Identity is a broad topic, and many resources are available. This blog post gives you a curated list of some of the most relevant resources at Auth0 by Okta and relevant identity organizations.
Identity Fundamentals
A digital identity is a set of attributes that define a particular user in the context of a function that is delivered by a specific application.
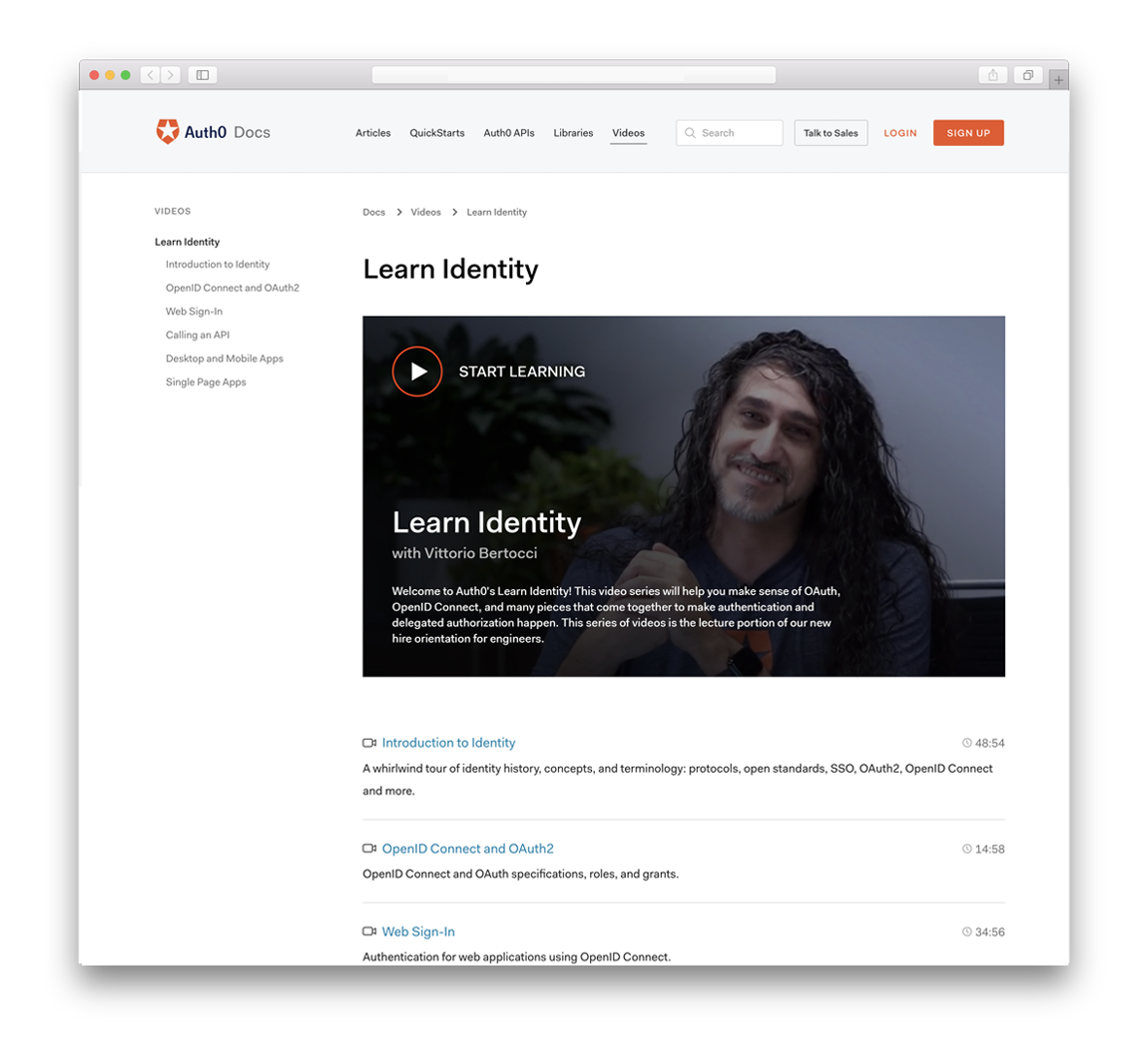
Learn it from Vittorio
Identity Fundamentals Course brought to you by the one and only Vittorio Bertocci.
IAM, CIAM, Am I?
- Identity and Access Management provides control over user validation and resource access, and it's commonly known as IAM.
- Customer Identity and Access Management (CIAM) how companies give their end users access to their digital properties as well as how they govern, collect, analyze, and securely store data for those users.
No Time? Learn Identity In a Minute
- Identity In a Minute Series is an ongoing series of 60-second shorts that describe key concepts in modern identity management, authentication, and authorization.
More Time? Learn Directly from Identity Experts
- Identity Unlocked Podcast: "Identity, Unlocked" is the podcast that discusses identity specs and trends from a developer perspective.
- Authorization in Software Podcast: "Authorization in Software" features chats with industry subject matter experts in authorization.
Authentication
In authentication, a user or application proves that they are who they say they are by providing valid credentials.
There are many ways of authentication, though. 🤔 Learn about the most common ones:
- Username and Password Authentication
- Passwordless Authentication
- SMS Passwordless Authentication
- What is Single Sign-On Authentication and How Does It Work?
For further information, we invite you to learn more about SSO with our free whitepaper.
Download the whitepaper
Authorization
Authorization is the process of giving someone the ability to access a resource.
People usually mix up Authentication and Authorization because authentication usually leads to authorization, but authorization does not always lead to authentication.
Learn more about authorization and the different types: 👇
- What Is The Right Authorization Model For My Application?
- What is Role-Based Access Control (RBAC)?
- What is Fine-Grained Authorization?
- Permissions, Privileges and Scopes - What's the Difference?!
2FA, MFA all-the-FA
There are many options you can use to prove your digital identity. These are called authentication factors, and there are three main types:
- knowledge or something that you know, like a password,
- possession or something that you have, like a device
- inherence, which is something that you are or is inherent to you.
Usually, your application requires only one authentication factor to authenticate a user, typically a password. In some contexts, you may want more assurance about the user's identity. In that case, you can require two or more authentication factors. That's what two-factor authentication (2FA) and multi-factor authentication (MFA) are all about.
Learn more about 2FA and MFA 👇:
- Two-Factor Authentication (2FA)
- The Working Principles of 2FA (2-Factor Authentication) Hardware
- The Working Principles of 2FA (2-Factor Authentication) Software
- 2FA Using Biometrics
- Getting Started with Multi-Factor Authentication
OAuth2, OIDC, Oh-what?
There are many standards used for identity. Some of the most relevant are OAuth2 and OIDC. OAuth 2.0, which stands for "Open Authorization", is a standard designed to allow a website or application to access resources hosted by other web apps on behalf of a user. At the same time, Open ID Connect (OIDC) is an authentication protocol that utilizes the authorization and authentication mechanisms of OAuth 2.0.
But what else is out there? Learn more here 👇
- OAuth 2.0 Simplified
- OAuth 2.0 and OpenID Connect (in plain English)
- OAuth in Five Minutes
- An Illustrated Guide to OAuth and OpenID Connect
- OIDC Playground
- SAML Authentication: you can also use samltool.io's playground to learn more
Want to get up to speed with OAuth2 and OpenID Connect?
Download the free ebook
Tokens, tokens, and more tokens!
A token is a piece of data that has no meaning or use on its own but, combined with the correct tokenization system, becomes a vital player in securing your application. There are different tokens, but what does each one do? How do you use them?
- ID Tokens VS Access Tokens: What's the Difference?
- What are Refresh Tokens?! and...How to Use Them Securely
- Token-based Authentication Made Easy
- JSON Web Tokens
- JWT.io
Interested in getting up-to-speed with JWTs as soon as possible?
Download the free ebook
WebAuthn
WebAuthn is a W3C recommendation for defining an API enabling the creation and use of strong, attested, scoped, public key-based credentials by web applications to authenticate users strongly. Here are some great resources to learn more:
 Want to learn more about WebAuthn?Visit → webauthn.me
Want to learn more about WebAuthn?Visit → webauthn.mePasskeys
Passkeys are password replacements that provide a faster, easier, and more secure user login experience that leverages WebAuthn under the hood. Learn more about passkeys:
About the author

Carla Urrea Stabile
Staff Developer Advocate
I've been working as a software engineer since 2014, particularly as a backend engineer and doing system design. I consider myself a language-agnostic developer but if I had to choose, I like to work with Ruby and Python.
After realizing how fun it was to create content and share experiences with the developer community I made the switch to Developer Advocacy. I like to learn and work with new technologies.
When I'm not coding or creating content you could probably find me going on a bike ride, hiking, or just hanging out with my dog, Dasha.