Documentation Index
Fetch the complete documentation index at: https://auth0.com/llms.txt
Use this file to discover all available pages before exploring further.
Before you start
To use Back-Channel Logout, your application must meet the following requirements:
- Your OIDC Back-Channel Logout URI endpoint must be exposed over the internet for your Auth0 tenant to access.
- Production-ready applications must use TLS. To learn more, read TLS (SSL) Versions and Ciphers.
- The application must be able to store the provided session identifier (
sid) and associate it with the user sessions it creates. We recommend production applications use durable session storage. - The application must be able to retrieve an existing session by the
sidduring the logout process without using client-side cookies. Cookies exist within the browser and are inaccessible to the logout callback endpoint.
Availability
OIDC Back-Channel Logout is available for all Enterprise plan customers. You should check the OIDC standard/.well-known/* metadata endpoint to determine if your application meets the requirements.
Back-Channel Logout restrictions
Back-Channel Logout URLs are called on publicly-exposed endpoints and must adhere to certain restrictions:- You must use the HTTPS protocols. Unencrypted HTTP or other protocols are not permitted.
-
You must not use Auth0 subdomains. Some Auth0 subdomains are:
- auth0.com
- auth0app.com
- webtask.io
- webtask.run
- We do not recommend using IP addresses without domains. IP addresses must be public IPs to use Back-Channel Logout. IP addresses from internal, reserved, or loopback ranges are not permitted.
Configure Auth0
Register your application to receive Logout Tokens via or .- Auth0 Dashboard
- Management API
Subscribe applications
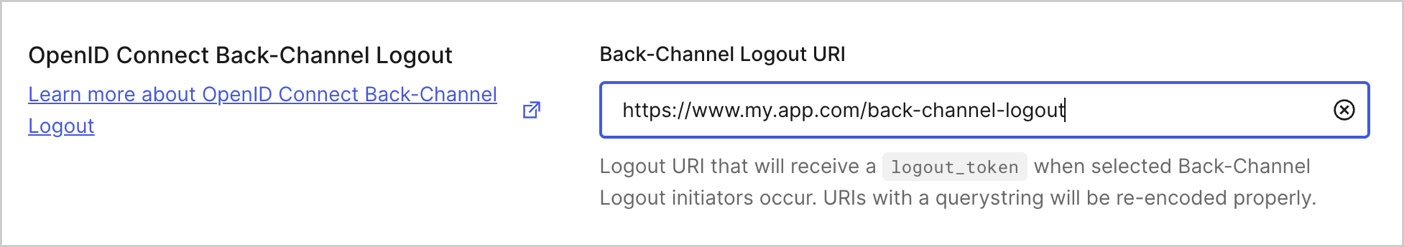
- Navigate to Auth0 Dashboard > Applications.
- Choose the application you want to register.
- Select the Settings tab.
- Under the OpenID Connect Back-Channel Logout > Back-Channel Logout URI, add the application logout URI that will receive the logout_tokens
-
Once complete, select Save Changes.
Unsubscribe applications
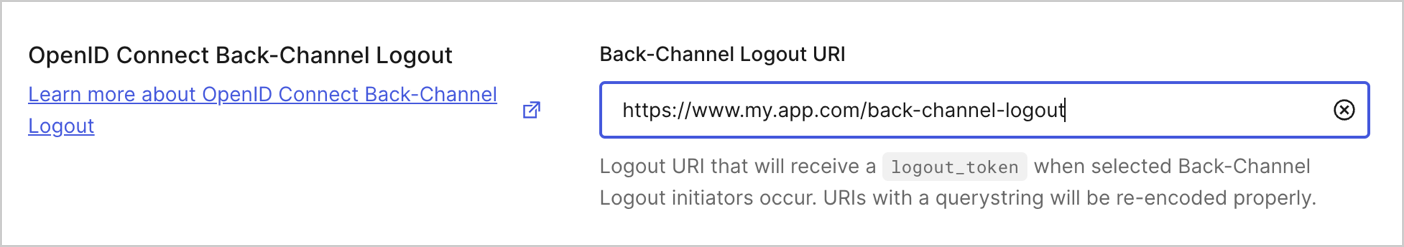
Unsubscribing your application stops the service from tracking new logins and sending logout events. The service discards pending logout events once your application is unsubscribed.To unsubscribe your application, delete the back-channel logout URL.- Navigate to Auth0 Dashboard > Applications.
- Choose the application you want to register.
- Select the Settings tab.
- Under the OpenID Connect Back-Channel Logout > Back-Channel Logout URI
- Remove the back-channel URL.
-
Once complete, select Save Changes.
API Operation Event in Auth0 tenant logs. To learn more, read Logs.Configure your application
Once you have configured Back-Channel Logout via the Auth0 Dashboard or Management API, configure your application to use the service based on the technology or framework.-
Implement end-user authentication according to your application type.
- End-users should be able to log in to the application, and a session should be created.
- An ID token should be issued from Auth0 and should be accessible in the application backend for further processing.
-
Extend the login process to save the
sidand, optionally, sub claims after the ID token is validated.- These claims must be saved against the current application session.
- The session management functions should be able to retrieve a specific session by the
sidvalue.
-
Configure the Back-Channel Logout endpoint:
- The endpoint must process only
HTTP POSTrequests. - Extract the
logout_tokenparameter and validate it as a regular JWT according to the spec. - Verify that the token contains an events claim with a JSON object value and a member named
http://schemas.openid.net/event/backchannel-logout. - Verify that the token contains the
sidand/orsubclaims. - Verify that the token does NOT contain the
nonceclaim. This is required to prevent abuse by distinguishing the Logout Token from the ID token. - Once the token is validated, retrieve the session corresponding to the received
sidand/orsubvalue and terminate it. The exact application session termination process depends on the implementation details. For example, this event may need to be communicated to the front-end.
- The endpoint must process only
OIDC Back-Channel Logout request example
Coded token payload:cURL
Token expiration is 2 minutes (120 sec).
JSON
Expected responses
- HTTP 200: Confirms user logout from the specific application.
- HTTP 400: Indicates an incorrect request. The request is not understood or the token failed validation. Auth0 records the problem in tenant logs but does not attempt further requests for this specific session.
Troubleshoot issues
Application did not receive the logout events
If your application did not receive a logout request after a logout event.- Make sure your application has a Back-Channel Logout URL registered in Auth0 Dashboard.
- Ensure the Back-Channel Logout URL is reachable from the Auth0 tenant.
-
Ensure a valid session is established. The end-user must log in to your specific application via Auth0.
Applications receive logout events only if end-users log in to that specific app with Auth0. If the end-user logs in to other applications, logout events do not trigger.
- Check Auth0 tenant logs for messages about unsuccessful logout message delivery.
- Make sure the logout is triggered via the standard logout endpoint. Other events do not trigger the logout events.
- If possible, check for blocked requests on the web server and/or application firewall logs.
I can’t find OIDC Back-Channel Logout tenant logs
This feature will be gradually released to all tenants starting 3 October 2023. You may still receive tenant log event codessslo for oidc_backchannel_logout_succeeded or fslo for oidc_backchannel_logout_failed.
Client app cannot verify the received Logout Token
If the transaction still fails with a 400 error:- Check if the token is a standard base64-encoded JWT. Some web servers may truncate long parameters. To learn more, read Signing Algorithms.
- If possible, capture a token and verify that it’s a JWT. Use a verified source, like JWT.IO.
-
Make sure the verification function fetches the tenant signing key dynamically via JSON Web Key Sets (JWKS).
We do not recommend hardcoding a static key. If your configuration requires the static key to be hardcoded, ensure the configuration contains the latest public key from the Auth0 tenant.

