You can configure a connection to send a Magic Link to a user through email to complete authentication. To learn more, read Configure Email or SMS for Passwordless Authentication.Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
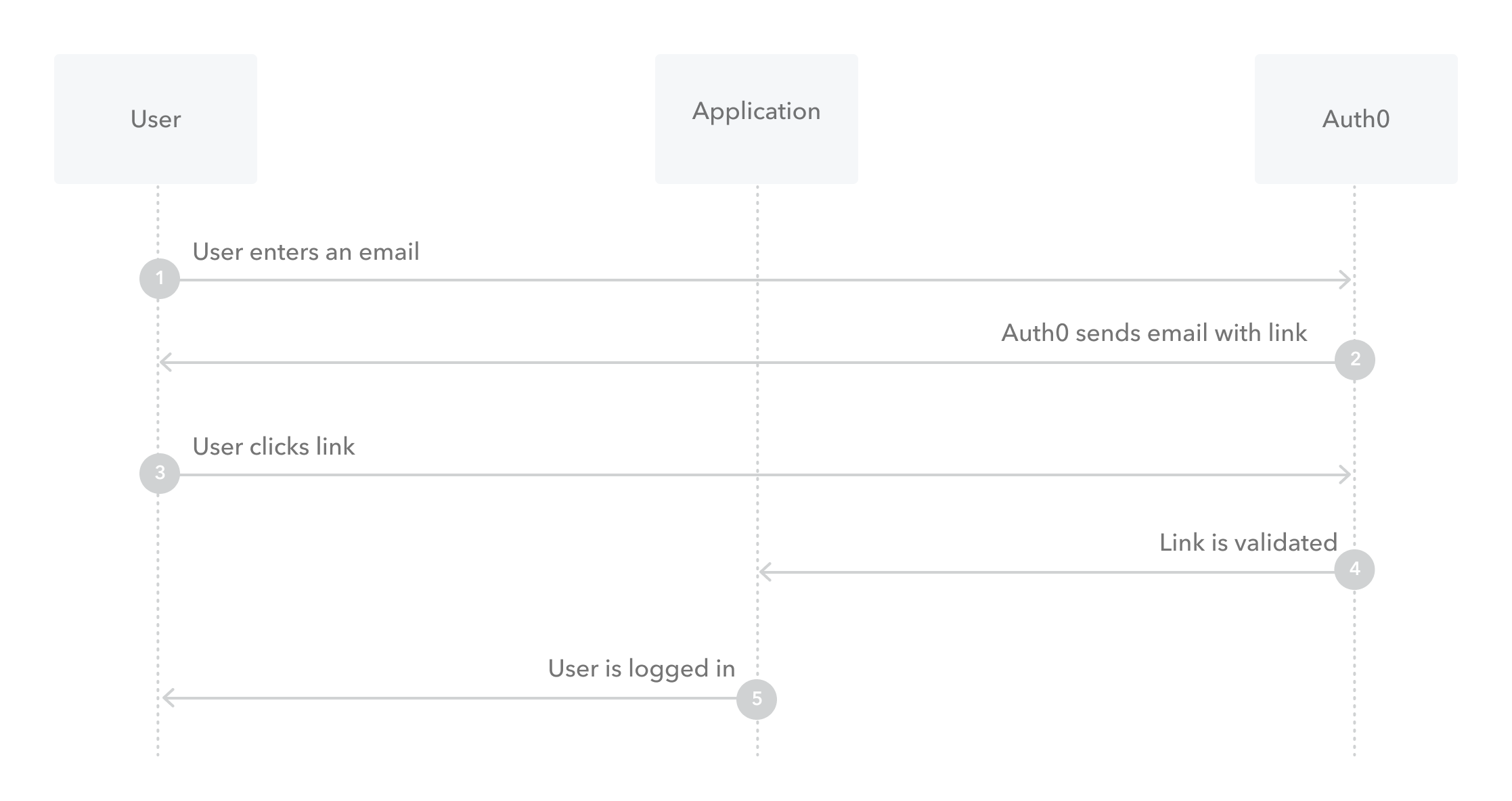
How it works
When a user opens a Magic Link, Auth0 logs them in directly. It is similar in function to them receiving an email with a one-time password (OTP), returning to your application, and entering the OTP, but without having to actually perform those steps.Limitations
Magic Links are not supported for . When using Magic Links with Classic Login, both the initial request and its response must take place in the same browser or the transaction will fail. This is particularly relevant for iOS users, who cannot change their default web browser. For example, the user might make the initial request using the Chrome browser, but when the user opens the Magic Link in their email, iOS automatically opens it in Safari (the default browser). If this happens, the transaction will fail.Classic Login flow with Magic Links
Configure the connection
- In the Auth0 Dashboard, go to Authentication > Passwordless, and then enable the Email toggle.
-
Select Email to open the configuration window, switch to the Settings view, and enter your email’s From, Subject, and Message text.
You must change the From value to an email address that does not use the
auth0.comdomain for Auth0 to send your custom email templates. If you do not, Auth0 sends the default email template. - Enter any Authentication Parameters you would like to include in the generated sign-in link.
- Decide if you want to Disable Sign Ups. If you enable this setting, you can allow passwordless access for only existing users, but may expose your application to the threat of user enumeration attacks. To learn more, read Passwordless Connections Best Practices.
- Select Save.
Multi-language support
The Message area supports multiple languages. To specify a language, call the Auth0 Authentication API Get Code or Link endpoint and set the value of thex-request-language header. When this header is not set, the language is extracted from the accept-language header, which is automatically set by the browser.
Message syntax
The Message area accepts Liquid syntax. You can use this syntax, combined with parameter values, to programmatically construct elements of the message. For example, you can reference therequest_language parameter to change the language of the message:
| Parameter | Description |
|---|---|
code | The password to use. |
link | The generated sign-in link. |
application.name | The name of the application with which the user is signing up. |
request_language | The requested language for message content. |
operation | Indicates when the template has been triggered by an update to a user’s email through the API. When triggered, the value is change_email, otherwise it is null. |
Update Classic Login settings
If you are using Classic Login for your application, you must update the page template to implement Magic Links.- In the Auth0 Dashboard, go to Branding > Universal Login > Advanced Options.
- Switch to the Login view, locate the Default Templates dropdown, and select Lock (passwordless).
-
Next, update the
Auth0LockPasswordlesssection of code with a new parameter. Add thepasswordlessMethodto your template. - Select Save.

