Auth0 allows you to quickly add authorization to your application. This guide demonstrates how to integrate Auth0
with any new or existing Spring Boot application.If you have not created an API in your Auth0 dashboard yet, use the interactive selector to create a new Auth0 API
or select an existing API that represents the project you want to integrate with.Review our getting started
guide to set up your first API through the Auth0 dashboard.Each Auth0 API uses the API Identifier, which your application needs to validate the access token.
New to Auth0? Learn how Auth0 works
and read about implementing API authentication
and authorization using the OAuth 2.0 framework.
Permissions let you define how resources can be accessed on behalf of the user with a given access token. For
example, you might choose to grant read access to the 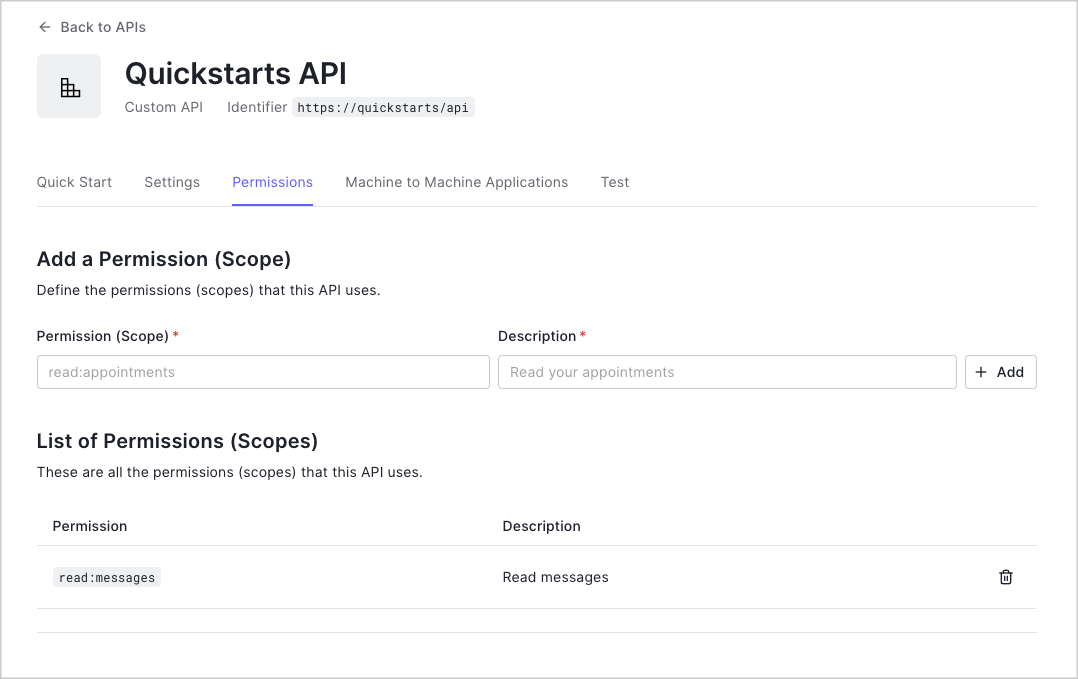
messages resource if users have the manager
access level, and a write access to that resource if they have the administrator access level.You can define allowed permissions in the Permissions view of the Auth0 Dashboard’s APIs section.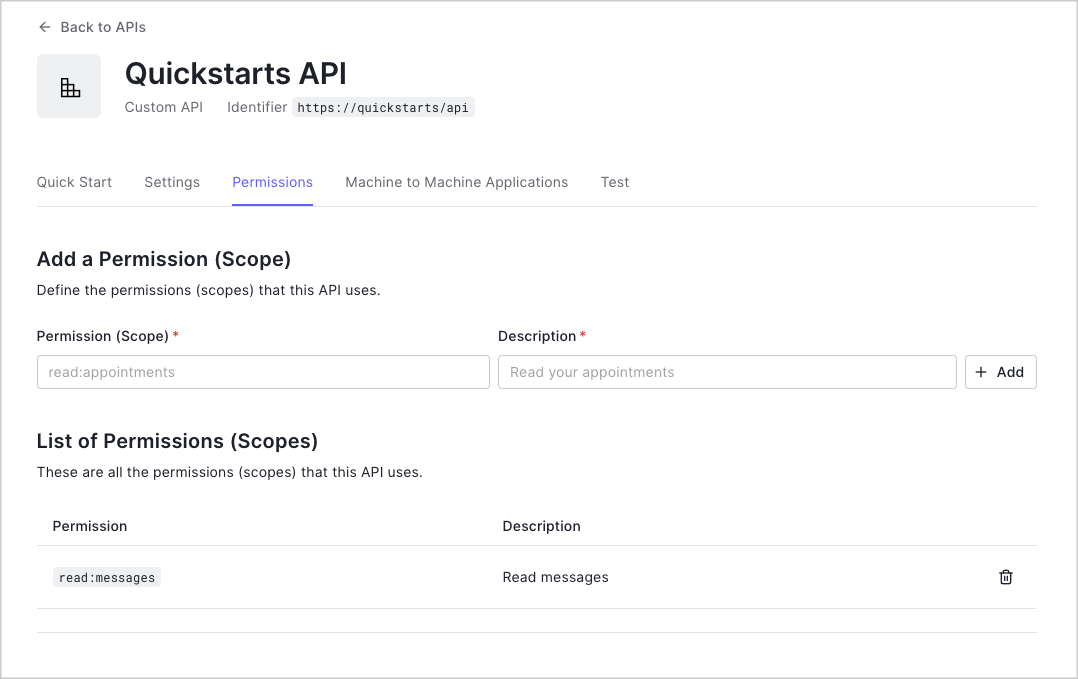
This example uses the
read:messages scope.The sample project uses a
/src/main/resources/application.yml file, which configures it to use the
correct Auth0 domain and API Identifier for your API. If you download the code from this page it
will be automatically configured. If you clone the example from GitHub, you will need to fill it in yourself.If you are using Gradle, you can add the required dependencies using the Spring Boot Gradle Plugin and the Dependency Management Plugin to resolve dependency versions:If you are using Maven, add the Spring dependencies to your
pom.xml file:To configure the application as a Resource Server and validate the JWTs, create a class that will provide an
instance of
SecurityFilterChain, and add the @Configuration annotation.Protect API endpoints
The routes shown below are available for the following requests:GET /api/public: available for non-authenticated requestsGET /api/private: available for authenticated requests containing an access token with no additional scopesGET /api/private-scoped: available for authenticated requests containing an access token with theread:messagesscope granted
HttpSecurity object provided in the
filterChain() method of the SecurityConfig class. Route matchers restrict access based
on the level of authorization required.By default, Spring Security creates a
GrantedAuthority for each scope in the
scope claim of the JWT. This scope enables using the
hasAuthority("SCOPE_read:messages") method to restrict access to a valid JWT that contains
the read:messages scope.Create a new class named
APIController to handle requests to the endpoints. The
APIController has three routes as defined in the Protect API Endpoints section. For this example, allow all origins through
@CrossOrigin annotation. Real applications should configure CORS for their use case.To build and run the sample project, execute the Windows:If you are configuring your own application using Maven and the Spring Boot Maven Plugin, you can execute the
Windows:
bootRun Gradle task.Linux or macOS:spring-boot:run goal.Linux or macOS:Checkpoint
The sample application will be available athttp://localhost:3010/. Read about how to test
and use your API in the Using Your API article.
