Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Before you start
- Subscribe to an Enterprise Plan with the Adaptive MFA addon. Refer to Auth0 Pricing for details.
- Configure and enable a Database or Active Directory connection.
- Configure and enable at least one MFA factor.
Enable Adaptive MFA
You can enable Adaptive MFA in the or with the Auth0 .- Dashboard
- Management API
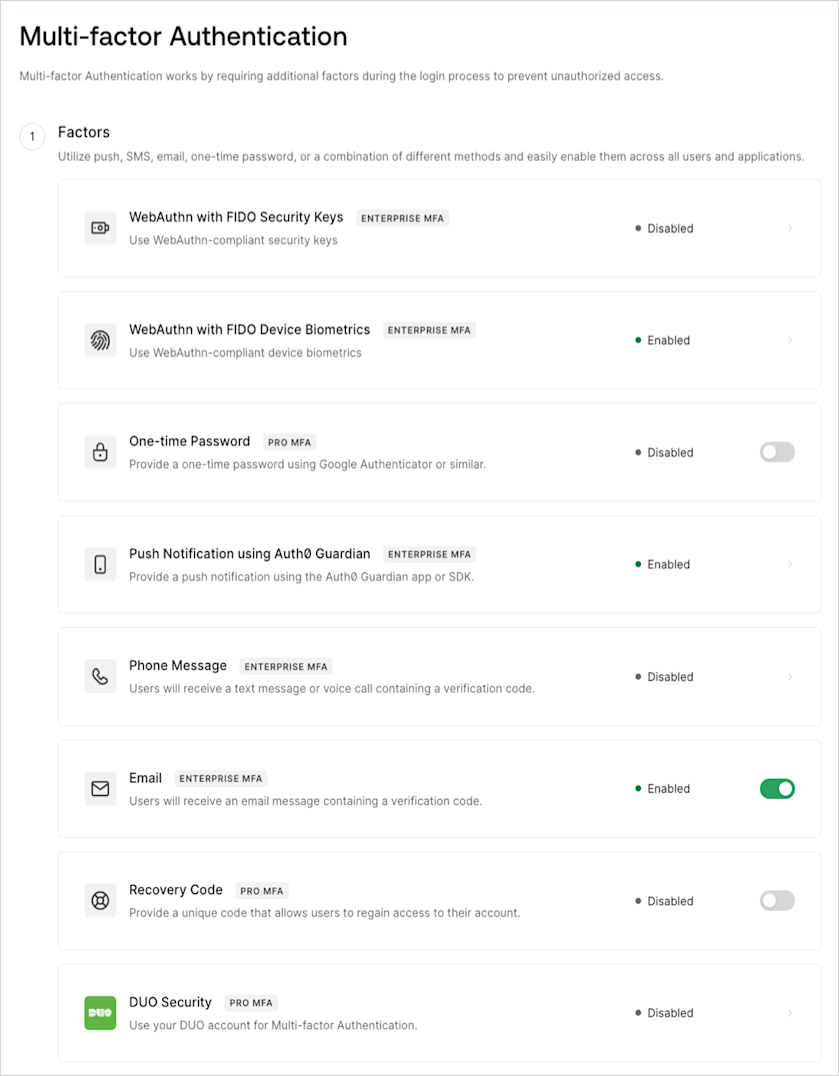
- In the Factors section, enable and configure at least one MFA Factor. To learn more, read Multi-Factor Authentication Factors.
- In the Define policies section, locate Require Multi-factor Auth, and then select Use Adaptive MFA. Risk assessment will automatically be enabled and recorded in your tenant logs.
-
In the Device Trust Duration field, set the number of days a device remains trusted before the user needs to authenticate with MFA. The default timeframe is 30 days, but you may increase or decrease the number of challenges for your users.
- You can set the trusted device duration between 1 and 365 days.
- If you modify the duration, the new duration value is applied to your users’ device the next time they log in.
- Select Save.
If you are using the Identifier First Authentication factor 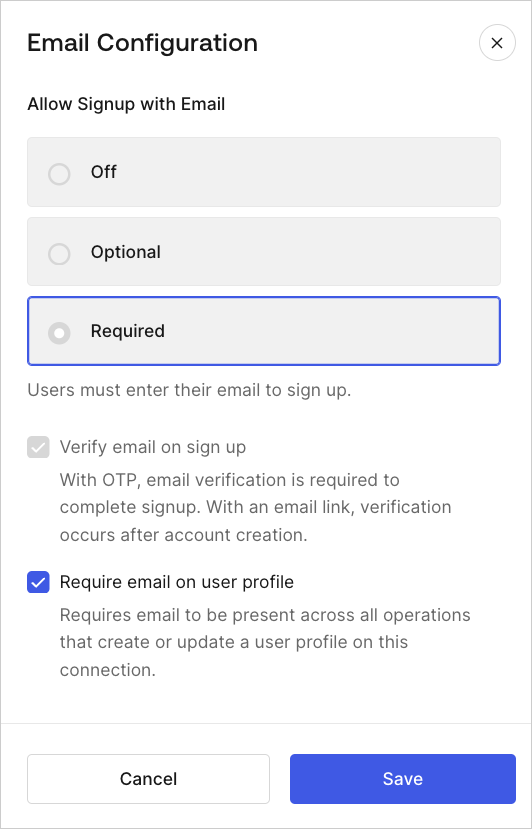
email, you must update email attributes in Dashboard > Database Connections > Authentication Methods. On the Email Configuration tab, ensure the email attribute is active. Then, set Allow Signup to Required and enable Require email on user profile.
Enable Adaptive MFA Risk Assessment
If you aren’t ready to enable Adaptive MFA, but want to start training it to analyze login behavior, you can enable Adaptive MFA Risk Assessment independently.- Go to Dashboard > Security > Multi-factor Auth.
- Locate the Define policies section.
- In MFA Risk Assessors, select Enable Adaptive MFA Risk Assessment.
- Select Save.
Customize Adaptive MFA
You can customize the behavior of Adaptive MFA to provide the best experience for your users while ensuring security. To learn more, read Customize Adaptive MFA.Actions that trigger MFA take precedence over default Adaptive MFA behavior.

