
- Locate the Application URIs section.
- Update Allowed Logout URLs following the provided guidelines.
Update tenant Allowed Logout URLs
You can register a URL with your tenant’s list of Allowed Logout URLs in the Auth0 Dashboard or with the Auth0 Management API.- Dashboard
- Management API
To register a URL with your tenant’s list of Allowed Logout URLs in the Dashboard:
- Go to Dashboard > Settings > Advanced.
- Locate the Login and Logout section.
- Update Allowed Logout URLs following the provided guidelines.
Allowed Logout URLs guidelines
When you update Allowed Logout URLs, follow the guidelines below to avoid validation errors:- Separate multiple URL values with a comma (
,). - Include the URL scheme part (for example,
https://).
*) as a wildcard for subdomains (such as https://*.example.com), but we recommend that you do not use wildcards in production environments. For more information, read Subdomain URL Placeholders.
Add query string parameters to post_logout_redirect_uri
The OIDC Logout endpoint parses query string parameters in the URL provided to thepost_logout_redirect_uri parameter.
You must include the exact URL with query string parameters in your Allowed Logout URLs, or the logout request will be denied. The URL must match exactly, including all query parameter names and values.
For example, if you pass https://example.com/logout?myParam=1234 to the post_logout_redirect_uri parameter (encoded as https%3A%2F%2Fexample.com%2Flogout%3FmyParam%3D1234), you must include the complete URL https://example.com/logout?myParam=1234 in your Allowed Logout URLs.
ui_locales parameter
The value of theui_locales parameter must be a space-delimited list of supported locales.
The first value provided in the list must match your tenant’s Default Language setting.
federated parameter
Thefederated parameter does not require a value.
If you include the federated parameter when you call the OIDC Logout endpoint, Auth0 attempts to log the user out of their identity provider.
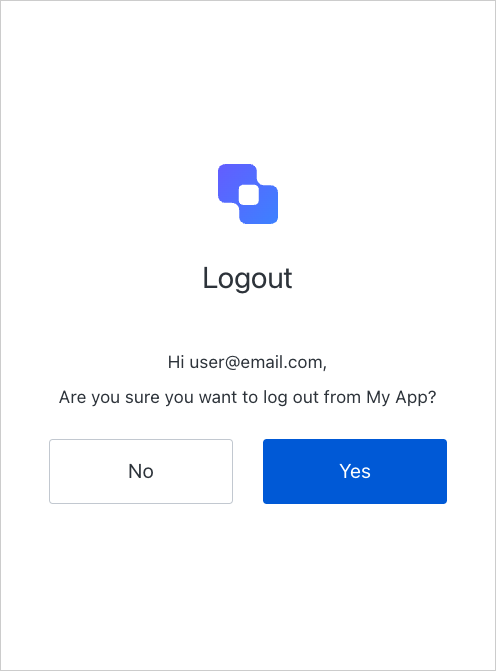
Logout consent prompt
The OIDC standard defines that the logout flow should be interrupted to prompt the user for consent if the OpenID provider cannot verify that the request was made by the user. Auth0 enforces this behavior by displaying a logout consent prompt if it detects any of the following conditions:- Neither the
id_token_hintnorlogout_hintparameters are provided. - The ID token’s
sidclaim does not correspond to the browser session in the request. - The value of the
logout_hintparameter does not match current session data.
Disable the logout consent prompt
You may disable the logout consent prompt. If you do, Auth0 does not attempt to detect anomalous behavior and accepts logout requests automatically. To disable the logout consent prompt in the Dashboard:- Go to Dashboard > Settings > Advanced.
-
Disable the Show RP-Initiated Logout End-User Confirmation toggle.