Chances are, if you're a B2B SaaS company (whether you're a large, established firm like Microsoft or an up-and-comer like Slack) — you're focused on being up to speed on the latest security tools.
For teams of all sizes, however, it can be a challenge to keep up in a rapidly evolving threat environment. How do you ensure that your team has a safe foundation on which to scale?
Building your security practices around the starting point of understanding and managing all of your users can help ensure that you always have a handle on who is working within your system and with confidential information. When crafted well, a robust identity and access management (IAM) system for your users can be a springboard for moving forward.
“When crafted well, a robust identity and access management (IAM) system for your users can be a springboard for moving forward.”
Tweet This
What Is Identity and Access Management (IAM)?
According to Gartner, "Identity and access management (IAM) is the security discipline that enables the right individuals to access the right resources at the right times for the right reasons." As teams become more dispersed and users are logging in across multiple time zones and various devices, IAM practices have emerged to organize and control appropriate access.
Historically, when teams were largely on site, enterprises simply used their own IAM software. Nowadays, as companies add more cloud services, managing access is becoming increasingly complex. For IT teams that are already swamped with maintenance tasks, outsourcing cloud-based Identity as a Service (IDaaS) and cloud IAM solutions is becoming more popular.
Identity Management: To Build or To Buy?
While you might have the in-house capacity to build your own identity and access management system, most teams don't. Even if you do, going with a DIY solution is often less cost-effective.
In today's environment, an effective IAM solution should
- provide a clear and centralized view of all users at a given time;
- give an admin quick controls to communicate with, manage the access of, and even block users;
- be powerful yet still flexible to grow with your company; and
- help you comply with the latest security regulations.
Asking yourself the following questions will help you determine whether it's time to outsource your IAM:
- Have you thought about how you’ll implement user management (e.g., self-service or admin managed?
- How will the user experience your solution?
- What analytics will you need for account creation and authentication events?
- How will you use your system to stay on top of potential security vulnerabilities?
- How will you flag and mitigate anomalies in user management and authentication events?
- How will you onboard new B2B customers wanting SSO for your product or service?
For an even more comprehensive checklist, see Auth0's guide.
Use Auth0 Lock for Simple, Secure Access
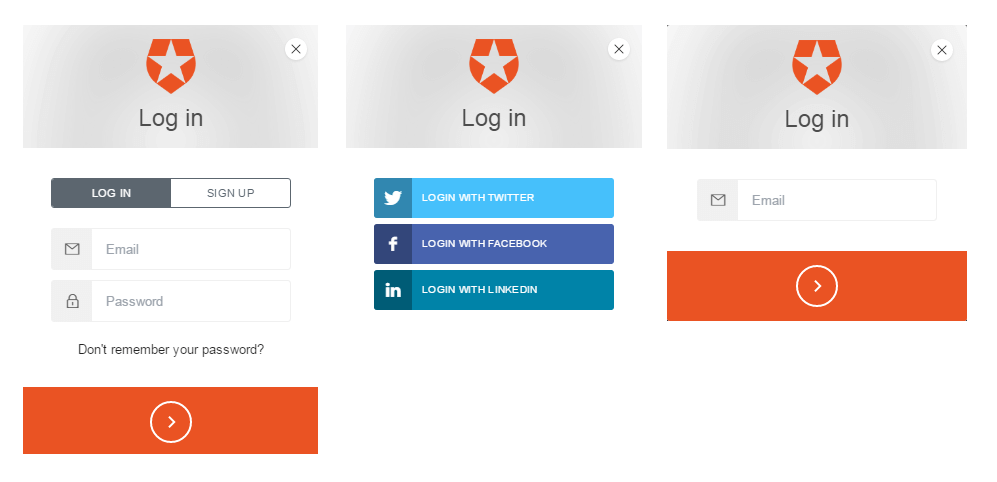
An example of a highly successful tool that has worked for a range of growing software companies, more established enterprise-scale companies, and even nonprofits is the Auth0 Lock. Auth0 Lock connects the login boxes of all users (i.e., both employees and customers) via a single, embeddable widget.
Instead of having multiple login boxes for each category of users, which can add a layer of complexity to the admin process, entrance with Auth0 Lock is streamlined for all. Given distinct usernames and passwords, IT admins are easily able to differentiate between users as soon as they've logged in — and can view all activity at one time, from a central hub. Separate login credentials will usher users to different sites that suit their work needs. For example, if you're in hiring mode, prospects can log in to fill out applications as easily as your finance team can update their records.
Once Auth0 Lock is implemented, your company can add features like social login and single sign-on (SS0) to further secure and enhance the UX of authentication. It's simple to customize Lock based on your company's needs and how you want the experience to be for your users.
The Power of Auth0 Connections
Auth0 sits between your app and the Identity Provider (like Twitter and Facebook, or enterprise providers like Active Directory and LDAP) that authenticates your users. Auth0 Lock is just one tool of many that will help secure this connection.
Auth0 supports over 30 social providers, 11 enterprise providers, and three legal identities. It adds a level of abstraction to your app to help isolate it from disruptive updates or idiosyncrasies of each provider's implementation. For example, as Facebook rolls out new privacy standards, any technical updates on their end that could change the login process for your users will be internalized and streamlined.
If You're Still Unsure About Outsourcing Your Identity Management Needs, Consider Compliance
More than simply creating a safer and easier UX, Auth0 can help B2B SaaS teams comply with increasingly stringent security regulations. A specialized provider like Auth0 can become a one-stop shop for adhering to GDPR and similar laws.
“More than simply creating a safer and easier UX, Auth0 can help B2B SaaS teams comply with increasingly stringent security regulations.”
Tweet This
Auth0 tools incorporate
- encryption;
- password protection; and
- five levels of password complexity.
In addition, Auth0 consolidates all of your user data into a single dashboard view, making it simpler to communicate processes to stakeholders — a core tenant of GDPR.
Auth0 is a team of experts, focused on the specific task of authentication and user management 24/7. The company is up to date on all of the latest security developments and rapid changes in the industry. We monitor for new threats and adapt our tools accordingly for B2B SaaS companies at all stages of growth.
About the author

Martin Gontovnikas
Former SVP of Marketing and Growth at Auth0 (Auth0 Alumni)
Gonto’s analytical thinking is a huge driver of his data-driven approach to marketing strategy and experimental design. He is based in the Bay area, and in his spare time, can be found eating gourmet food at the best new restaurants, visiting every local brewery he can find, or traveling the globe in search of new experiences.View profile