Modern applications face a contradictory set of requirements and are being pushed in every direction at once, while having to balance security, privacy, and user experience. They are expected to maximize conversion and personalization while simultaneously defending against increasingly sophisticated automated threats. Usually, engineering teams treat these as separate workstreams: a growth team handles the UI, while a security team manages the perimeter.
This separation fails when you introduce AI. When autonomous agents start interacting with your data, the "perimeter" disappears. The only thing left to govern the system is identity.
In most legacy architectures, identity was a "check the box" feature: a login page and a database of hashed passwords. But in a product ecosystem where AI agents can act on behalf of users, identity has to move from the edge of the stack to the core of the product architecture.
If you don't know exactly who or what is performing an action, and the specific context that allows it, you aren't building an AI experience; you're building a liability.
In this article, we’ll look at how identity has shifted from a feature to a core part of product architecture, and why it’s becoming the foundation for building trusted AI experiences.
Identity Is Now Part of Your Product Architecture
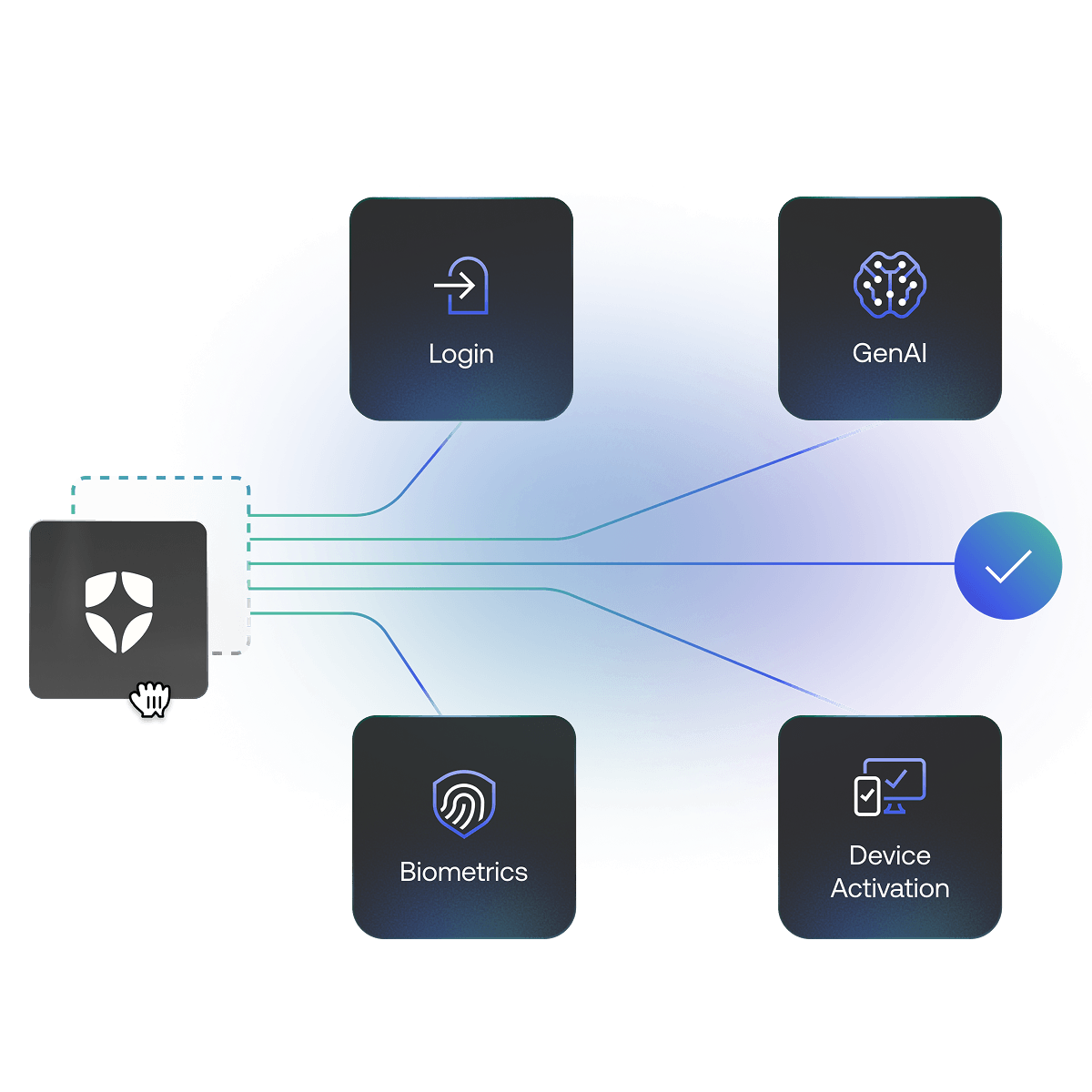
Traditionally, identity was a wrapper. You built an app, then "added auth." This led to a fragmented reality where identity logic lived in different places: some in the gateway, some in the microservices, and some hard coded into the frontend.
When identity is fragmented, your product slows down. Not because your code is bad, but because your "source of truth" is scattered. A user might be authorized to view a resource in the web app but blocked by a stale policy in the API. These inconsistencies create "identity debt" that makes it impossible to ship new features quickly.
In modern architecture, identity functions as a shared system. It provides a consistent way to handle authentication (is this person who they say they are?) and authorization (what are they allowed to do right now?). By centralizing this, you move the complexity out of the individual services and into a dedicated layer. This allows your developers to focus on building features rather than duct-taping OAuth flows.
Why Identity Directly Impacts Growth, Not Just Security
When growth slows, it’s often framed as a product or marketing problem. Conversion drops, engagement fades, or expansion takes longer than expected. But in many cases, the issue sits deeper in the system. It shows up in how users enter, move through, and return to your product.
Conversion
The first interaction is the most fragile. If your onboarding flow requires too much manual input or forces a password reset before a user has even seen the product value, they leave.
Modern identity allows for progressive profiling and gathering data only when it’s needed. By using social logins or passkeys, you reduce the time-to-value. More importantly, identity provides the initial "who" that allows you to tailor the very first screen a user sees.
Retention and engagement
Users don’t think in terms of sessions or systems. They expect continuity. If they start a workflow on a mobile device and finish it on a desktop, they shouldn't feel like they’re interacting with two different companies.
When identity isn't integrated into the architecture, context gets dropped. Sessions expire too early, or preferences don't sync. A unified identity layer enables the "user state" to be persistent across every touchpoint, which is the actual requirement for high retention.
Expansion
For B2B platforms, the "expansion" phase usually involves moving from a single user to an entire organization. This requires more than just basic login; it requires robust multi-tenancy and sophisticated governance.
If your identity system can't handle complex organizational hierarchies or "bring your own identity" (BYOID) for enterprise customers, your sales team will hit a wall. Scaling trust with an enterprise buyer means proving you can enforce their specific security policies across their entire tenant without breaking their workflow.
When identity is a core architectural pillar, multi-tenancy isn't a "hack" layered on top of a database; it’s a hard boundary that enables data isolation while allowing for flexible, attribute-based access at scale.
AI Changes the Rules as Identity Now Has to Govern Machines
The rise of agentic AI that can take actions, not just summarize text, creates a massive security gap. Traditional identity models were built for human sessions that last for a few hours and involve a human clicking a button.
AI agents don't work like that.
Actions are no longer tied to sessions
An AI agent might trigger a sequence of events that lasts for days. It might call five different microservices to complete a single task. If your security model relies on a temporary browser cookie, it won't work.
You need a way to issue "scoped" credentials to an agent that are tied back to the original human intent but restricted in what they can actually execute. This is where Non-Human Identity (NHI) management becomes the most important part of your stack.
Access decisions need to happen in real time
In an agentic world, permissions cannot be static. You can't just give an AI "admin" rights and hope for the best. Access decisions must be evaluated at the moment of request.
Traditional Role-Based Access Control (RBAC) is too blunt for this. Assigning an agent a "manager" role is a massive over-privilege; it gives the AI access to everything a manager can see, all the time. Instead, the system needs to understand the relationship between the actor, the action, and the specific resource.
This requires a shift to continuous authentication. The system should check the dynamic context of the request:
- Is the agent asking for more data than it needs for this specific sub-task?
- Is this request happening at an unusual frequency?
- Does this specific agent have a proven relationship to this specific row of data for this specific tenant at this exact moment?
If identity is built into the architecture, the system doesn't just check a static "role" in a database; it evaluates the live relationship. The moment an anomaly is detected or a relationship boundary is crossed, the system can kill the session instantly.
Attribution becomes a requirement, not a feature
When an AI agent makes a mistake or a malicious actor manipulates one, you need a deterministic audit trail. You have to be able to answer:
- Which model made this request?
- Which user authorized the agent to act?
- What specific policy allowed this data access? Without a centralized identity layer, these questions are unanswerable. Identity provides the "provenance" for every action taken by an AI.
How Identity Architecture Impacts Specific Industries
These architectural shifts move from theory to technical debt quickly. When authorization logic is fragmented across services, it creates inconsistencies in how products behave, especially as systems become more distributed and AI agents are introduced.
Retail
In retail, identity sits directly in the path of conversion, making it the difference between a "generic" store and a personalized concierge. If a customer is recognized across web, mobile, and in-store, the retailer can provide a single, unified cart.
However, if an AI shopping assistant is introduced, that assistant needs limited access to the user's payment info, enough to check out, but not enough to change the delivery address or view the entire order history. Identity handles that scoping.
Financial services
In financial services, identity decisions happen constantly, and the margin for error is smaller. Users expect fast onboarding and smooth access, but also strong protection when actions become sensitive.
Trust in fintech is built on the "step-up" experience. You don't need a fingerprint scan to check your balance, but you definitely need it to transfer $10,000. Modern identity architecture allows for "risk-based authentication," where the system only adds friction when the risk warrants it.
When AI is used to automate trading or fraud detection, identity confirms that those automated agents are operating within strict legal and regulatory boundaries.
Healthcare
In healthcare, identity is tightly tied to trust and privacy, and the stakes are highest there.
Patient data must be "siloed" but accessible to the right providers at the right time. When AI is used to analyze lab results, the identity layer confirms that the AI only sees the specific records it needs for that analysis (the principle of least privilege) and that the patient's consent is verified in real time before the data is decrypted.
B2B SaaS platforms
In SaaS environments, identity complexity increases quickly.
You’re not just managing users, but organizations, roles, permissions, and increasingly, AI features embedded directly into workflows. Agents may act on behalf of users, trigger actions across systems, or interact with external services.
Basically, B2B SaaS is moving toward "multi-tenant" AI. This means your AI features are processing data for thousands of different companies simultaneously. The biggest risk is "cross-tenant" data leakage. A strong identity architecture confirms that the AI agent working for Company A can never, under any circumstances, "see" the data from Company B, even if they are using the same underlying LLM.
How to operationalize identity
Moving identity from a peripheral feature to a core architectural component is a significant engineering shift. Most teams fail here because they treat identity as a one-time integration task rather than an ongoing operational discipline.
Decouple policy from code
The most common mistake in product architecture is embedding authorization logic directly into the application code. When you have if (user.role == 'admin') scattered across your microservices, you’ve created a maintenance nightmare. To operationalize identity, you must decouple policy from the underlying business logic.
By moving toward an externalized authorization service, specifically one built for Relationship-Based Access Control (ReBAC), you allow security and product teams to dynamically update access rules in real-time.
Instead of redeploying code to change a permission, you simply update the relationship graph. This confirms that as your AI agents evolve, your security posture evolves with them, without touching a single line of microservice logic.
Solve the token exchange problem
In a distributed system, especially one involving AI agents, the "identity" of the actor often changes as it moves through the stack. A user logs in (User Context), triggers an AI agent (Service Context), which then calls a database (Resource Context).
Operationalizing this requires a robust token exchange pattern. You cannot simply pass the user’s original JSON Web Token (JWT) through the entire chain; it’s a massive security risk and provides too much broad access. Instead, your architecture must support token downscoping, where each hop in the request chain receives a token with the absolute minimum scope required to perform its specific task.
Automate the lifecycle of NHIs
If your plan for AI agents involves creating a service account and saving the API key in a secret manager, you aren't operationalizing; you're just creating a back door.
NHIs require the same (or stricter) governance as human users. This means:
- Automatic rotation: Keys and secrets should expire and rotate without human intervention.
- Behavioral monitoring: Because agents don't have "normal" office hours, you need to establish a baseline of "normal" behavior. If an agent suddenly requests a bulk export of a database, it usually only queries for single rows; the identity layer should automatically revoke its credentials.
- Attribution mapping: Every NHI must be mapped to a "human-in-the-loop" or a specific service owner. When an agent malfunctions, you shouldn't be hunting through logs to find out who created it.
Build for "day two" operations
Most identity projects focus on "Day One": getting the user to log in. Operational excellence is about "Day Two": what happens when a user loses their physical MFA key? What happens when a customer’s tenant needs to be migrated to a different region with different data residency laws?
Operationalizing identity means building the "plumbing" for these edge cases early. This includes centralized logging that feeds into your Security Information and Event Management (SIEM), self-service recovery flows that don't rely on manual helpdesk tickets, and a "kill switch" capability that can revoke all sessions for a compromised organization across every one of your services instantly.
Identity is how you scale trust
As applications move from "tools we use" to "agents that act for us," the margin for error disappears. Without a relationship-aware identity layer, a simple prompt like "summarize my team's performance" could grant an agent access to every salary and private HR file in the company.
A single misconfigured permission or over-scoped token is no longer a minor bug; it’s a massive vulnerability. Complexity is the enemy of security. When identity logic is spread across twenty different services, you have twenty different places to fail.
By treating identity as a core architectural layer, you do more than just lock the door. You create a system that is consistent, traceable, and scalable. You give your teams the freedom to build aggressive AI features because you know the underlying identity framework will keep those features within their boundaries.
Every interaction, whether it’s a human clicking a link or an AI agent calling an API, starts with the same fundamental question: "Who is this, and what are they allowed to do?" Answering that question correctly, every single time, is the only way to build a product people actually trust.
Want a deeper look at how identity supports AI, growth, and trust?
Explore Secure every interaction: A leader’s guide to identity in an agentic world.
About the author

Saad Rahman
Staff Product Marketing Manager, Auth0 Solutions