Cloud Identity and Access Management (IAM)
Understanding How Identity and Access Management in the Cloud Works

What is Identity and Access Management?
According to Gartner, Identity and Access Management (IAM) is the security discipline that enables the right individuals to access the right resources at the right times for the right reasons. IAM addresses the mission-critical need to ensure appropriate access to resources across increasingly heterogeneous technology environments.
Enterprises traditionally used on-premises IAM software to manage identity and access policies, but nowadays, as companies add more cloud services to their environments, the process of managing identities is getting more complex. Therefore, adopting cloud-based Identity-as-a-Service (IDaaS) and cloud IAM solutions becomes a logical step.
What does Cloud Identity and Access Management include?
Cloud IAM typically includes the following features:
- Single Access Control Interface. Cloud IAM solutions provide a clean and consistent access control interface for all cloud platform services. The same interface can be used for all cloud services.
- Enhanced Security. You can define increased security for critical applications.
- Resource-level Access Control. You can define roles and grant permissions to users to access resources at different granularity levels.
Why do you need Identity and Access Management?
Identity and Access Management technology can be used to initiate, capture, record, and manage user identities and their access permissions. All users are authenticated, authorized, and evaluated according to policies and roles.
Poorly controlled IAM processes may lead to regulatory non-compliance; if the organization is audited, management may not be able to prove that company data is not at risk of being misused.
How can Cloud IAM help you?
It can be difficult for a company to start using cloud Identity and Access Management solutions because they don’t directly increase profitability, and it is hard for a company to cede control over infrastructure. However, there are several perks that make using an IAM solution very valuable, such as the following:
- The ability to spend less on enterprise security by relying on the centralized trust model to deal with Identity Management across third-party and own applications.
- It enables your users to work from any location and any device.
- You can give them access to all your applications using just one set of credentials through Single Sign-On.
- You can protect your sensitive data and apps: Add extra layers of security to your mission-critical apps using Multifactor Authentication.
- It helps maintain compliance of processes and procedures. A typical problem is that permissions are granted based on employees’ needs and tasks, and not revoked when they are no longer necessary, thus creating users with lots of unnecessary privileges.
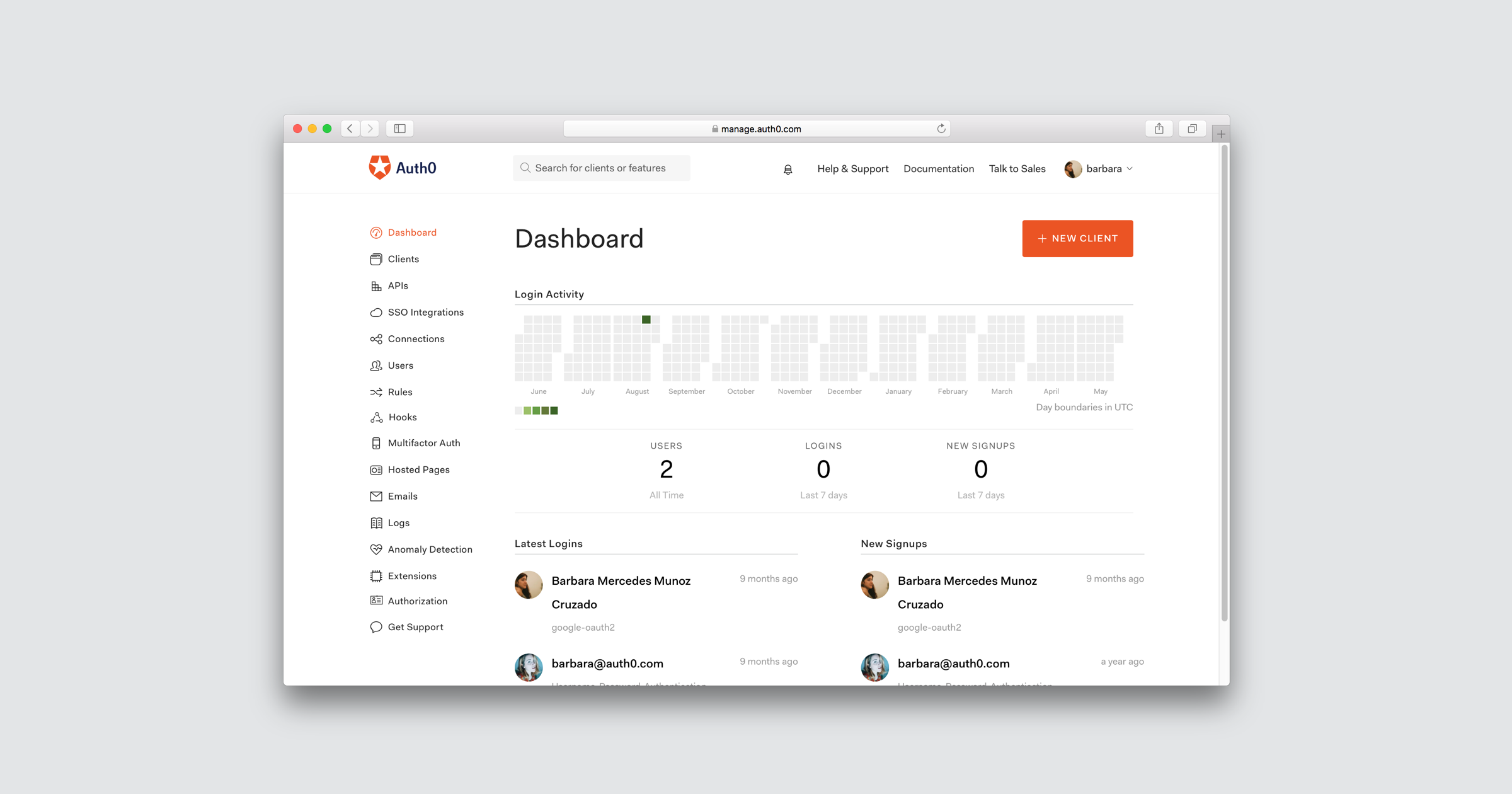
Auth0 as your Cloud IAM solution
Auth0 can authenticate your users with any identity provider running on any stack, any device or cloud. It provides Single Sign-On, Multifactor Authentication, Social Login, and several more features.
You can read more about Auth0 features here: Why Auth0?
In terms of authorization, you can use the power of the rules engine to define coarse-grained authorization — that is, rules that dictate who can login (for example: at what times, from which locations and devices, and so on).
Auth0 also has a group memberships feature that can be exposed to the application (for example: group memberships in Active Directory, in Azure Active Directory, in the user’s metadata, and so on); based on that, you can do more fine-grained authorization (where only users in a particular group can access some applications).
We are always working on improving Auth0 and making things simpler; therefore, you can expect updates in these areas soon.
Sign up for free
Start building today and secure your apps with the Auth0 identity platform today.
